- Cyber threats are increasingly elevating data and infrastructure risks for state and local governments. Proactive security standards and assessments can strengthen governmental defenses.
- Cyber Maturity Assessments (CMAs) evaluate preparedness to safeguard against, detect, isolate, and respond to system threats holistically across staff, procedures, and tools.
- Conducting a CMA can provide governments strategic advantages, such as: gauging risk management capabilities, fostering a security culture, mapping regulatory requirements, adapting to the evolving threat landscape, and informing cybersecurity strategies.
~
Cyber threats grow more sophisticated every day, increasing risks to sensitive data and critical services at the state and local level. With public-sector cyberattacks on the rise, today’s governments need to reinforce their cyber defenses to protect government operations and maintain constituent trust.
In the realm of cybersecurity, staying ahead of the curve is not just advisable; it’s imperative. In 2016, the Department of Defense (DoD) introduced a final rule amending the Defense Federal Acquisition Regulation Supplement (DFARS). This rule mandated new cybersecurity safeguards and cyber incident reporting for controlled unclassified information (CUI).
Transitioning from DFARS, the DoD has now developed the Cybersecurity Maturity Model Certification (CMMC), a framework designed to enhance the cybersecurity of government contractors. While state and local governments are not beholden to the CMMC, your team can still benefit from embracing CMMC standards and proactively developing comprehensive security programs.
5 Benefits of a Cyber Maturity Assessment for Your State or Local Government
To check your government against CMMC standards, a powerful tool you can employ is a Cyber Maturity Assessment (CMA) — which examines your organization’s overall preparedness to safeguard against, recognize, isolate, and react to cyber threats that could compromise sensitive data and systems. Analyzing more than just adherence to regulations, a CMA is a holistic analysis of people, processes, and tools that assesses the entity’s broader cyber risk exposure and defenses.
Here are five ways a CMA can be a trusted ally in fortifying your cybersecurity defenses:
1. Risk Management
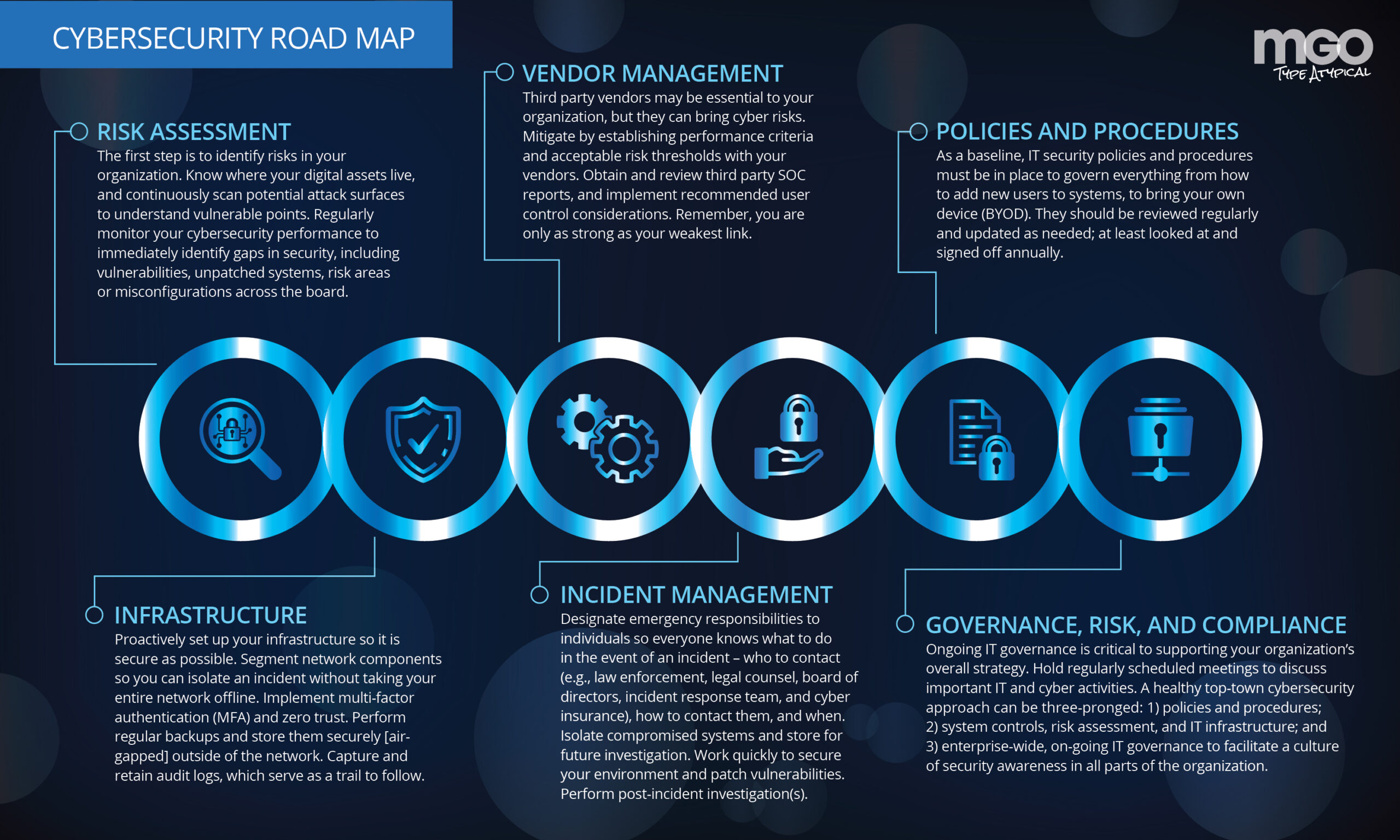
The CMA framework addresses the crucial question: Is your organization equipped to navigate evolving risks effectively? With the assistance of CMA, state and local governments can gain insights into the maturity of their current processes and mechanisms. This empowers them to make informed decisions on risk mitigation strategies, ensuring a robust defense against emerging cyber threats.
2. Strengthening Security Culture
Promoting a culture of security and privacy by design is paramount in today’s digital landscape. CMA serves as a catalyst in fostering this mindset within organizations. By assessing the maturity of security practices, it enables state and local governments to identify areas for improvement, laying the foundation for a resilient security culture.
3. Understanding of Multiple Regulatory Requirements
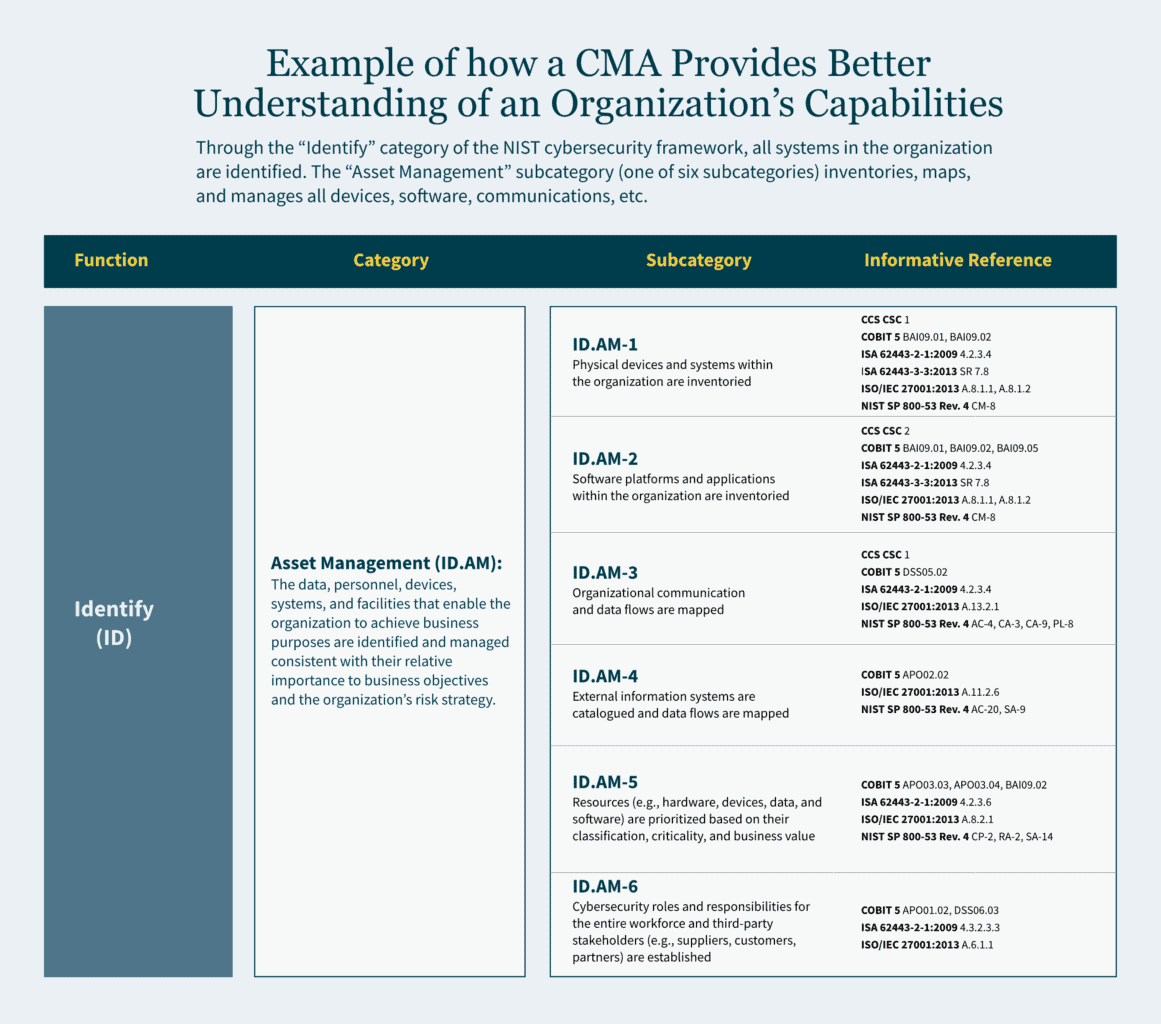
Navigating the complex web of regulatory requirements is a challenge for any government entity. CMA provides a comprehensive understanding of an organization’s capabilities to meet controls-based regulatory requirements. This not only ensures compliance but also establishes a framework for efficient regulatory adherence, minimizing vulnerabilities.
4. Proactiveness in an Ever-Evolving Cybersecurity Landscape
As cyber threats continue to grow in scale and sophistication, organizations must be proactive in adapting to the evolving landscape. CMA equips state and local governments with the foresight needed to stay ahead of cybercriminals. By identifying potential threats and vulnerabilities, organizations can implement strategies to drive growth and transformation while safeguarding their digital assets.
5. Determining Considerations for a Cybersecurity Strategy
Crafting an effective cybersecurity strategy requires a deep understanding of an organization’s capabilities and potential areas for improvement. CMA assists in identifying key considerations for a cybersecurity strategy, ensuring that state and local governments can rapidly adapt to the dynamic cybersecurity landscape.
Employing a Methodical Approach to CMA that Delivers Actionable Insights
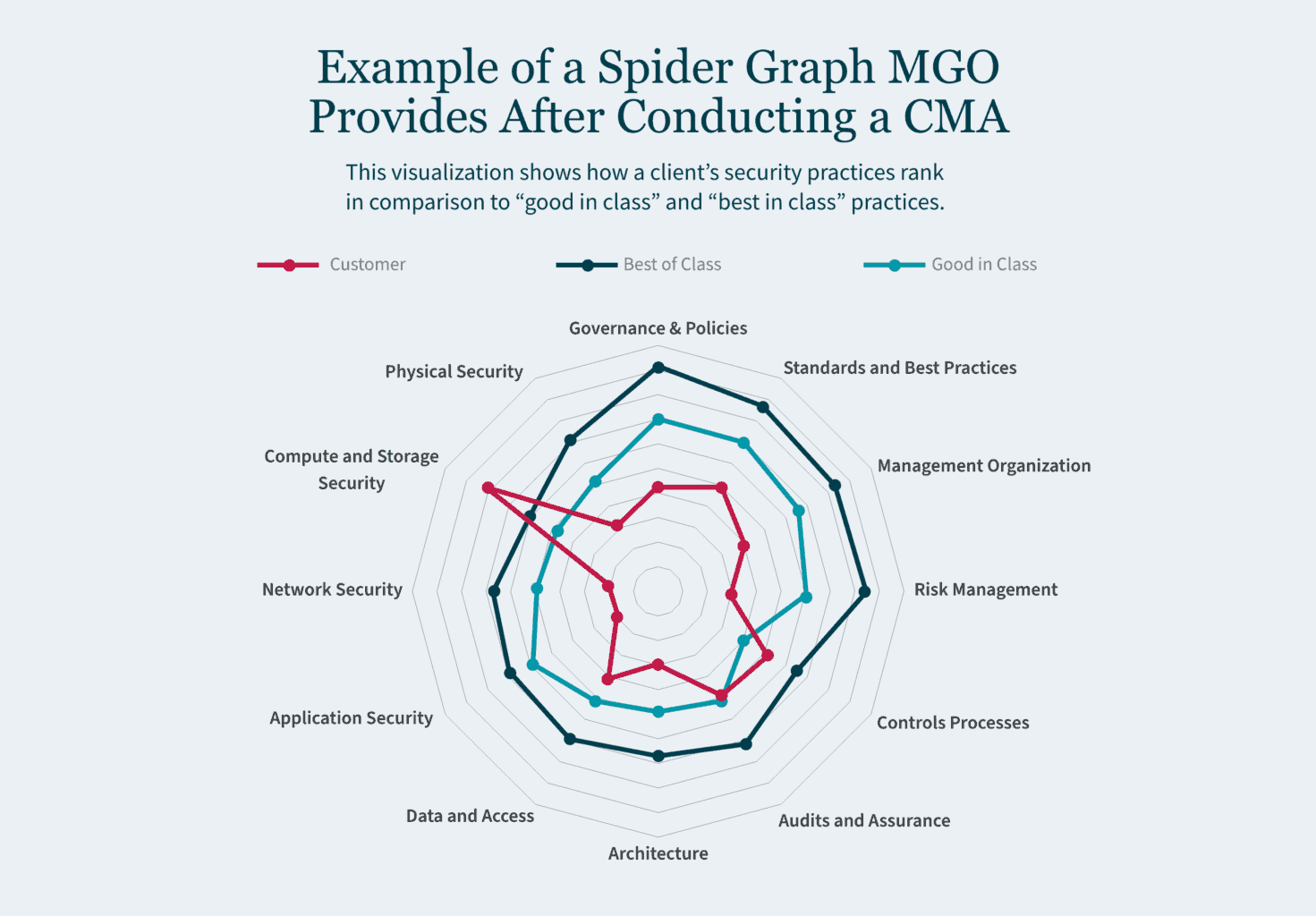
Conducting a productive CMA that yields meaningful insights requires experience with security frameworks and familiarity with the latest threat trends impacting state and local governments. At MGO, our Technology and Cybersecurity Advisory (TCA) team approaches each CMA engagement through a consistent methodology focused on mapping security practices to leading industry standards, evaluating core capability areas, and developing practical recommendations tailored to the organization.
Key elements of MGO’s CMA methodology include:
- Utilization of NIST Cybersecurity Framework (CSF), ISO 27001 or CIS Controls as a Baseline – The TCA team will help you identify current gaps in the security of information assets and determine potential opportunities for improvement relative to your organization’s size and stage in the lifecycle.
- Focus on Key Cybersecurity Capabilities – Emphasizing key cybersecurity capabilities including governance, detection, prevention, response and legal compliance, the TCA team will assist in aligning and mapping these capabilities against industry standards.
- Recommend Prioritized Areas of a Management Action Plan – The TCA team will assist you in identifying key areas of improvement and provide a risk-ranking to help prioritize moving forward.
- Maintaining Continuous Improvement – Instituting a recurring cycle of assessment and improvement is crucial, as cybersecurity maturity is a dynamic process that must adapt to evolving threats and business needs.
How We Can Help You Achieve Your Cybersecurity Goals
Our highly skilled team delivers in-depth cybersecurity and business knowledge that translates to outside-the-box thinking and practical recommendations. We will work with your team to conduct deep-dive walkthroughs and technical testing to help you manage potential cybersecurity issues. Reach out to MGO today to learn how our cybersecurity services can benefit your state or local government.
]]>Proactive planning is vital
State and local governments are frequently constrained by their budgets. Proactive planning spreads both effort and budget into a longer timeframe, which allows investments to be made incrementally and resources to be consistently allocated.
Because cyberattacks are nothing new, many organizations have already prepared some sort of response plan. However, because the pace of cyberattacks and the sophistication of hackers is constantly increasing, your plan should be updated at least annually. A robust plan is a living document that involves cross functional teams that include IT professionals and leadership.
Risks should be identified and prioritized so that urgent needs can be addressed with immediate investments. Although, the complete (or updated) plan may never be complete, the prioritized pieces of it will form a framework through which cybersecurity becomes an ongoing conversation, and a lens through which daily work is viewed.
Have a contingency plan: know who to contact and how
A contingency plan should be in writing. The process of drafting a detailed plan that addresses many different scenarios is time consuming, and it is also necessary. The thought process and discussions that go into thinking through a robust response to a cybersecurity plan are valuable to the whole organization. When a cyberattack occurs, one of the greatest concerns is to stop the loss of sensitive information. Part of contingency planning will involve creating an information classification policy, so your information systems protect the highest value information with the highest level of security.
Contingency planning also involves a communication plan. In what order do you make phone calls to your incident response team, legal counsel, board of directors, insurance agent, or law enforcement? Who needs to know what, when? How do you document your actions?
If you think having these discussions is overwhelming and stressful in the planning stage, imagine what it would be like to try to make critical decisions when your firewall is open, your information systems are locked, and your daily work has come to a halt.
Update your system to reduce risk
State and local governments often have older IT systems, some of which have been in use for 20 years. These systems require patches to prevent cybercrime, and in most cases, the various information systems do not “talk” to each other.
One of the first steps you can take is to update your information systems. Part of this may involve a discussion of a policy manual and potentially some training so that people are aware of the risks that are constantly evolving. A standing IT governance committee may initially be dedicated to the upgrade, and later take on the ongoing task of mitigating cyber risks throughout your organization.
Mitigating some of these risks might include reviewing your cyber insurance policies to ensure that you have adequate coverage for overall data recovery and the cost of business interruption. This committee should also review your backup policies and services to ensure reliable storage in a separate location that is tested periodically to ensure compliance with your contracts.
Prepare to respond to cyberattacks
State and local governments should expect to be targeted — they have access to large amounts of personal information and data. Thus, it is crucial to have a plan that can be immediately put into action to protect this sensitive information for the people and communities you serve. Your response within the first 24 hours of the breach is critical to minimizing damage. With proper planning, even an aggressive attack can be survived with minimal losses.
If your organization is not yet prepared for a cyberattack, or you are interested in proactive planning against a breach, schedule a consultation with the MGO Technology Group or learn more about the services we provide here.
]]>The comment period for these proposed rules lasted for two months, ending on May 9, 2022. During that time, the SEC received more than 100 comments from various sectors, including legal, government, business, and nonprofit. These comments vacillated from critical to supportive, but many had several concerns about the rule’s provisions. For those curious about the specific apprehensions, our Technology and Cybersecurity team analyzes them, as well as the suggested solutions, in this article.
Most common concerns regarding the SEC’s cybersecurity proposal
Within the comments provided on the proposal, there were eight key issues broached along with solutions to these issues.
1. The four-day incident notice deadline
Many commenters believe being given a mere four days to report a cybersecurity incident was not enough time to truly analyze the incident and complete an accurate report. Worried a harried or slapdash report could yield even more security risks, they proposed more flexible solutions to provide accurate disclosures, like:
- A 30-day reporting deadline;
- Government-permitted reporting delays (as needed);
- A modification in the disclosure framework to ensure state notification statutes are exemplified; and
- Additional time for smaller companies to investigate, report, and fully disclose the situation as needed.
2. Law enforcement and national security exceptions
Feedback for the proposed rules also stated some specific incidents should benefit from delayed reporting exceptions, namely those that need to involve law enforcement or security investigations on a larger scale.
This solution allows those grappling with more challenging and involved cybersecurity incidents to remain compliant with the law while doing what is necessary to complete an investigation and strengthen security to prevent future incidents. It also gives law enforcement more freedom to complete their efforts — and prevents publicity that could tip off the attackers, who could then cover their tracks.
3. The definition of key terms
The SEC uses several words that could be misconstrued, have multiple meanings, or are not succinct enough to require disclosures surrounding them. These words, as pointed out in the comments, include:
- Cybersecurity threat,
- Cybersecurity incident, or
- Information systems.
To solve this and streamline compliance reporting requirements, commentors believe the SEC should utilize the thorough and uniform definitions employed by the National Institute of Standards and Technology (NIST), as well as those used in the Cybersecurity Incident Reporting for Critical Infrastructure Act of 2022 (CIRCIA), SEC’s Release Number 33-11028, and the 2016 Presidential Policy Directive on United States Cyber Incident Coordination.
In addition, the SEC can break down each incident or threat into a tier system to accurately encapsulate the severity each tier entails, better describing the impact on the organization.
4. The disclosure of the board of directors’ cybersecurity expertise
Comments also touched on the requirement to include the experience the members of a company’s board of directors have, finding it unnecessary to disclose and tedious to acquire. The suggestions given included eliminating this narrow requirement (primarily because if a board member(s) does not have heavy cybersecurity experience, that could reflect negatively on the company’s prioritization of cybersecurity) even if the company does, in fact, take cybersecurity seriously.
They also call for “cybersecurity expertise” to be defined using broad criteria so smaller companies can meet the requirement without struggling to find an “expert” just to tick a box — or to allow the requirement to meet with a leader at different level in the company besides the board of directors.
5. The accumulation of immaterial events requirement
Another criticism of the proposed rules targets the requirement to list previously undisclosed immaterial cybersecurity incidents, which many comments revealed to find unnecessary and vague, as an incident to one company may be deemed immaterial but found material to another. The lack of consistency and definition means their solution is to either scratch the requirement or, alternatively, provide more guidance on what these incidents should entail to be included, as well as an example of one — and set a one-year limit, as this requirement does not include one.
6. Security program disclosures
Requiring a company to disclose security program-related protocols and plans, like strategies and risk management tactics would, comments to the proposal argue, make the company more vulnerable to future security breaches — as well as inadvertently divulge protected information. To mitigate this, critics suggest removing the requirement to keep companies (and their security plans) safe, allowing a vague summary of the program to meet the requirement; or introducing a confidentiality clause.
7. Fear of regulatory discord
As cybersecurity becomes a bigger issue for all industries across the country, the SEC’s proposal could contradict other states’ laws and requirements regarding cybersecurity (and their varying definitions, triggers, timings, and more). This could create confusion for companies who want to remain compliant in the event of a cyberattack but are unsure of which requirements they must meet to determine if a breach has, in fact, occurred. Readers of the proposed rule believe creating standardized terms and requirements can help. Plus, the SEC should demonstrate how it will work with the other regulations so companies can align their requirements in a streamlined way.
8. Safe harbor provisions
It seemed to many if a company has already reported a material cybersecurity risk, it is redundant to be required to report it again via the Form 8-K. The provided (short) timeframe, too, could cause issues — in the case of a third-party breach, a company may hurry to complete the form without confirming it to be reliable or accurate, defeating the entire point of the form.
This requirement invited split opinions. Some comments mentioned two “safe harbors” (i.e., double reporting) is a good thing, helping the SEC to promote consistent disclosure. Others, however, stated that including both would be redundant, especially with a tight deadline and the lack of clear definitions for these incidents.
Our perspective on the response to the SEC’s cybersecurity proposal
As the SEC strives to increase transparency and prevent malicious cyberattacks, cybersecurity disclosure requirements will continue to change and strengthen. The number of comments received on this proposed rule indicates that companies across industries are not only invested in what these disclosure requirements mean, but they are willing to do what is necessary (albeit logical) to enhance and standardize the way they protect themselves and disclose risk.
Looking forward, the SEC will take these comments into consideration for the next draft of the proposal.
How we can help
While you wait for the next draft of the proposal, remember to stay vigilant—not only to protect your organization, but also to maintain compliance. To stay up to date, bookmark the SEC’s Cybersecurity news and our Technology and Cybersecurity insight library.
Professional service firms like MGO help verify you are compliant and strengthen your overall cybersecurity — so these incidents are less likely to occur, and if they do, you will be ready to mitigate risks at once. Let us know if you are ready to assess your cybersecurity or get started on a SOC for Cybersecurity.
For insights tailored to your company and industry, schedule a conversation with our Technology and Cybersecurity team today.
]]>The SEC’s concerns for reliable information systems aren’t without merit. Increased vulnerabilities and threats including remote work, reliance on cloud and third-party services, virtual and digital payments, and sophisticated malware and ransomware, prompted the proposal of these rules to mitigate potential costs and consequences for businesses and investors. Previous standards were not always adhered to, and cybersecurity disclosures were sometimes dismissed with investors and consumers left uninformed.
To provide more transparent, timely, and consistent information, the SEC has broken down the additional disclosures into four categories:
- Material cybersecurity incidents
- Risk management and strategy
- Governance
- Expertise
For anyone unfamiliar with the SEC’s new cybersecurity requirements, our Technology and Cybersecurity practice breaks down what they are and how you can best adhere to them to keep your organization compliant and secure.
Breaking down material cybersecurity incident disclosures
Under this rule, a company will be required to disclose cybersecurity breaches within four days of discovering the incident (note: this is not four days from the date of the breach itself). To determine if the incident involves material information, the company must consider if a shareholder would find the information breached relevant to making an investment decision. Examples of material cybersecurity breaches that would require this reporting include an impact on:
- Operational technology systems
- Stolen information with intent to extort
- Compromise of data or a network
- Ransomware attacks
- Theft of sensitive business information
Within this disclosure, a company is required to report as much as they can about the incident, including:
- When the incident was discovered
- A brief description of what the incident entailed
- Whether data was altered, taken, accessed, or used by the attacker
- How the incident directly affected operations
- If the company has resolved, or is resolving, the issue
A company is not required to disclose certain specific or technical details that could further hinder a resolution or assist attackers in perpetuating a breach, like its response plans, security systems, networks, and other existing vulnerabilities.
Risk management and strategy rules
The proposed amendment would also require a “consistent and informative” disclosure of a company’s cybersecurity risk management and strategy — including not only its own risk management standards but also third-party service providers and their mitigation.
The company would be expected to disclose how its cybersecurity risk management and strategy factor into the overall business strategy and business model related to the collection and handling of sensitive data and the business’s level of dependency on technology. These disclosures will allow investors to possess the information necessary to evaluate a company’s cybersecurity risk and its ability to potentially manage the impact of an attack.
Within this rule, a company would be required to disclose if it:
- Has a cybersecurity risk assessment and management program (with an attached description of said program).
- Uses third parties with that program, and, if so, has policies and procedures to evaluate their associated cyber risks.
- Has a cybersecurity program that considers prior cybersecurity incidents.
- Has had an incident that has affected or could affect the company.
- Has considered the cybersecurity risks in its business strategy, planning, and capital allocation — and how.
Key governance rules
The SEC’s proposal will ensure a company discloses how its board and management handle and take responsibility for cyber risk, including its general cybersecurity governance and the overall scope of the board’s oversight. Does the duty fall to the entire board, a committee, or specific board members? Are there processes for informing the board of potential risks, and how often do they discuss them? Is cyber risk considered a part of overall strategy and risk management?
In addition, it would require a description of the specified management’s role in managing the cybersecurity risks — like expertise, experience, and general role in implementing the cybersecurity measures. Other disclosures in this category include:
- Responsibilities for evaluating and managing cyber risk.
- If the company has a chief information security officer or similar role, and expertise level of the individual.
- How managers responsible for cybersecurity are informed and monitor efforts like discovery, identification, and remediation of breaches.
- How often the managers responsible for cybersecurity report to the board or committee.
Expertise
Under this amendment, companies would be required to disclose their directors’ expertise in cybersecurity, citing each by name along with prior work experience, level of expertise, certifications and degrees, and skillset.
Prepare your organization with a SOC assessment for cybersecurity
To know where your organization stands with its cybersecurity risks and strategy, an assessment is important — especially a System and Organization Controls (SOC) for Cybersecurity, a framework allowing organizations to communicate the effectiveness of their risk management program and information about their cybersecurity.
As we know, the recently issued SEC proposal would require companies to detail their cybersecurity risks and incidents as well as related books and records for up to five years. Participating in a SOC for Cybersecurity would enable your organization to prepare accordingly with no blind spots. This is especially important if your organization utilizes third-party risk management, a growing concern for many firms due to the increased risk associated with them.
With the SOC for Cybersecurity, you can equip your management, directors, investors, business partners, and other stakeholders with the controls they need to ensure you remain compliant with the SEC’s new additions.
Our perspective
While there have been no updates since the proposed rules, it is important to stay vigilant — not only to protect your organization, but also to maintain compliance. To stay up to date, bookmark the SEC’s Cybersecurity news and our Technology and Cybersecurity insight library.
Professional service firms like MGO help verify you are compliant and strengthen your overall cybersecurity — so these incidents are less likely to occur, and if they do, you will be ready to mitigate risks at once. Let us know if you are ready to assess your cybersecurity or get started on a SOC for Cybersecurity.
For insights tailored to your company and industry, schedule a conversation with our Technology and Cybersecurity team today.
]]>Proactive planning is vital
State and local governments are frequently constrained by their budgets. Proactive planning spreads both effort and budget into a longer timeframe, which allows investments to be made incrementally and resources to be consistently allocated.
Because cyberattacks are nothing new, many organizations have already prepared some sort of response plan. However, because the pace of cyberattacks and the sophistication of hackers is constantly increasing, your plan should be updated at least annually. A robust plan is a living document that involves cross functional teams that include IT professionals and leadership.
Risks should be identified and prioritized so that urgent needs can be addressed with immediate investments. Although, the complete (or updated) plan may never be complete, the prioritized pieces of it will form a framework through which cybersecurity becomes an ongoing conversation, and a lens through which daily work is viewed.
Have a contingency plan: know who to contact and how
A contingency plan should be in writing. The process of drafting a detailed plan that addresses many different scenarios is time consuming, and it is also necessary. The thought process and discussions that go into thinking through a robust response to a cybersecurity plan are valuable to the whole organization. When a cyberattack occurs, one of the greatest concerns is to stop the loss of sensitive information. Part of contingency planning will involve creating an information classification policy, so your information systems protect the highest value information with the highest level of security.
Contingency planning also involves a communication plan. In what order do you make phone calls to your incident response team, legal counsel, board of directors, insurance agent, or law enforcement? Who needs to know what, when? How do you document your actions?
If you think having these discussions is overwhelming and stressful in the planning stage, imagine what it would be like to try to make critical decisions when your firewall is open, your information systems are locked, and your daily work has come to a halt.
Update your system to reduce risk
State and local governments often have older IT systems, some of which have been in use for 20 years. These systems require patches to prevent cybercrime, and in most cases, the various information systems do not “talk” to each other.
One of the first steps you can take is to update your information systems. Part of this may involve a discussion of a policy manual and potentially some training so that people are aware of the risks that are constantly evolving. A standing IT governance committee may initially be dedicated to the upgrade, and later take on the ongoing task of mitigating cyber risks throughout your organization.
Mitigating some of these risks might include reviewing your cyber insurance policies to ensure that you have adequate coverage for overall data recovery and the cost of business interruption. This committee should also review your backup policies and services to ensure reliable storage in a separate location that is tested periodically to ensure compliance with your contracts.
Prepare to respond to cyberattacks
State and local governments should expect to be targeted — they have access to large amounts of personal information and data. Thus, it is crucial to have a plan that can be immediately put into action to protect this sensitive information for the people and communities you serve. Your response within the first 24 hours of the breach is critical to minimizing damage. With proper planning, even an aggressive attack can be survived with minimal losses.
If your organization is not yet prepared for a cyberattack, or you are interested in proactive planning against a breach, schedule a consultation with the MGO Technology Group or learn more about the services we provide here.
The coronavirus probably has not hit its peak yet, but every facet of daily life has already been affected. Many companies are actively reaching out to their customers to ensure operations will continue under the best of circumstances and as government regulations allow. For many companies this means supporting a widely spread remote worforce.
As we are already in the midst of this crisis, the chance for your firm to proactively prepare for disrupted operations has passed, but this does not mean there is nothing that can be done. Thanks to the plethora of cloud-based processing options, it is still possible to fully secure resources for the majority of your staff to work remotely. It may be more expensive right now, but that is still a better alternative than shuttering operations entirely. For companies that have already gone remote, you have probably deployed your remote desktop connections, trained your staff on remote conferencing options, and made sure your phone data plans are paid up for any type of mobile device solution you choose to use. Now that these features are fully deployed, this is a great time to review them for potential cybersecurity risk factors.
As is the case with on premise work, cybersecurity has no ‘one size fits all’ solution for remote environments. Each company is going to be different and will require its own strategy to mitigate risk. However, there are some basic steps companies can take to ensure that their cyber risk is limited as much as possible during this time of remote work.
Risks of relying on public internet
The single largest risk factor for remote work is the public internet that is being used by your staff to access your company data, but there are some simple steps you can take to mitigate risk from the largely unsecured public internet.
First and foremost is the securing and monitoring of all connections into your infrastructure. Think of all connections to your data, from any location, as a phone call. A device calls into the physical location of your data to access it, process it, and possibly transfer it to another location, much as you would see with a phone call or fax machine. The key is to identify the various points from which these devices can ‘call into’ your physical infrastructure and then limit the number of devices that can actually make this call. Identifying and securing the remote access points of your company data or network infrastructure is most likely the easier of the these two tasks as in most circumstances you should have near full control over the physical space in which your data storage device resides.
Establishing a secure infrastructure
From here, the simplest and most effective means of protection is to erect a firewall to keep out unauthorized calls. Step two is to do as much as you can to secure the connections that you want to allow through the firewall. The simplest means to accomplish this is through a Virtual Private Network (VPN) that will not only provide verification of the authorized connections past your firewall, but will also create a secure tunnel by which the call into your data can travel.
The VPN will compensate for most security provisions your staff’s at home internet might or might not have. From there, you will need to look carefully at which devices you actually will allow in through your firewall. It would be prudent to direct your technical team or IT Vendor to create a list of approved devices that is as small as possible. You should limit approved devices to company issued laptops and mobile handsets. You can expand this list to employee owned devices, but this should only be done with the advent of a Mobile Device Manager (MDM) solution. While a VPN will compensate for an insecure connection, an MDM will compensate for the lack of cybersecurity protection an employee owned device may or may not have. At this point, you might be asking, where can I find VPNs, MDMs, etc. Thankfully there are plenty of businesses on the open market that have these tools, and even technical staff, setup and ready to deploy and are just waiting for a company like yours to engage them for assistance. By employing these two relatively simple steps, your company can create remote work infrastructure that will significantly cut down on the risks of employees working from home over the open internet.
Vigilant infrastructure maintenance
Now that we have looked at what infrastructure should be put in place, we next need to look at how to properly maintain the infrastructure. As with the technical tools listed above, the market has plenty of Managed Service Providers (MSPs), such as MGO Technology Group, that are ready to engage and provide you with the technical staff and tools your company will need to effectively continue operations during this crisis. Make no mistake about it, your remote work environment is going to require some form of troubleshooting, either in the form of equipment malfunction or staff training on how to properly use the tools mentioned above. This is where having a good level one (L1) IT support staff comes into play in your cybersecurity strategy. In order to properly mitigate the risks of data breach or leakage, your staff will need to correctly use the tools you have put into place. Never underestimate how far a well-trained and well-equipped IT support staff can go in correcting the human errors not caught by your VPNs, Firewalls, and MDMs.
Access professional guidance
In order to weather this crisis or any over further disruption your company might experience, you are going to need good equipment and knowledgeable people to install and maintain this equipment. Finding, maintaining, and retaining the equipment and staff can be a difficult and time consuming endeavor. As mentioned above, you may want to consider engaging with technical MSPs who have the training and resources in order to install and maintain the infrastructure your company will need to not only allow your employees to work from home, but to also switch back to working on premise as soon as the situation improves.
For more guidance or to schedule a consultation, contact us here.
]]>Today’s world is more connected than ever. Not only are users sharing more information across the Internet than at any other time in history, they are doing so with a variety of devices available to the public. That’s hundreds of devices available for a user to connect and conduct various facets of their lives in a convenient and productive way. It also means thousands of potential vulnerabilities that nefarious actors can exploit. Mobile devices represent the newest threat to user security as more and more of our digital lives are accessed via these handheld computers. Given the popularity of these devices, it’s not surprising that hackers have turned their attention to how they can exploit vulnerabilities for personal gain.
Because mobile devices are often used outside of a regulated environment, such as an office or private network, they can be susceptible to attacks over public networks that purposely do not restrict access. Despite these inherent vulnerabilities, there are several steps you can take on your handset to help ensure that your device remains secure. Though this list is not all-encompassing, it will provide a handy guide to make sure your mobile environment remains a safe and reliable tool for you to use.
1. Keep your apps and operating system up-to-date
Updates will apply the most recent security patches to both your apps and operating system which is why you should apply the updates as soon as you see the notification from your phone. For an extra layer of protection you should consider allowing your apps to auto-update while the device is connected to WiFi.
2. Keep access secure
Always use a PIN, Passcode, or some form of Biometric Authentication to access your phone. No one, not even you, should be able to pick up your phone and access it without some form of verification. Though passcodes are still the strongest form of a security on a mobile device, you can provide an adequate layer of security by applying both Biometrics, such as a fingerprint or eye scan, and a backup pattern or PIN.
3. Limit points of access
When you are not using these features, you should turn off WiFi, Bluetooth, and the Near Field Communication (NFC) receiver. The less active access points available on your phone, the less likely someone will be able to exploit them. This doesn’t mean you should never use them. However, shutting them off when you are not using them not only lowers your attack surface, it’s healthier for the device’s battery. Many headsets also now include software that allows you automate turning these settings on and off with a single voice command. Try to make use of these tools to find the most efficient balance for your own lifestyle.
4. Mind your connections
Much like you would think twice about going to places where you may have doubts about safety, so should you be mindful about who and what you allow your phone to connect with. ONLY allow connections and access to devices, individuals, and apps you know you can trust. his includes only downloading apps from a trusted source such as the Google Play or Apple Apps Store. Additionally, be wary of any apps that request admin level permissions in order to function. Is having that one face filter really worth giving an app access to ALL of your friend’s contact information?
5. Keep the device tidy
Occasionally you should inventory the apps on your device and decide if you still actively use them. Deleting unused apps has an array of benefits, which include freeing up storage and processing power, reducing background usage, and reducing possible attack vectors from apps that are no longer updated by the developer. Most handsets now come with tools to allow you to list your apps based on the last time they were used. This can help you narrow down those that should be removed first.
6. NEVER jailbreak your phone
As temping as some might make it sound you should never ‘root’ or ‘jailbreak’ your phone if you wish to keep it secure. Doing so removes many of the protections that handset makers often put in place to prevent incompatible programs from interfering with the phone’s basic functions. Jailbreaking your phone removes these protections while also taking your operating system out of the regular update cycle. Jailbreaking your phone may also have the effect of voiding it for many Bring Your Own Device (BYOD) programs run by professional organizations.
To learn more about cyber and information security, for you and your organization, schedule a consultation with the experts at MGO Technology Group.
]]>Are your employees comfortable telling leadership about a potential problem at your company? Now ask yourself, are they comfortable telling leadership about a potential mistake? A large number of today’s cyberbreaches often begin as the result of an innocent mistake by an employee. It might be sharing a password over an unprotected median, a nefarious actor grabbing a picture of an employee’s laptop screen while they are working in public, or as is most common, an employee clicks on an innocuous link from a phishing email. What most employers may not realize is that many employee’s common sense regarding breaches is actually pretty good. At the very least they will suspect that something is amiss, which could be the first step in detecting a potential breach. Empowering your employees to actively look for, and report on, potential breaches goes a long way to helping your organization build a strong cyber security culture.
Creating a positive cyber security culture
The first step is to educate your employees on what to look out for when it comes to cyber and information risk. Many firms employ some form of basic cyber-security training, mostly at the time of on-boarding, but training usually ends there. Cyber security is an ever-shifting landscape where threats are always evolving. This is why it is important for firms to enact a year-round cyber security awareness program based around employee activities. A good employee-based cyber security awareness program will be light on technical jargon and focused on highlighting the vulnerabilities of the processes and systems that all employees use in their day-to-day work, such as instant messaging, answering e-mails, browsing the web, and sending documents through authorized and unauthorized means of file sharing. There is no great need to get into the technical details of how an attack might happen, but rather acknowledge that the danger is out there and focus on what employees can do to look out for potential dangers, such as noticing strange URL’s and suspicious e-mail attachments from unrecognized users. Consistently educating employees on current cyber threats and methods will give them the tools to identify a threat and be proactive in helping your company stop it.
Encouraging active breach and threat reporting
Training employees to spot the dangers is only half the battle. The other half is generating an effective reporting culture. No cyber security strategy is complete without a good cyber security reporting culture that puts a premium on reporting potential breaches. Here are a few suggestions to create a positive culture of reporting:
Have the team that provides your first level IT Support lead awareness/education sessions, as they will mostly likely also be the first point of contact for reporting potential breaches. The sessions can be developed by an outside consultant or an internal cyber security professional, but building a repertoire between those who should be reporting the incident and that first point of contact provides a sense of comfort that your employees are reporting the issue to the right group in the correct way.
In training, the IT support staff should make clear that reporting a threat is NOT a burden and that employees should err on the side of caution. If an employee receives an e-mail they find suspect they should not hesitate to contact their IT department through the designated reporting means.
Everyone from the organization must know and believe that the consequences of reporting a potential mistake will not be dire. Beyond feeling comfortable reporting suspicious activities, employees must also feel comfortable in reporting suspicious behavior that might be a direct result of their own actions. If an employee feels that admitting a mistake will be detrimental to their career they will keep quiet and a potential breach oversight could occur. Admittedly, this strategy carries some risk as you do not want certain behaviors to be consequence-free. However, the scope of consequence must be weighed against the actual action.
For example, an employee need not be officially reprimanded for admitting to clicking on a suspicious link and reporting it, but it would be prudent for the IT support staff to point out what could have been done differently to avoid the infraction. If the employee becomes a repeat offender, then a more official process might be warranted. Until then, simply pointing out of the issue should be enough to change behavior while maintaining a culture where employees are not fearful of bringing an issue forward.
Strong and proactive cyber security culture starts at the top
When setting the company’s cyber security policy, upper management must keep an eye toward baseline employees who perform the day-to-day actions of the company. Clear signals about saying something if you think something is wrong can go a long way toward changing your company culture. Having a strong IT or Cyber Security group is simply not enough when your own staff could unknowingly be your cyber Achilles Heel. There is a saying in cyber security that “every employee is a potential vulnerability.” However, if trained and leveraged correctly, your employees can also act as another safeguard, actively working to protect your information technology environment.
If you have any questions or would like support developing and implementing an effective cyber security program, reach out to the MGO Technology Group for a consultation.
]]>THE AMCA breach and its impact on clients and patients
It is most likely you have not heard of AMCA. However, if you have had any form of medical test in the past few years, there is a very good chance you know some of their largest clients: LabCorp and Quest Diagnostics, two of the largest medical laboratories in the United States.
AMCA was a third party debt collector for LabCorp, Quest Diagnostics, and several other medical companies. As a result AMCA had a deep data sharing relationship with these firms, which included the exchange of patient health and financial information. At the time of this posting, the initial cause of the breach at AMCA is unknown. Early indicators point to an intrusion on their payments website, but it is unclear how that intrusion actually took place. We’re sure the investigation will turn up more details on the nature of the attack, but it’s already too late for AMCA. The company has filed for Chapter 11 bankruptcy protection due to the astronomical costs of notifying their clients’ patients of the breach, and the termination of client relationships with AMCA. This result doesn’t even begin to cover the costs that LabCorp and Quest could incur due to possible HIPAA violations.
Understanding the risk posed by third party vendors
No matter what industry you work in, it is likely that your company uses a third party vendor, even in a limited capacity, for day to day operations. Are you sharing critical, sensitive or proprietary information with your vendor? If so, do you know the nature of the data sharing relationship between your company and theirs? If the answer is along the lines of ‘probably not’ then you have some work to do.
Though the rules of every industry are different, on the whole, you are still responsible for your customer data no matter who you may turn it over to. If there is a breach, it doesn’t matter if it was caused by something that was out of your company’s control, your customers are going to come to you first for explanations and redress. As such, you need to work to mitigate as much outside risk as possible and short of cutting off all third party vendor contact and taking all operations internal, the best way to do this is with a standardized and transparent Third Party Risk Management Program (TPRMP).
The fundamentals of an effective third party risk management program
TPRMPs are going to look different for every company across every industry, but on the whole they should include these three parts:
An introspective review – Before signing on the dotted line with your potential vendor, you need to have discussions with your business owners and IT and cybersecurity experts to assess your company and determine what information and data needs protecting and why. It’s too easy to say ‘everything’ so your company really needs to dive down and understand what assets, intangible or otherwise, are most important.
Once you make that determination, when you share this data with your trusted vendors, you will be in a position to explain what is important and why. It is incumbent on you to inform your vendor about the criticality of the data you are sharing and ensure they have the proper level of protection. Once you complete the internal assessment and determine what information and data is critical to your company, you need to create and embrace a third party risk management program. One tool within this program is a questionnaire that you can share with your vendor so they can perform a self-assessment on their cyber and IT controls to ensure your data remains secure.
Risk Assessment – With the questionnaire in hand, your company needs to explain to the vendor that the information you are sharing is critical and why. You will ask them to complete the questionnaire so you can gain an understanding of their control environment. In some circumstances, you may go beyond the self-assessment questionnaire and perform an onsite assessment to validate that what they have in place is accurate. Once you have gathered the information on the vendor you will need to have a qualified professional, either internal to your company or a trusted partner, review the responses and determine if the control environment at the vendor is adequate to protect your data.
One major area to consider will be to evaluate how your own company will be exchanging information and resources with the vendor. Remember that not all data is shared via email or electronically and people sometimes forget that physical items such as prototypes are sensitive and critical. You also must remember that the kind of data you share may change over time, along with the mechanisms for sharing. Your relationship with the vendor is ongoing and the risk assessments that you perform on your vendor should evolve and align over time. Once you have a qualified person make a final determination of your risk by engaging with a vendor you are then able to make an informed business decision.
Continuous Updating – TPRMPs are not one and done once you sign on the dotted line. Threats evolve every day and your TPRMP needs to evolve with it. Before you engage with your vendor you should have asked them not only what their plans are to continuously improve their security, but how will they inform you about it. Beyond the initial questionnaire or assessment, a carefully written contract with your vendor regarding the responsibilities of each party in maintaining the confidentiality, integrity, and availability of the entrusted data is critical to a successful and secure relationship and partnership. Clear communication to the vendor and continuous attention to the control environment will help ensure that the data entrusted will remain secure and private and that the “B” word, bankrupt, does not happen to your company.
It is possible, and likely, that Quest and LabCorp had a TPRMP in place with AMCA when they engaged them as a vendor. However something went wrong, and now a large corporation is going under and millions of people are exposed to fraud. The cause of this major security and data breach will come out over time and lessons learned will hopefully strengthen other TPRMPs to help ensure similar breaches are not experienced. All good Cyber Security programs, including TPRMPs, must evolve and get stronger with time and the lessons learned from various breaches.
]]>But what happens when your technology leaves you vulnerable, such as in the case of your IT environment suddenly held hostage by a cybercriminal?
According to Recorded Future, since 2013 there have been 170 city, county and state governments that have been attacked using ransomware, a type of malicious software built to interrupt or shut down your business or government operations. That means it’s a good time to understand how it works and, more important, what you can do to prevent it.
How it works
Ransomware blocks access to your data by encrypting it, then you’re informed you will only receive a decryption code when a sum of money is paid to these anonymous cybercriminals. The attack is sudden and the clock begins ticking for you to pay the ransom, or lose access to your computer system forever.
Fundamentally these attacks are successful because the proper safeguards are not in place for various reasons, the ain one being perceived cost. Statistics support the aphorism that it’s not so much a matter of “if” your organization will get hit, but rather a matter of “when” an attack will happen.
According to Malwarebytes’ Cybercrime Tactics and Techniques Q1 2019 Report, ransomware for businesses of all sizes is up 195 percent in the first quarter of 2019 since the final quarter of 2018, and up more than 500 percent when compared to the first quarter of 2018. This risk is certainly not going away anytime soon.
The financial backlash can be devastating, but even worse can be the loss of access to daily electronic processes, computer data, employee time, organizational records and invaluable information.
Recent ransomware attacks
- City of Baltimore: On May 7, the RobbinHood ransomware infection hit. An estimated $18 million has been reported as likely damages, with $10 million going toward the repair of the city’s systems, while $8 million is in forgone interest and penalties. Some services are still not restored and others are using manual processes.
- City of Atlanta: More than a year ago the city was brought to its knees as the result of a ransomware attack, when the cybercriminal demanded $51,000. Payment was not made and to date nearly $17 million has been spent repairing the damages. In addition, valuable police department dash cam video has been lost forever according to reports.
- State of New York: Hackers demanded $30,000 from the Erie County Medical Center in Buffalo. When hospital officials refused to pay, 6,000 of the hospital computers were wiped. It took six weeks to get up and running again, during which time employees were forced to
keep handwritten records. Officials estimate it cost $10 million to recover from the attack. - State of Florida: In December, just before Christmas, a Florida grocery store suffered a ransomware attack when its QuickBooks server was held for ransom. In this case, the cybercriminal wanted
1.5 bitcoin or, at the time, $5,100. Because the owner did not have reliable back-up files they were compelled to pay the ransom, but they still lost a significant amount of data.
As you can see, regardless of the type of industry or size, cybercriminals are widely casting their nets, which reasonably ensures their catch will amount to a good payday.
8 steps to security
However, all is not lost. There are eight steps you can take that will go a long way in securing your IT environment, rendering it more difficult for cybercriminals to access.
1. Perform a security assessment of your IT environment. Do not rely upon “it hasn’t happened to me yet, so I doubt it will” reasoning. The risk is not worth it.
2. Provide security awareness to anyone accessing your IT environment to prevent the No. 1 cause of cyber-attacks: Phishing. Humans continue to be the weakest link. You need to go beyond training and make employees aware, so that it becomes part of the security culture.
3. Back up your data daily. If you find yourself in the unfortunate position of being a ransomware victim, the best way to recover from the attack is to have secure and reliable backups ready to use when you are held hostage.
4. Patch software immediately. When fixes are made available, don’t wait. Update your software so hackers can’t exploit a vulnerability.
5. Limit the number of people who can install software. This is the IT version of “too many cooks spoil the broth.” You need to trust that your employees are doing the right thing when installing and updating software, and that they’re not relying upon free software, which is a notorious gateway for malware.
6. Use a reputable antivirus software (AV). AV is a simple, yet powerful step that will lower your chances of being attacked by ransomware.
7. Perform security monitoring of your network. You MUST be aware of what is happening in your network by performing 24x7x365 monitoring, which will help ensure you’re actively looking for the bad guys.
8. Use two-factor authentication. Gone are the days of just a single password. Having two forms of authentication, such as a password and a biometric, to access your network will provide added assurance.
While nothing is foolproof, taking preventive measures maintains your brand, ensures customer retention and prevents a cyber breach. At the end of the day you want the peace of mind that’s provided when you know you have done everything you can—even when it’s “just in case.”
Mark Cousineau, CPA, CITP, CGMA, CIA, CFE, CGAP, CGFM, CRMA is a director at MGO and Karl Kispert is managing director of MGO’s technology group. You can reach Mark at mcousineau@mgocpa.com or contact Karl Kispert here.
Published in California CPA magazine July 2019
]]>