Executive Summary:
- The Sarbanes-Oxley (SOX) Act established stricter financial reporting requirements for public companies, leading to increased scrutiny of Information Produced by the Entity (IPE).
- IPE carries different levels of risk depending on whether it is system-generated and manually prepared IPE. Strong documentation is key to validating completeness and accuracy of IPE.
- Best practices for IPE documentation include identifying the source, parameters, and format of reports; validating totals and counts; retaining screenshots; and having knowledgeable reviewers.
~
Passed by Congress in 2002, the Sarbanes-Oxley (SOX) Act revolutionized public company audits by introducing financial reporting requirements aimed at increasing transparency and preventing fraud. Most notably, the SOX Act established the Public Company Accounting Oversight Board (PCAOB), a nonprofit organization that oversees the audits of public companies to protect investors and further the public interest in the preparation of informative, accurate, and independent audit reports.
The PCAOB refines its auditing standards annually and, in recent years, the organization has placed greater scrutiny on the work of external auditors. To keep up with PCAOB compliance, external auditors have imposed more rigorous documentation requirements on companies. As a result, companies have felt pressure to provide more expansive Information Produced by the Entity (IPE).
If external auditors have applied greater scrutiny on your reporting, you may be wondering: What level of documentation is sufficient? How can you improve your documentation to avoid deficiencies and provide greater clarity? In this article, we will discuss: 1) what IPE is, 2) the risks associated with different IPE, and 3) how to document your IPE thoroughly.
What is IPE?
IPE is any information created by a company used as part of audit evidence. Audit evidence may be used to support an underlying internal control or as part of a substantive audit. Although there are documentation and risk severity differences between system-generated and manually prepared IPE, the fundamental questions that need to be addressed are the same:
- Is the data complete?
- Is the data accurate?
Risk Levels of Different IPE
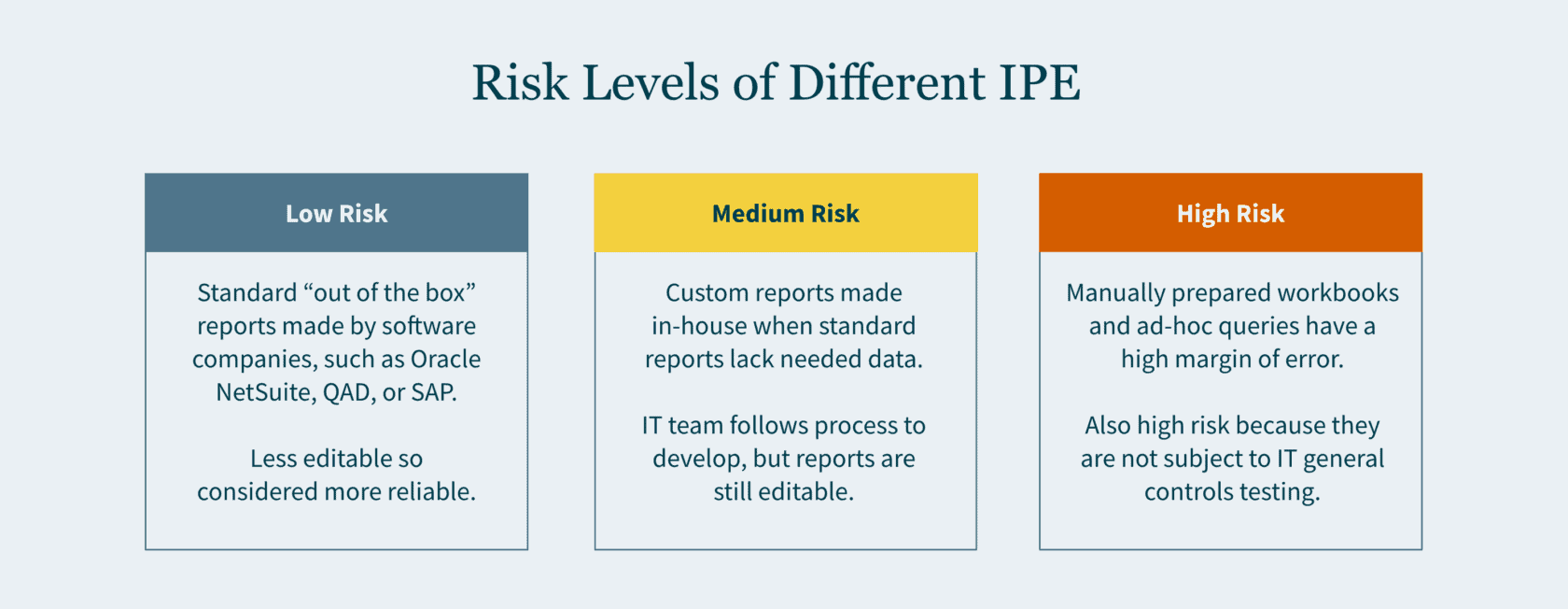
Here is an overview of how risk levels vary for different types of information you report to auditors:
Low Risk
“Out of the box” reports carry the lowest risk. These reports are also referred to as “standard” or “canned” reports. Standard reports have been developed by software companies — such as Oracle NetSuite, QAD, or SAP — as part of their enterprise resource planning (ERP) systems. Typically, the end user (you) and even your IT team cannot modify these reports. Given the constrained editability, greater reliance is placed on these reports.
Medium Risk
Custom reports are typically driven by the business team and developed in-house by your company’s IT team. When your company’s ERP system does not have a report that would provide sufficient data, the in-house developers create a custom report. The IT team follows their change management process when developing the request report. If the report results do not align with your business team’s expectations, the query is refined, and the process is repeated until it does.
High Risk
A manually prepared workbook or an ad-hoc query are inherently the riskiest documentation. A manually prepared workbook may be a debt reconciliation prepared by your staff accountant, or a list of litigations the company is involved in drafted by your legal department. Given that these are manually drafted, the margin of error may be high.
An ad-hoc query is considered high risk since the report is not subject to IT General Controls (ITGC) testing. The end user may input any parameters to generate the report. Since no control testing is performed by your company, external auditors would need to rely on their own IT team to vet the nonstandard query.
How to Document IPE?
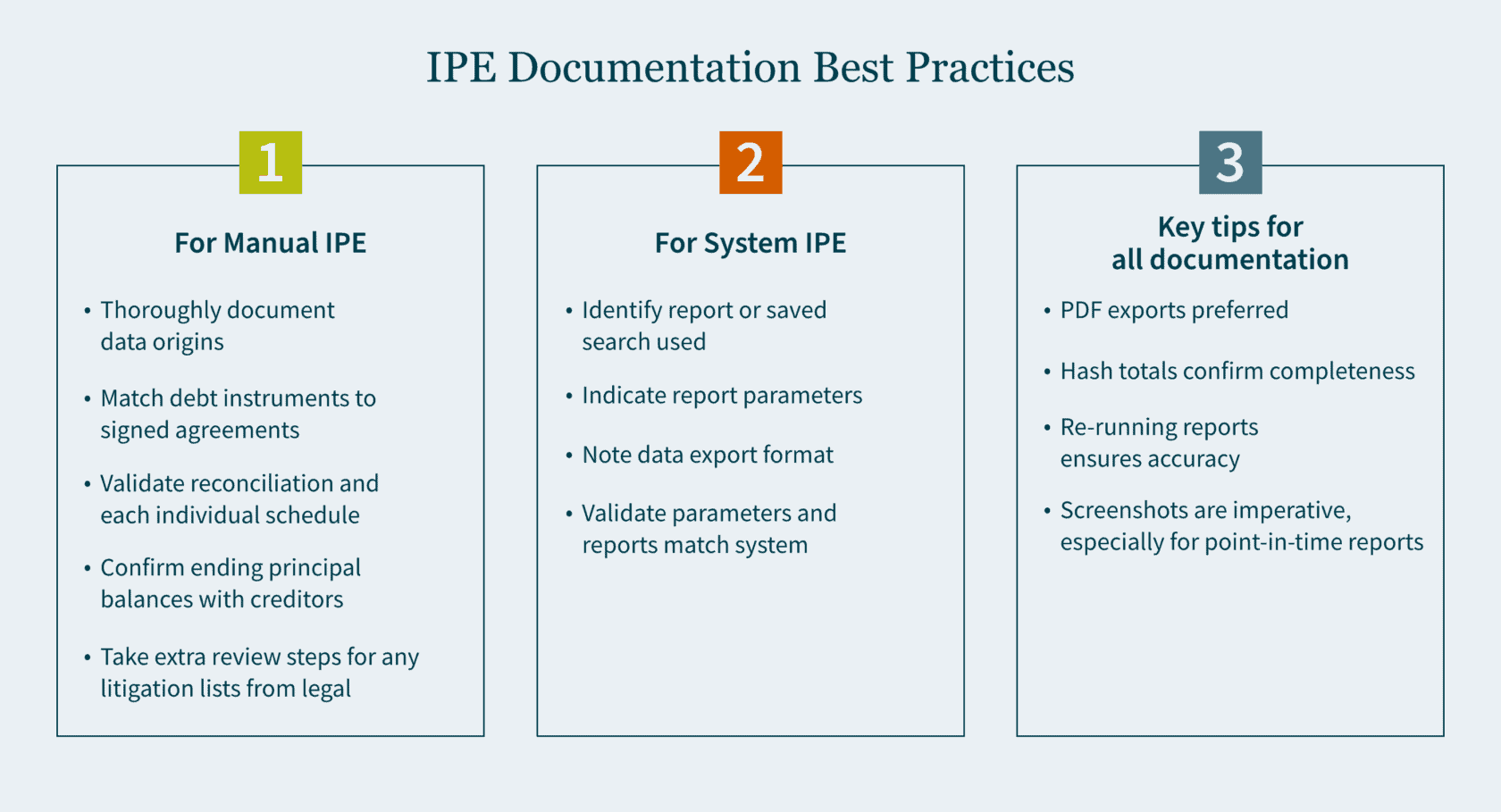
Your documentation will vary to a certain degree depending on whether the IPE is manually prepared or system generated. In either case, it is important to be as thorough as possible when documenting your procedures.
Manual IPE
For a manually prepared workbook, provide thorough documentation about the origins of the data. It is ideal to have someone who is privy to the information review the workbook.
When the reconciliation is comprised of debt instruments, the reviewer should do the following:
- Match the list of individual debt instruments to the signed agreements.
- Validate the reconciliation and each individual schedule for mathematical accuracy.
- Confirm ending principal balances with creditors (where possible).
If the list consists of litigations compiled by the legal department, the reviewer should do the following:
- Send confirmations to outside counsel (where possible).
- Obtain a list of commitments and contingency journal entries made to an accrual.
These additional steps provide greater comfort that the list compiled is complete and accurate.
System-Generated IPE
For system-generated IPE, there are a handful of questions to keep in mind:
- Have you identified the report or saved search that was used?
- What parameters were used to generate this report?
- In what format is the data exported?
- After you run your report and confirm the parameters are correct, what format should be utilized for your export?
Exported Data
Most ERP systems allow the exporting of data in the following four formats:
- PDF (portable document format)
- Excel
- CSV (comma-separated values)
- Text file
One major drawback in an Excel, CSV, and text file is that, by their nature, they are editable upon export. An additional drawback of a text file is that it does not contain formatting. As the volume of data grows, proving out the completeness and accuracy becomes more challenging. For these reasons, a PDF export is typically preferred.
After the data is exported in one of the four formats, you want to ensure that it agrees back to the system (completeness and accuracy). Here are a few ways to do that:
- Does the exported data have dollar amount totals? If so, agree the total dollar amount to the system.
- Does the exported data have hash totals? An example of a hash total is employee ID numbers which in aggregate have no real value other than providing confirmation that the data is complete and accurate.
- Does the report have a total line count? If totals are not available, line counts may be used. However, it is important to note that while the line count may agree, the data itself could have still been inadvertently manipulated.
Screenshots of Data
Retaining screenshots is imperative for documentation. A detailed screenshot should include some (if not all) of the following:
- Totals (dollar amounts, hash amounts, etc.)
- Lines count
- Parameters utilized
- Time and date stamp
The first three items validate the completeness and accuracy of the exported data. The fourth item confirms when the report was run and if it was timely. There are many reports that are point-in-time and may not be recreated at a future date. Knowing the constraints of the reports you use is important. Retaining screenshots cannot be overemphasized, especially for point-in-time reports.
Certain ERP systems or online portals do not provide a preview of the report prior to the export. This puts a constraint on the validation of completeness and accuracy, as it inhibits screenshots from being taken. In this case, as part of the review, the reviewer should re-run the report and validate that the original report used matches the information in the re-run report.
Strengthen Your SOX Compliance by Implementing Best Practices
There is no perfect science to IPE documentation. But the end goal is to be as detailed as possible. By simply focusing on the fundamental questions and ensuring that your documentation addresses them, your documentation will inevitably improve.
Developing best practices for your team is the cornerstone for any successful audit. Ensure you have the right guidance to make it happen. Our Audit and Assurance team can tailor a SOX environment to meet your needs. Contact us today to learn more.
]]>- The Securities and Exchange Commission (SEC) is promoting the enhancement and standardization of registrants’ disclosures related to cybersecurity risk management, strategy, and governance by adopting a rule that requires public companies to disclose “material” cybersecurity breaches within four days of determining its materiality.
- The SEC wants to know: the processes the companies use to assess, identify, and manage cybersecurity risks, as well as the board’s oversight of such risks and management’s role in assessing and managing those risks.
- The rules apply to nearly all registrants that file periodic reports with the SEC (including foreign private issuers and smaller reporting companies).
- Registrants must also include their risk management, strategy, and governance disclosures in their 2023 annual reports.
The SEC wants public companies to be more transparent with its investors about cybersecurity. On July 26, 2023, it voted 3-2 to adopt new rules on disclosure to promote clarity surrounding “material” breaches and what’s being done to combat them. And it wants them to do this within four days of determining if a cybersecurity breach was material on Form 8-K.
However, delays may be permitted if immediate disclosure of the breach could pose a national security or public safety risk.
Defining “material” disclosures
According to the U.S. Supreme Court, a piece of information is material to investors when its disclosure “would be viewed by the reasonable investor as having significantly altered the ‘total mix’ of information made available.”
Why is the SEC implementing this rule change?
The SEC seeks to protect companies and investors as cybersecurity incidents have increased in number and sophistication in recent years. In their fact sheet they note: “Cybersecurity risks have increased alongside the digitalization of registrants’ operations, the growth of remote work, the ability of criminals to monetize cybersecurity incidents, the use of digital payments, and the increasing reliance on third party service providers for information technology services, including cloud computing technology (…) All of these trends underscored the need for improved disclosure.”
But corporations are contesting the rules, arguing this short announcement period is unreasonable — and could reveal vulnerabilities that could be exploited by more cybercriminals looking to take advantage of a company mid-breach.
What are the requirements for risk management, strategy, and governance disclosures?
Public companies will be required to disclose their cybersecurity breaches within a four-day time period. This disclosure must include additional details too, like the timing of the incident, its impact on the company, and management’s expertise on cybersecurity in Form 10-Ks (and Form 20-Fs for Foreign Filers).
How will the SEC cybersecurity rules affect you?
The SEC has observed that previous cybersecurity announcements have been inconsistent and inadequate.
Many public companies already have plans in place to share sensitive information about their cyber incidents with federal agencies (FBI). Last year, the Cybersecurity and Infrastructure Security Agency (CISA) adopted cybersecurity rules that require critical infrastructure entities to report breaches within three days to CISA. This reporting duplication could prove confusing and time-consuming.
Ultimately, all public companies need robust internal controls and reporting systems to maintain compliance with the SEC requirements. This assumes issuers already have top-tier cybersecurity technology and processes in place. If not, they’ll need to build these functions out to minimize subsequent fallout from investors and regulators when these inadequacies are made public in their reporting.
The SEC strives to protect investors, which isn’t a bad thing. However, the enforcement of these new rules may not be the most logical option to do so.
Ultimately, the question may not necessarily be how many days you should take to disclose your breach but who should actually be regulating cybersecurity, and who has the authority to call the shots. Cybersecurity is no longer a “nice to have” function in an organization.
How we can help
It’s important to stay vigilant to protect your organization from risk and maintain compliance. Our Technology and Cybersecurity Practice can help verify you are compliant and strengthen your overall cybersecurity, so these incidents are less likely to occur. And, if they do, you’ll be ready to mitigate risks sooner— and make progress towards compliance with the SEC’s new rules.
If you are ready to assess your cybersecurity posture, or you have questions about
how the SEC’s new requirements could affect you, schedule a conversation with our Technology and Cybersecurity team today.
The comment period for these proposed rules lasted for two months, ending on May 9, 2022. During that time, the SEC received more than 100 comments from various sectors, including legal, government, business, and nonprofit. These comments vacillated from critical to supportive, but many had several concerns about the rule’s provisions. For those curious about the specific apprehensions, our Technology and Cybersecurity team analyzes them, as well as the suggested solutions, in this article.
Most common concerns regarding the SEC’s cybersecurity proposal
Within the comments provided on the proposal, there were eight key issues broached along with solutions to these issues.
1. The four-day incident notice deadline
Many commenters believe being given a mere four days to report a cybersecurity incident was not enough time to truly analyze the incident and complete an accurate report. Worried a harried or slapdash report could yield even more security risks, they proposed more flexible solutions to provide accurate disclosures, like:
- A 30-day reporting deadline;
- Government-permitted reporting delays (as needed);
- A modification in the disclosure framework to ensure state notification statutes are exemplified; and
- Additional time for smaller companies to investigate, report, and fully disclose the situation as needed.
2. Law enforcement and national security exceptions
Feedback for the proposed rules also stated some specific incidents should benefit from delayed reporting exceptions, namely those that need to involve law enforcement or security investigations on a larger scale.
This solution allows those grappling with more challenging and involved cybersecurity incidents to remain compliant with the law while doing what is necessary to complete an investigation and strengthen security to prevent future incidents. It also gives law enforcement more freedom to complete their efforts — and prevents publicity that could tip off the attackers, who could then cover their tracks.
3. The definition of key terms
The SEC uses several words that could be misconstrued, have multiple meanings, or are not succinct enough to require disclosures surrounding them. These words, as pointed out in the comments, include:
- Cybersecurity threat,
- Cybersecurity incident, or
- Information systems.
To solve this and streamline compliance reporting requirements, commentors believe the SEC should utilize the thorough and uniform definitions employed by the National Institute of Standards and Technology (NIST), as well as those used in the Cybersecurity Incident Reporting for Critical Infrastructure Act of 2022 (CIRCIA), SEC’s Release Number 33-11028, and the 2016 Presidential Policy Directive on United States Cyber Incident Coordination.
In addition, the SEC can break down each incident or threat into a tier system to accurately encapsulate the severity each tier entails, better describing the impact on the organization.
4. The disclosure of the board of directors’ cybersecurity expertise
Comments also touched on the requirement to include the experience the members of a company’s board of directors have, finding it unnecessary to disclose and tedious to acquire. The suggestions given included eliminating this narrow requirement (primarily because if a board member(s) does not have heavy cybersecurity experience, that could reflect negatively on the company’s prioritization of cybersecurity) even if the company does, in fact, take cybersecurity seriously.
They also call for “cybersecurity expertise” to be defined using broad criteria so smaller companies can meet the requirement without struggling to find an “expert” just to tick a box — or to allow the requirement to meet with a leader at different level in the company besides the board of directors.
5. The accumulation of immaterial events requirement
Another criticism of the proposed rules targets the requirement to list previously undisclosed immaterial cybersecurity incidents, which many comments revealed to find unnecessary and vague, as an incident to one company may be deemed immaterial but found material to another. The lack of consistency and definition means their solution is to either scratch the requirement or, alternatively, provide more guidance on what these incidents should entail to be included, as well as an example of one — and set a one-year limit, as this requirement does not include one.
6. Security program disclosures
Requiring a company to disclose security program-related protocols and plans, like strategies and risk management tactics would, comments to the proposal argue, make the company more vulnerable to future security breaches — as well as inadvertently divulge protected information. To mitigate this, critics suggest removing the requirement to keep companies (and their security plans) safe, allowing a vague summary of the program to meet the requirement; or introducing a confidentiality clause.
7. Fear of regulatory discord
As cybersecurity becomes a bigger issue for all industries across the country, the SEC’s proposal could contradict other states’ laws and requirements regarding cybersecurity (and their varying definitions, triggers, timings, and more). This could create confusion for companies who want to remain compliant in the event of a cyberattack but are unsure of which requirements they must meet to determine if a breach has, in fact, occurred. Readers of the proposed rule believe creating standardized terms and requirements can help. Plus, the SEC should demonstrate how it will work with the other regulations so companies can align their requirements in a streamlined way.
8. Safe harbor provisions
It seemed to many if a company has already reported a material cybersecurity risk, it is redundant to be required to report it again via the Form 8-K. The provided (short) timeframe, too, could cause issues — in the case of a third-party breach, a company may hurry to complete the form without confirming it to be reliable or accurate, defeating the entire point of the form.
This requirement invited split opinions. Some comments mentioned two “safe harbors” (i.e., double reporting) is a good thing, helping the SEC to promote consistent disclosure. Others, however, stated that including both would be redundant, especially with a tight deadline and the lack of clear definitions for these incidents.
Our perspective on the response to the SEC’s cybersecurity proposal
As the SEC strives to increase transparency and prevent malicious cyberattacks, cybersecurity disclosure requirements will continue to change and strengthen. The number of comments received on this proposed rule indicates that companies across industries are not only invested in what these disclosure requirements mean, but they are willing to do what is necessary (albeit logical) to enhance and standardize the way they protect themselves and disclose risk.
Looking forward, the SEC will take these comments into consideration for the next draft of the proposal.
How we can help
While you wait for the next draft of the proposal, remember to stay vigilant—not only to protect your organization, but also to maintain compliance. To stay up to date, bookmark the SEC’s Cybersecurity news and our Technology and Cybersecurity insight library.
Professional service firms like MGO help verify you are compliant and strengthen your overall cybersecurity — so these incidents are less likely to occur, and if they do, you will be ready to mitigate risks at once. Let us know if you are ready to assess your cybersecurity or get started on a SOC for Cybersecurity.
For insights tailored to your company and industry, schedule a conversation with our Technology and Cybersecurity team today.
]]>The SEC’s concerns for reliable information systems aren’t without merit. Increased vulnerabilities and threats including remote work, reliance on cloud and third-party services, virtual and digital payments, and sophisticated malware and ransomware, prompted the proposal of these rules to mitigate potential costs and consequences for businesses and investors. Previous standards were not always adhered to, and cybersecurity disclosures were sometimes dismissed with investors and consumers left uninformed.
To provide more transparent, timely, and consistent information, the SEC has broken down the additional disclosures into four categories:
- Material cybersecurity incidents
- Risk management and strategy
- Governance
- Expertise
For anyone unfamiliar with the SEC’s new cybersecurity requirements, our Technology and Cybersecurity practice breaks down what they are and how you can best adhere to them to keep your organization compliant and secure.
Breaking down material cybersecurity incident disclosures
Under this rule, a company will be required to disclose cybersecurity breaches within four days of discovering the incident (note: this is not four days from the date of the breach itself). To determine if the incident involves material information, the company must consider if a shareholder would find the information breached relevant to making an investment decision. Examples of material cybersecurity breaches that would require this reporting include an impact on:
- Operational technology systems
- Stolen information with intent to extort
- Compromise of data or a network
- Ransomware attacks
- Theft of sensitive business information
Within this disclosure, a company is required to report as much as they can about the incident, including:
- When the incident was discovered
- A brief description of what the incident entailed
- Whether data was altered, taken, accessed, or used by the attacker
- How the incident directly affected operations
- If the company has resolved, or is resolving, the issue
A company is not required to disclose certain specific or technical details that could further hinder a resolution or assist attackers in perpetuating a breach, like its response plans, security systems, networks, and other existing vulnerabilities.
Risk management and strategy rules
The proposed amendment would also require a “consistent and informative” disclosure of a company’s cybersecurity risk management and strategy — including not only its own risk management standards but also third-party service providers and their mitigation.
The company would be expected to disclose how its cybersecurity risk management and strategy factor into the overall business strategy and business model related to the collection and handling of sensitive data and the business’s level of dependency on technology. These disclosures will allow investors to possess the information necessary to evaluate a company’s cybersecurity risk and its ability to potentially manage the impact of an attack.
Within this rule, a company would be required to disclose if it:
- Has a cybersecurity risk assessment and management program (with an attached description of said program).
- Uses third parties with that program, and, if so, has policies and procedures to evaluate their associated cyber risks.
- Has a cybersecurity program that considers prior cybersecurity incidents.
- Has had an incident that has affected or could affect the company.
- Has considered the cybersecurity risks in its business strategy, planning, and capital allocation — and how.
Key governance rules
The SEC’s proposal will ensure a company discloses how its board and management handle and take responsibility for cyber risk, including its general cybersecurity governance and the overall scope of the board’s oversight. Does the duty fall to the entire board, a committee, or specific board members? Are there processes for informing the board of potential risks, and how often do they discuss them? Is cyber risk considered a part of overall strategy and risk management?
In addition, it would require a description of the specified management’s role in managing the cybersecurity risks — like expertise, experience, and general role in implementing the cybersecurity measures. Other disclosures in this category include:
- Responsibilities for evaluating and managing cyber risk.
- If the company has a chief information security officer or similar role, and expertise level of the individual.
- How managers responsible for cybersecurity are informed and monitor efforts like discovery, identification, and remediation of breaches.
- How often the managers responsible for cybersecurity report to the board or committee.
Expertise
Under this amendment, companies would be required to disclose their directors’ expertise in cybersecurity, citing each by name along with prior work experience, level of expertise, certifications and degrees, and skillset.
Prepare your organization with a SOC assessment for cybersecurity
To know where your organization stands with its cybersecurity risks and strategy, an assessment is important — especially a System and Organization Controls (SOC) for Cybersecurity, a framework allowing organizations to communicate the effectiveness of their risk management program and information about their cybersecurity.
As we know, the recently issued SEC proposal would require companies to detail their cybersecurity risks and incidents as well as related books and records for up to five years. Participating in a SOC for Cybersecurity would enable your organization to prepare accordingly with no blind spots. This is especially important if your organization utilizes third-party risk management, a growing concern for many firms due to the increased risk associated with them.
With the SOC for Cybersecurity, you can equip your management, directors, investors, business partners, and other stakeholders with the controls they need to ensure you remain compliant with the SEC’s new additions.
Our perspective
While there have been no updates since the proposed rules, it is important to stay vigilant — not only to protect your organization, but also to maintain compliance. To stay up to date, bookmark the SEC’s Cybersecurity news and our Technology and Cybersecurity insight library.
Professional service firms like MGO help verify you are compliant and strengthen your overall cybersecurity — so these incidents are less likely to occur, and if they do, you will be ready to mitigate risks at once. Let us know if you are ready to assess your cybersecurity or get started on a SOC for Cybersecurity.
For insights tailored to your company and industry, schedule a conversation with our Technology and Cybersecurity team today.
]]>- The SEC has proposed new regulations regarding climate-related disclosures, which impact reporting for public registrants.
- The proposed rules will involve calculating and reporting Scope 1,2, and 3 greenhouse gas emissions.
- If these proposed SEC guidelines are enacted, privately held companies that are contracted suppliers or vendors to public companies will have to report GHG data as part of their Scope 3 calculations.
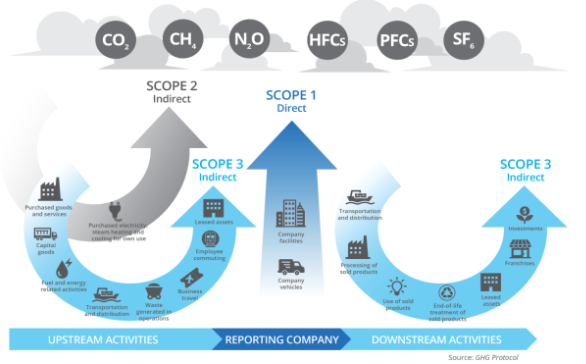
In March 2022, the U.S. Securities and Exchange Commission (SEC) proposed new regulations specific to climate-related disclosures which would impact reporting obligations for public registrants. A key component of the proposed rules (refer to pages 41-45 of the 506 page proposal for the analysis) involves calculating and reporting Scope 1, 2, and 3 greenhouse gas (GHG) emissions.
For anyone unfamiliar with the concept of Scope 1, 2, and 3 GHG emissions, our Environmental, Social and Governance (ESG) practice breaks down what they are, why they are important, and what you can do to start inventorying, measuring, and ultimately reducing your company’s emissions impact.
Understanding the difference between Scope 1, 2 and 3 GHGs
In order to define Scope 1, 2, and 3 emissions, companies must first look to the most common standards and frameworks.
For example, while the International Organization for Standardization (ISO) has provided a general set of standards (through ISO 14064); however, the Greenhouse Gas Protocol (GHG Protocol) has emerged to provide “accounting and reporting standards, sector guidance, calculation tools and trainings for businesses and local and national governments” and has “created a comprehensive, global, standardized framework for measuring and managing emissions from private and public sector operations, value chains, products, cities and policies to enable greenhouse gas reductions across the board.”
Further, the SEC notes on page 34 of their proposed rule, that the GHG Protocol “has become a leading accounting and reporting standard for greenhouse gas [GHG] emissions” with “concepts and a vocabulary that are commonly used by companies when providing climate-related disclosures.”
As such, the SEC has grounded the proposed rules in line with the following definitions established by the GHG Protocol:
Scope 1 GHG Emissions:
Direct emissions that occur from sources owned or controlled by the company – such as fuel combustion from buildings, vehicles, machinery, and other equipment.
Scope 2 GHG Emissions:
Indirect emissions resulting from the generation of electricity purchased and used by the company (derived from the activities of the power provider). This includes purchased electricity, heat, steam, and cooling.
Scope 3 GHG Emissions:
All other indirect emissions which are not captured in the Scope 2 category. Scope 3 emissions are generated as a result of a company’s value chain but are not directly owned or managed by the company. For example:
- Upstream emissions include but are not limited to goods and services purchased from vendors and suppliers; upstream transportation and distribution; business travel; and employee commuting.
- Downstream emissions include but are not limited to transportation and distribution to customers; the processing of sold products; the use of sold products; sold products’ the end-of-life treatment; and investments.
Given the scope and scale, Scope 3 emissions are significantly more complex and time consuming to inventory, calculate, track, and manage compared to both Scope 1 and Scope 2 emissions.
Why measuring greenhouse gas emissions is important
The SEC’s proposed rule has its most immediate impact on public companies; however, private companies that operate in the value chain for public companies impacted by the proposal need to consider their own GHG emissions calculations.
For example, if the SEC guidelines are put in place and include Scope 3 reporting requirements as currently written (i.e., based on materiality or linkage to commitments), privately held companies that are contracted suppliers or vendors to public companies impacted by the proposed rule are likely to receive recurring requests (i.e., at least annually) for complete, accurate, and timely GHG data, which the public company will include as part of their upstream Scope 3 calculation.
As such, an inability to furnish complete, accurate, and timely GHG data may become a barrier for entry to becoming a supplier or vendor to certain public registrants.
Attestation of GHG reporting
With the SEC’s proposed climate-related disclosure rules, GHG emission information will need to be validated through third-party attestation.
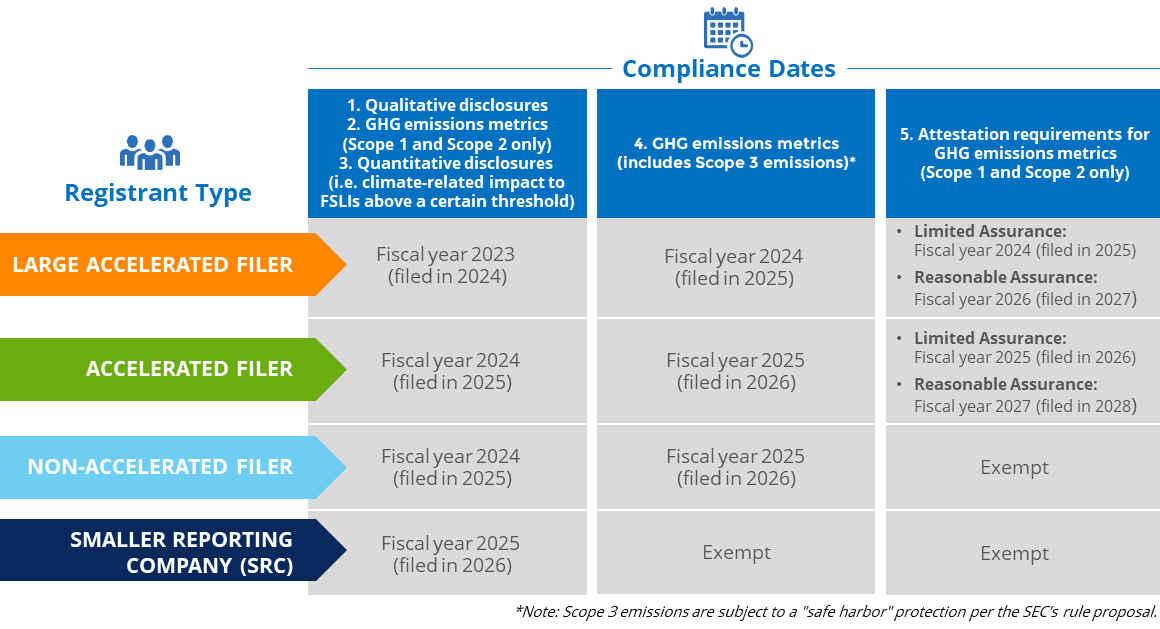
Per the proposed rule, the attestation requirements for GHG emissions metrics would:
- Pertain to Scope 1 and Scope 2 only (i.e., any Scope 3 disclosures would not be subject to the attestation requirement and would be protected through a safe harbor provision)
- Impact large accelerated and accelerated filers only (i.e., non-accelerated and/or smaller reporting companies [SRCs] would not be required to comply with the attestation requirements)
- Define a set of minimum attestation report requirements, including acceptable attestation frameworks
- Include a phase-in period with a compliance date dependent on the registrant’s filing status
It should be noted that the proposed rule also allows impacted registrants to transition into the reasonable assurance attestation requirement by initially subjecting the new GHG emissions disclosures to a limited assurance review. Both reasonable and limited assurance engagement and reporting requirements are defined at length by various organizations (including the AICPA); however, impacted registrants need to understand that a limited assurance review is considered “substantially less in scope” than an examination performed under reasonable assurance (i.e., impacted registrants need to ensure they are taking appropriate steps to ensure that their GHG emissions disclosures are robust, in all material respects).
Greenhouse Gas strategy for state and local governments
Measuring Scope 1, 2, and 3 GHG emissions is not only applicable for businesses — leaders of state and local government institutions are also under growing pressure to inventory, measure, and disclose ESG-related metrics and key performance indicators (KPIs), including GHG emissions disclosures.
As a result, the GHG Protocol has also developed an accounting and reporting standard for cities.
MGO’s perspective
Regardless of your ESG program’s maturity, the definition of value is evolving, and organizations that keep pace are primed for long-term success. If you are interested in inventorying, measuring, and reporting Scope 1, 2, and 3 GHG emissions, contact us to get started.
For insights tailored to your company and industry, schedule a conversation with our ESG team today.
]]>- The SEC has issued a proposal requiring companies to disclose information about corporations’ climate change risks within their filings.
- This proposal includes new requirements for qualitative and quantitative disclosures, attestations, and audit reporting requirements for Scope 1 and 2 Greenhouse Gas emissions.
- The SEC’s goal in creating this new proposal is to drive greater transparency from registrants to protect investors and solidify climate-related disclosures as required reporting.
On March 21, 2022, the U.S. Securities and Exchange Commission (SEC) issued a proposed rule that would require registrants to include climate-related disclosures within registration statements and annual reports (including Form 10-K). According to SEC Chair Gary Gensler, the rule is intended to promote transparency and protect investors, providing them with “consistent, comparable, and useful information for making their investment decisions.”
With a 3-1 passing vote, the SEC’s formal proposal has now opened a public comment period which seeks responses from the impacted companies, accounting firms, and the public at large (note the comment period will end on May 20, 2022, or 30 days following the publication in the Federal Register, whichever is later).
While updates to the proposed regulations are likely to follow the closure of the comment period, it is already evident that mandatory climate-related disclosures are close. Further, given the complexity of the proposal, it is apparent that registrants will experience increased costs driven by new governance and reporting requirements – and these costs could extend through the registrant’s entire value chain (including upstream suppliers and downstream customers).
MGO’s Environmental, Social and Governance (ESG) practice has inspected the proposed rules and provides a summary and contextual overview in the following paragraphs.
Note: The complete, 506-page SEC proposal is viewable here, while a 3-page summary fact sheet is viewable here.
SEC proposed climate disclosure requirements
Through its independent research of 6,644 annual filings, the SEC found that many companies were already disclosing both qualitative and quantitative metrics related to climate change (i.e., on a voluntary basis). Additionally, the SEC found that a subset of those companies was doing so in line with two of the most common frameworks and standards:
- Task Force on Climate-Related Financial Disclosures (TCFD) – The framework primarily used by companies that make qualitative, climate-related disclosures around governance, strategy, and risk management as well as certain quantitative disclosures (i.e., the metrics and targets used by a company to measure and assess climate risks, opportunities, and targets)
- Greenhouse Gas Protocol – The standardized framework used by most organizations to inventory, calculate, and manage greenhouse gas (GHG) emissions (i.e., the quantitative disclosures commonly referred to as Scope 1, Scope 2, and Scope 3 GHG emissions)
At the highest level, the proposal’s new disclosure requirements include:
- New qualitative disclosures (under Regulation S-K) in a separate, captioned section of the annual filing, including but not limited to descriptions of:
- The governance of climate-related risks (e.g., board and management oversight)
- Material climate-related impacts on strategy, business model, and outlook
- Approaches to climate-related risk management
- GHG emissions metrics (e.g., Scope 1, Scope 2, and potentially Scope 3 emissions)
- Climate-related targets and goals, if any (e.g., net-zero commitments)
- Usage of an internal carbon price and how this price was determined
- New quantitative disclosures (under Regulation S-X) included as a note within the audited financial statements, including:
- Disaggregated information about the climate-related impacts, events, and transition activities to existing financial statement line items (FSLIs) above a certain threshold (e.g., increases to reserves, impairment charges, expenditures specific to transition activities, etc.)
- Incremental attestation and audit requirements
- Scope 1 and Scope 2 GHG emissions disclosures (under Regulation S-K) would be subject to an attestation requirement; however, the disclosures would initially be subject to an audit under the limited assurance standard and followed by an audit under the reasonable assurance standard two years later
- Climate-related impacts, events, transition activities, etc. to existing FSLIs would be subject to existing audit requirements (i.e., consistent with procedures performed over historical financial statement footnotes, including internal controls over financial reporting [or ICFR])
When would the proposed climate-disclosure updates go into effect?
Under the proposed rule (which is subject to change after the comment period), domestic and foreign registrants would be required to adhere to the following phase-in timelines:
MGO’s perspective
Through our experience to date, and corroborated through the review of the SEC’s analysis of 6,644 annual filings (refer to pages 311-320 of the 506 page proposal for the analysis), many registrants across all industries are already voluntarily disclosing climate-related information. However, for the companies that have not yet moved to establish climate-related governance, evaluate their existing business strategies, analyze the emerging risks, or inventory the data required for climate-related metrics, the compliance effort is expected to be considerable.
In the end, the SEC’s goal with the proposed rule appears to be two-fold:
- The first is to drive transparency from registrants to protect investors. As many issuers already disclose climate-related information voluntarily, standardizing the requirements will provide more comparable information while reducing compliance costs in the long run
- The second is a recognition that climate-related disclosures are not only here to stay but set to grow in importance in the coming decades. Given that anticipated growth, the SEC’s proposal will ensure the US regulatory environment is able to keep pace — especially with its international counterparts
Regardless of your company’s current maturity as it relates to climate governance, strategy, risk assessment, and disclosure, the time to act is now. Rule proposals of this scale and complexity from the SEC are infrequent, and with international regulators looking to adopt their own sustainability disclosure requirements (see the IFRS Foundation’s Sustainability Disclosure Standards draft released on March 31, 2022), we expect the path to compliance will be long and ambiguous for many.
Lastly, while the proposal is intended for public registrants, we believe that private companies also need to begin to mobilize. As an example, if a private company operates as a vendor or supplier for a Large Accelerated filer with Scope 3 emission reporting ambitions, the privately held vendor or supplier can expect that Large Accelerated filer to request timely and quality Scope 1 and/or Scope 2 GHG data to serve as an input into the filer’s Scope 3 calculation (inclusive of questions around the completeness and accuracy of data).
Questions to consider about the SEC’s proposed ESG ruling
- Who is responsible for governance and oversight (at both the board and management level) of climate-related risks and opportunities?
- Which climate-related frameworks and/or standards has the company considered adopting or are already following for existing disclosures?
- Are existing qualitative and quantitative climate-related disclosures robust (i.e., considered investor-grade)?
- Are there sufficient processes and controls in place to ensure climate-related disclosures are complete, accurate, and timely?
- Is a communication plan in place to make employees aware of climate-related risks, opportunities, commitments, and progress?
- Does the board understand why ESG-related information (which is broader than the information in the climate-disclosure proposal) is important to investors and other stakeholders?
Regardless of your ESG program’s maturity, the definition of value is evolving, and organizations that evolve with it are primed for long-term success.
For insights tailored to your company and industry, schedule a conversation with our ESG team today.
]]>Under this Act, foreign companies traded on any U.S. exchanges are required to have their auditors submit to inspection by the Public Company Accounting Oversight Board (PCAOB) in an effort to establish that they’re neither owned nor controlled by a foreign government. With a wealth of Chinese companies trading in the U.S., the legislation is likely to have a significant impact on Chinese companies and their accounting firms, as well as U.S. investors and the capital market, for years to come.
How the HFCAA works
The Act will amend Section 104 the Sarbanes-Oxley Act of 2002, the comprehensive legislation passed by Congress aimed at overseeing the conduct of public companies. Pursuant to the HFCAA, there will be a number of sizable changes.
• First, the Securities and Exchange Commission (SEC) will now be required to identify companies that are utilizing registered public accounting firms located outside the United States that are preventing audits from the PCAOB.
• Additionally, the SEC must prohibit securities trading of these public companies within U.S. markets following three consecutive years of non-inspection. Under the language of the bill, these companies will be prohibited from trading on either a national securities exchange or “through any other method that is within the jurisdiction of the Commission to regulate, including through the method of trading that is commonly referred to as the ‘over-the-counter’ trading of securities.” It should be noted that in the event an issuer receives a trading prohibition, then the issuer is allowed to have the prohibition overturned as long as it is able to retain an accounting firm that can be fully inspected by the PCAOB.
• Also, as part of the Act, there are disclosure requirements for non-inspection years for foreign issuers of securities that utilize firms to prepare audit reports. For instance, they will need to disclose the percentage of shares owned by foreign government entities. They will also need to disclose whether or not foreign government entities have “controlling financial interest with respect to the issue.”
• Finally, there are also disclosure requirements that specifically involve China. According to the Act, the names of each official of the Chinese Communist Party of the board of directors of either the issuer or “the operating entity with respect to the issuer” must be disclosed in their Form 10-K, Form 20-F, and shell company reports. Additionally, it must be disclosed if the issuer’s articles of incorporation (or “equivalent organizing document”) has “any charter of the Chinese Communist Party, including the text of any such charter.”
Potential impact of the HFCAA
While the HFCAA applies to any U.S.-listed company incorporated outside the United States, including Mainland China, Hong Kong, France, and Belgium, it is generally understood as explicitly targeting Chinese companies under the restrictions imposed by the Chinese government.
This Act could lead to an increase in the number Chinese and Hong Kong-based issuers being delisted from U.S. exchanges in the coming years. In fact, according to the list of public companies affected by obstacles to PCAOB inspections, there are more than 200 Chinese companies currently audited by CPA firms in mainland China and Hong Kong that would be negatively impacted. These companies, including popular stocks such as Alibaba Group Holding Ltd – ADR, Baidu Inc, JD.com Inc, and Nio Inc – ADR, could feel the brunt of this new legislation.
Note that the Big Four accounting firms in China are independent from the Big Four in the U.S. and do not meet the audit requirements of the PCAOB since they are under the China’s national security laws and the Chinese Securities Law, which prohibit Chinese companies from providing records “relating to securities business activities” overseas without approval by the Chinese securities regulator. Besides, the imminent enactment would certainly discourage new listing of Chinese companies in the U.S. as it could result in a discount on the trading prices as investors may factor in the potential de-listing risk.
However, it remains to be seen how the SEC implementation will roll out within 90 days of the HFCAA’s enactment, which could be greatly influenced by the new leadership of the SEC. According to Bloomberg, President-elect Joe Biden is expected to pick Gary Gensler to head the SEC.
Additionally, because of the three-year compliance timeline in the Act, Chinese companies may consider several options to mitigate the impending risks. The most likely one is to engage a reputable U.S.-based CPA firm, preferably one that has an established China Group, who understands both the Chinese business climate and the U.S. accounting rules, and most importantly obtain a clean compliance record with PCAOB. Yet, it’s also critical that companies consider other factors such as the investor and make sustainable long-term plan to maintain a legitimate and confident position in US capital markets.
If you have any questions
MGO’s SEC practice has a dedicated China Group experienced with Chinese IPOs, RTOs, M&A deals and the unique characteristics of SPAC acquisitions. To understand your options, and the path ahead, please feel free to reach out to us for a consultation.
As one of the largest, and fastest-growing stock exchanges in the world, the Nasdaq is a highly-sought after destination for foreign companies seeking access to U.S. public markets. While there will be more rules dictating eligibility for issuing IPOs on the Nasdaq, it is MGO’s interpretation that these changes are not retributive but are instead designed to simply increase transparency and accountability to protect the investor community.
It is our hope that companies from China, and other affected countries, are not discouraged by these new rules and, in fact, feel emboldened. These new rules give companies bright lines in order to have a successful offering and will eliminate much of the subjectivity around the qualifications to go public. With these guidelines in place, issuances that meet the new Nasdaq requirements are expected to be enthusiastically embraced by an investor community with greater confidence that their money is in safe hands.
In the following we will explore the new rules, what they mean, and steps affected companies considering an IPO should take to prepare.
What are “Restrictive Markets?”
At the center of the Nasdaq’s proposed listing requirement changes is a new definition of “Restrictive Markets,” which defines the regions and companies affected by the new rules. According to the Nasdaq’s public notice to the SEC, Restrictive Markets are defined as:
“a jurisdiction that Nasdaq determines to have secrecy laws, blocking statutes, national security laws or other laws or regulations restricting access to information by regulators of U.S.-listed companies in such jurisdiction.”
To determine whether a company is based in a Restrictive Market, Nasdaq will consider the primary location of:
- Principal business segments, operations or assets;
- Board and shareholders’ meetings;
- Headquarters or principal executive offices;
- Senior management and employees; and
- Books and records.
Nasdaq will take a holistic approach to assessing these factors and determining whether a company is based in a Restrictive Market, bearing in mind that a company’s headquarters may not be the office from which it conducts its principal business activities.
This definition (and pursuant rules) would apply to both foreign private issuers based in Restricted Markets and companies based in other jurisdictions that principally administer their businesses in Restricted Markets.
Nasdaq has not officially provided a list of jurisdictions they consider Restrictive Markets.
The details of proposed Nasdaq rules changes
Rule #1: Additional Listing Criteria for Restrictive Market Companies
- For an IPO: A Restrictive Market company must offer a minimum amount of securities totaling at least $25 million; or 25% of the company’s post-market value.
- For a Business Combination: A Restrictive Market company to have a minimum market value of unrestricted publicly held shares following the business combination equal to the lesser of: $25 million; or 25% of the post-business combination entity’s market value of listed securities.
- For a Direct Listing: A Restrictive Market company is only permitted to list on the Nasdaq Global Select Market or Nasdaq Global Market in connection with a Direct Listing.
Reasoning: This rule represents the first time the Nasdaq has created minimum values for an IPO. The Nasdaq justifies the move by commenting that small offerings often do not reflect the true value of the company, and a lack of liquidity can create opportunities for price manipulation, and may make issuances unappealing to institutional investors and the secondary market.
Impact: For over a decade, smaller Chinese companies have pursued IPOs as a liquidity/exit event that provides access to U.S. dollars. The Nasdaq only wants companies genuinely seeking to raise capital and trade shares. Chinese companies only seeking a limited liquidity event will be turned away if they do not meet the float percentage requirements.
Rule #2: “Restricted Market” companies must have senior management or a director with experience with U.S. regulatory and reporting requirements, Nasdaq rules, and federal securities laws. Currently listed companies will have a period to get in compliance, while IPOs must have this member on the leadership team. Compliance will be on-going.
Reasoning: A number of corporate governance issues have created scandals and other disruptions that have cost U.S. investors millions, if not billions, of dollars. By requiring that a member of senior-level management have a qualified understanding of regulatory, reporting and securities laws, Nasdaq intends to ensure there is institutional understanding of applicable rules and requirements.
Impact: Many businesses seeking to go public on the Nasdaq will likely already have a member of leadership with this experience. And if they don’t, rule or not, they certainly should. Nasdaq’s proposed rules allow for an advisory role that meets their standards. This position will be expected to provide on-going guidance related to corporate governance, internal controls, and other securities law concerns.
Rule #3: More stringent criteria for auditors of companies (not only Restrictive Market) applying for IPOs or that are already listed. These criteria include:
- Auditor must be subject to PCAOB inspections.
- Auditor must pass PCAOB inspections, sufficiently respond to inspection requests, and not have significant deficiencies in their conduct or systems of quality controls, as observed by the PCAOB.
- Auditor must be able to demonstrate that it has adequate personnel participating in the audit with expertise applying U.S. GAAP, GAAS or IFRS, as applicable, in the company’s industry.
- Auditor’s training program for personnel participating in a company’s audit is adequate;
- For non-U.S. auditors, whether the auditor is part of a global network or other affiliation providing sufficient, globally common technologies, tools, methodologies, training and quality assurance monitoring.
- Auditor must demonstrate to Nasdaq it has sufficient resources, geographic reach, or experience as it relates to the company’s audit.
Reasoning: Audit quality is at the center of investor confidence in a company and its listed shares on the Nasdaq. Implementing greater controls and expectations for audit providers is a no-nonsense approach to both improving the reliability of listed securities, and improving investor confidence.
Impact: This rules applies to all companies listed on the Nasdaq, and is not specific to Restricted Market entities. The result will simply be greater demand for qualified audit providers that have the expertise, global reach, and sufficient quality controls.
In conclusion
In a year of unprecedented global market disruption caused by external factors, and with the high profile Luckin Coffee accounting scandal rocking investor confidence, Nasdaq’s proposed rule changes are common sense steps toward creating greater transparency and accountability for all listed companies, and especially those originating in countries with laws limiting transparency.
The ultimate goal of these rules and their enforcement is to provide greater stability for both companies and investors. The former must only take the time to carefully consider their path to the IPO and engage qualified auditors and advisors familiar with Nasdaq rules, SEC laws and international reporting requirements.
]]>