- Internal controls, especially around fraud prevention, are essential for limiting losses, driving efficiency, improving accountability, and boosting company value during investments or M&A deals.
- The “tone at the top” from leadership in fostering an ethical environment, along with proper segregation of duties, are key elements for fraud prevention and strong internal controls.
- Well-established policies and procedures, like Delegation of Authority rules and restricted system access protocols, are also vital for maintaining adequate controls to enable company growth.
~
As the economy stands on shaky legs, private equity and venture capital firms are necessarily careful and strategic when assessing potential investment opportunities. Whether your long-term plan includes acquiring another company, selling your business, or seeking new capital, strengthening your internal control environment — with a focus on preventing fraud — is a powerful way to increase actual and perceived value.
In the following, we will lay out the reasons why fraud prevention is an essential element to proper corporate governance and illustrate key areas to examine whether your internal control environment is built to help your operation succeed.
The Importance of Internal Controls in Fraud Prevention
A robust internal control system is the first step toward managing, mitigating, and uncovering fraud. A strong internal control environment will:
Protect your company’s assets by reducing the risk of theft or misappropriation of cash, inventory, equipment, and intellectual property.
Detect fraudulent activities or irregularities early on and deter employees from attempting fraud in the first place.
Provide cost savings by limiting opportunities for financial losses, costly investigations, and legal expenses associated with fraud.
Drive operational efficiency by providing clear processes and guidelines that reduce the risk of errors or inefficiencies in day-to-day operations.
Improve employee accountability by implementing checks and balances that discourage unethical behavior.
When seeking an investment or undertaking a significant M&A deal, you should have a firm grasp of the strength and quality of your internal control environment. Not only will you reduce the risk of fraud in the near term, but you will also cultivate confidence with potential investors and M&A partners.
Fraud Prevention Starts with the “Tone at the Top”
The first key element to look for in measuring the strength of your internal controls is ensuring a clear and proactive “tone at the top”, meaning an ethical environment fostered by the board of directors, audit committee, and senior management. A good tone at the top encourages positive behavior and helps prevent fraud and other unethical practices.
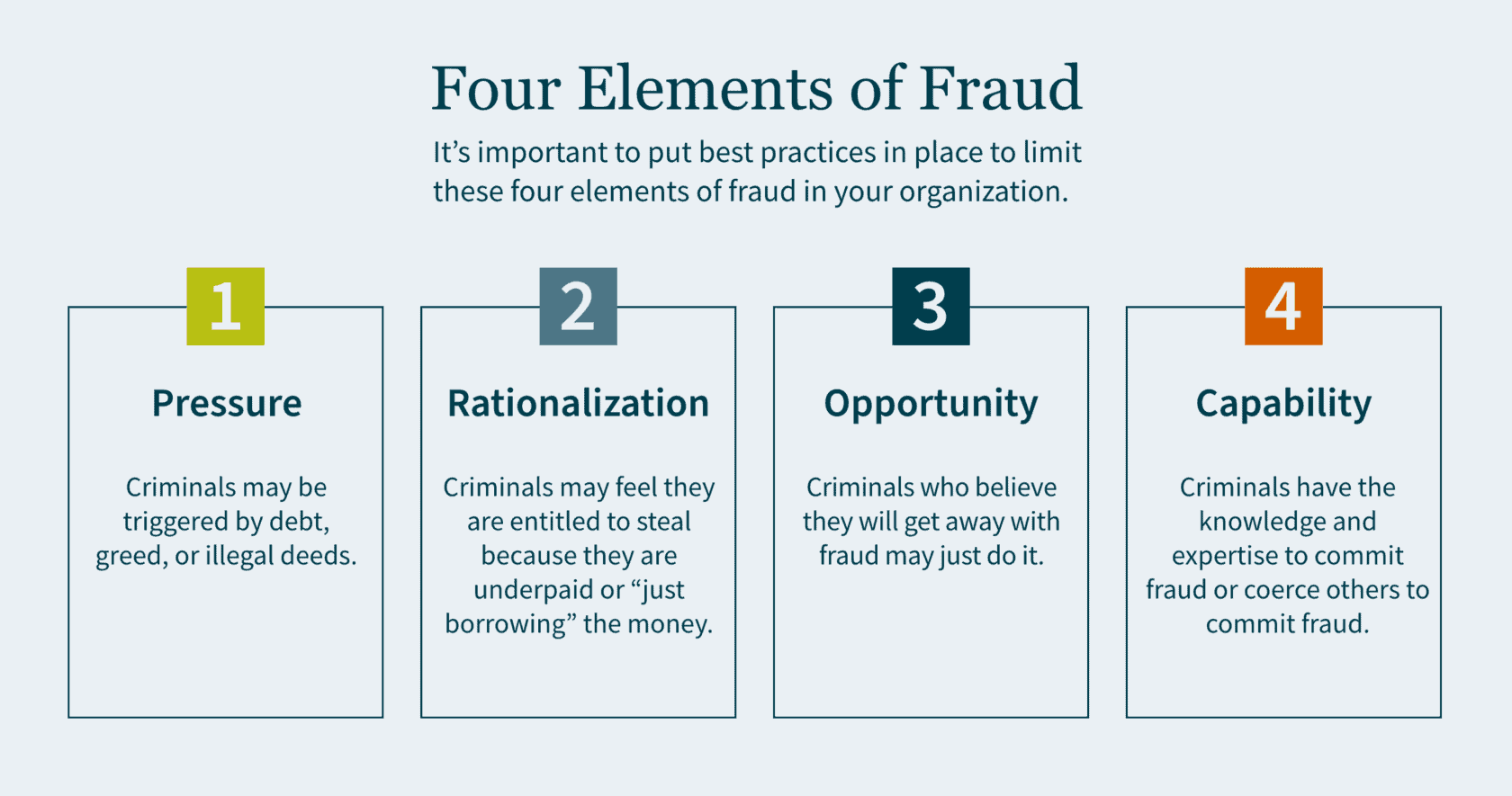
There are four elements to fraud: pressure, rationalization, opportunity and capability.
Pressure motivates crime. This could be triggered by debt, greed, or illegal deeds. Individuals who have financial problems and commit financial crimes tend to rationalize their actions. Criminals may feel that they are entitled to the money they are stealing, because they believe they are underpaid. In some cases, they simply rationalize to themselves that they are only “borrowing” the money and have every intention of paying it back.
Criminals who can commit fraud and believe they will get away with it may just do it. Capability means the criminal has the expertise as well as the intelligence to coerce others into committing fraud. The board of directors is responsible for selecting and monitoring executive management to ensure best practices are in place to limit the motivations of all four elements of fraud.
Proper Segregation of Duties for Internal Controls
The second key element to look for in your internal controls is a well-established segregation of duties. The idea is to establish controls so that no single person has the ability that would allow them the opportunity to commit fraud. Companies must make it extremely difficult for any single employee to have the opportunity to perpetrate a crime and subsequently cover it up.
Fraud Controls
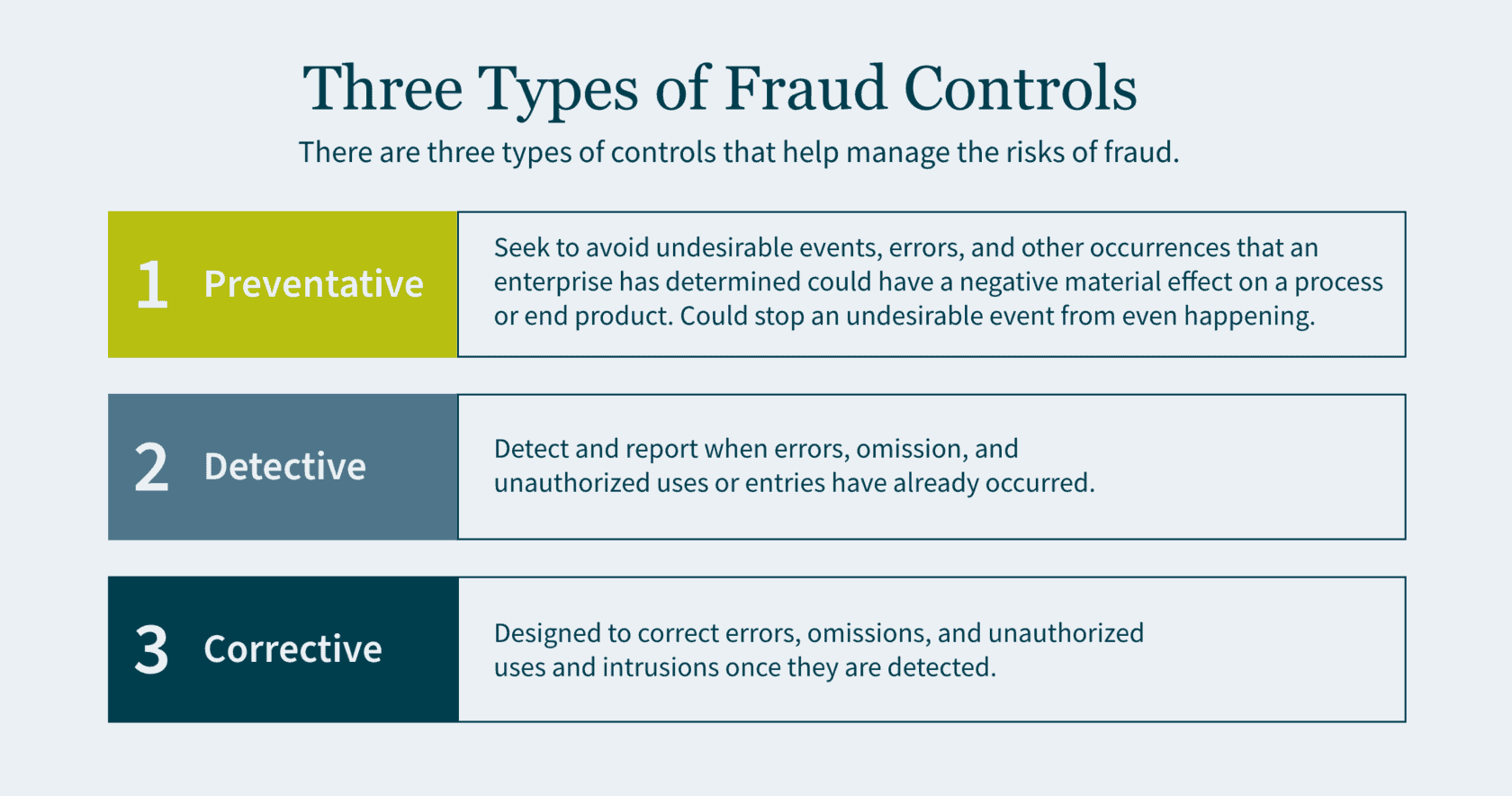
There are three types of controls that help manage the risks of fraud: preventative, detective, and corrective.
- Preventative controls seek to avoid undesirable events, errors, and other occurrences that an enterprise has determined could have a negative material effect on a process or end product. Preventative controls are the best of the three as they are the first line of defense and a backstop to fraud. If designed correctly, preventative controls stop an undesirable event from even happening.
- Detective controls exist to detect and report when errors, omission, and unauthorized uses or entries have already occurred. Although it is important to identify these adverse events, you are doing so after the fraud has already been committed.
- Corrective (also referred to as compensating) controls are designed to correct errors, omissions, and unauthorized uses and intrusions once they are detected.
Preventing Misappropriation of Assets
An important component of segregation of duties is to prevent the misappropriation of assets and reduce fraud risk. Below are some examples of best practices for various types of assets:
- Cash Receipt: segregate the receipt of cash/checks and the recording of the journal entry in the accounting system into two roles.
- Accounts Receivable: segregate the responsibilities of recording cash received from customers and providing credit memos to customers. (If one person performs both functions, it creates the opportunity to divert payments from the customer to the employee and then cover the theft with a matching credit to the customer’s account).
- Cash Reconciliation: the individuals who authorize, process, or record cash should not perform the bank reconciliation to the general ledger.
- Inventory: individuals who order goods from the suppliers should not have the ability to log the goods received in the accounting system.
- Payroll: segregate the responsibilities of compiling gross and net pay for payroll, with the responsibilities of verifying the calculation. (If a single individual performs both functions, it allows for the opportunity to increase personal compensation and the compensation of others without authorization. It also provides an opportunity to create a fictitious payee and make corresponding payroll checks).
The Importance of Policies and Procedures
The third key element to look for in your investees is well-established policies and procedures. Make sure that any company you consider acquiring has basic policies and procedures in place, such as Delegation of Authority (DOA).
The DOA is a policy where the executive team delegates authority to the management of the company. Individuals should be considered appropriate to fulfill delegated roles and responsibilities. The DOA should be reviewed at least annually. Subsequently, it is important to ensure that the DOA is being followed, and that approvals do not deviate from it. Any such anomalies should be rare and, when they do occur, they need to be reviewed and approved. Constant deviations from the DOA may be a sign that the DOA needs to be restructured.
A second essential policy and procedure is restricted computer and application access. This is to protect sensitive company financials and proprietary data. The company should have a robust control environment and maintain computer logins and password access on a need-to-know basis. Access should only be granted by the owner of the application or system and subsequently logged by the administrator. Now more than ever companies are hiring remote employees. This shift in the dynamic workspace further emphasizes the need for a quality IT controls environment.
How We Can Help
As you prepare your company for future growth, getting an impartial third-party opinion on your internal control environment can be a powerful tool for finding gaps and inefficiencies, and implementing value-added changes.
Our dedicated Public Company teams offer a deep level of industry experience and technical skills. We can help prepare your company for a major capital raise, including going public via an IPO or RTO. Or we can help optimize value for an M&A deal, whether you are buying or selling. Contact us today to access an external, holistic vision focused on helping you grow and succeed
]]>- A growing organization is a positive, but along with it usually comes increasingly complex financial accounting.
- Outsourcing provides businesses of all sizes with an opportunity to manage an array of issues — from staffing shortages or a lack of specific expertise to disorganized or unsecure financial records.
- Benefits of outsourcing include significant cost savings, direct access to specific accounting knowledge, the minimization of turnover, the ability to scale, access to tools and processes, and flexibility.
Many CEOs and business leaders are experiencing challenges in the aftermath of the COVID-19 pandemic, including changing customer trends, aggressive competition, emerging digital technologies, and the new normal of employee expectations for workplace flexibility.
These uncertain economic forces and cultural shifts are putting increased pressure on staffing for organizations of all sizes – especially fast-growing ones. While these difficulties are difficult to overcome, they are also an opportunity to change the “status quo” and level-up back-office performance.
For leaders navigating the uncertain tailwinds of the pandemic and planning to enter a new era of growth, outsourcing represents a powerful opportunity to address any staffing issues or business challenges. It empowers you to access specialized insight on a temporary basis, create value ahead of a major transaction, manage overhead costs, and modernize and revitalize business processes.
A recent study showed that 59% of all businesses utilize outsourced resources and that accounting is the most commonly outsourced function. So, how do you know if outsourcing your accounting function is right for your organization?
In this article we’ll look at five indicators that this strategy might be right for you and detail the key benefits to outsourcing or augmenting your accounting function.
Five signs your business may benefit from outsourced accounting

Here are some questions you should ask yourself to determine if your organization would benefit from outsourced accounting services:
- Is your business growing rapidly?
If you’re experiencing a significant influx of revenue, first off, great work! Your business model is proving out and you’re on the fast-track to success. But what is happening to your expenses, profitability and working capital? Depending on your answer it could mean that your accounting needs are evolving, the risks of a breakdown are higher, and overall, there is simply more at stake. It may be time to confirm that your current in-house team is qualified and staffed appropriately to handle these new responsibilities.
- Are you struggling to keep up with your accounts receivable or payroll?
One way to get a firm answer to whether your team is understaffed is if you’re missing key deadlines or struggling to get timely collection of cash from your accounts receivable. The inability to collect and follow-up on AR is essential to funding current and future growth and is directly connected to meeting your payroll commitments – one of the largest expenses of any business. If anything falls behind, you can find yourself in a difficult position if you do not have the ability to access cash or financing.
- Are your financial records organized and producing usable data?
Your accounting function does more than compliance, it should help guide your organization’s financial hygiene. Organized financials tell a clear story of earnings, spending, and investment, so you can make informed decisions. An over-worked or inexperienced accounting team will be working furiously to keep up with compliance and may not have the capacity, or necessary experience, to provide guidance on your financial scorecard to accrete value to the organization.
- Do your accounting needs fluctuate significantly throughout the year?
If your business experiences big shifts in labor productivity based on the calendar year and your taxes filings are late with significant overages from the tax preparers, or your audits have a significant number of adjustments, that may mean your accounting team lacks capability. Striking the right balance between hiring quality talent and the speed of bringing new hires up to date with company procedures can be a challenge. Outsourcing your team can deliver the resources you need, when you need them, and limit costs during the slower periods.
- Are you concerned about financial security and checks and balances?
If your internal accounting team is one or two individuals, you may be open to hidden risks. An independent team can provide the checks-and-balances that help mitigate the risk of fraud and asset misappropriation.
If you answered yes to any of these questions, you should consider outsourcing part or all of your accounting function. With an outsourced accounting team, you gain immediate access to trained, knowledgeable staff with the knowledge you need in technical accounting. The right outsourced resources can help your business grow faster and run more smoothly — often at a lower price than building an internal accounting department.
Benefits of outsourced accounting services
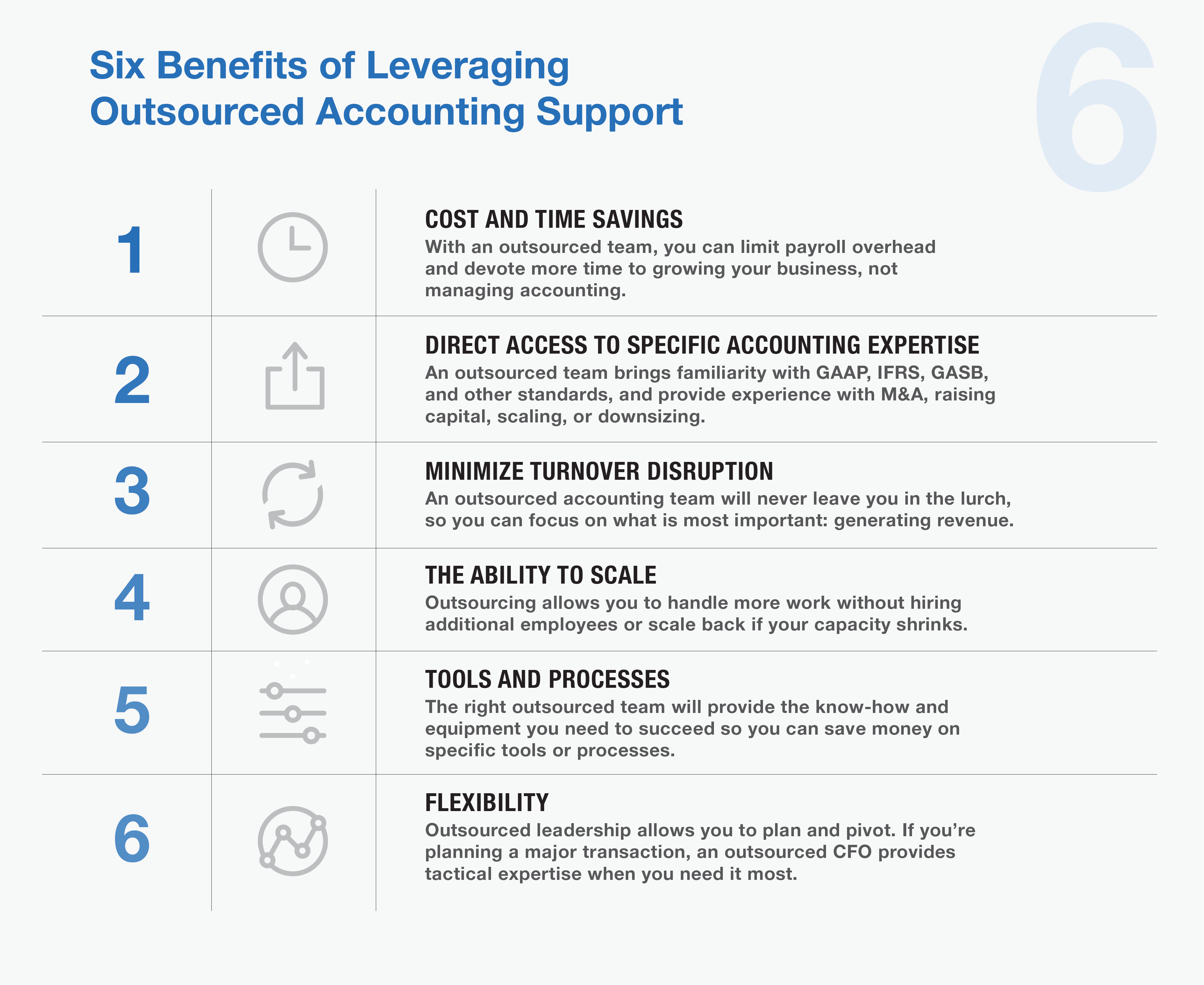
1.Cost and time savings
Maintaining full-time employees can be costly — and for most organizations, labor costs are some of the highest expenses. By relying on an outsourced team, you can devote your time to growing your business and spend less time managing accounting.
- Direct access to specific accounting expertise
Every company is different, which means every company’s needs are different. By outsourcing, you have access to the service you need when you need it. An outsourced team will bring familiarity with an array of accounting and reporting standards, including GAAP, IFRS, GASB, etc. Plus, they can provide specific experience with M&A transactions, raising capital, scaling, or downsizing operations.
- Minimize turnover disruption
In a smaller organization, each employee is vital to the business’s success. When you lose one, the disruption left in their wake can provide additional challenges. An outsourced accounting team will never leave you in the lurch, so you can focus on what is most important: generating revenue.
- The ability to scale
If your organization has grown quickly, you may experience growing pains when your fortunes suddenly shift. In boom times, you may need to hire more staff to meet demand. But that also means you may find yourself laying off employees in a downturn. Outsourcing allows you to handle more work without hiring additional employees or scale back if your capacity shrinks.
- Tools and processes
No matter what your organization’s size, you should always try to keep your overhead costs minimal. By outsourcing, you can save money on specific tools or processes you might otherwise need to function. The right outsourced team will provide the know-how and equipment you need to succeed.
- Flexibility
By outsourcing certain jobs, you can plan — and pivot, as needed — depending on your organization’s needs. This is especially relevant in the case of needing specialized guidance. If you’re planning a major transaction or other market move, an outsourced CFO can provide tactical expertise when and where you need it.
MGO can help
As your organization grows, your financial accounting needs become increasingly complex. Because your in-house accountants may be limited to handle the basics, outsourcing to professional teams with specialized knowledge and experience can provide precisely the kind of service you require — and give you the time you need to focus on the organization’s other needs.
MGO has a robust outsourced accounting team staffed by CPAs with diverse industry background and technical specialties. We’ll provide the right-size solution to your organization’s needs. Areas we support include day-to-day accounting tasks, complex financial systems projects, regulatory compliance demands, and support for M&A deals, raising capital, and other major transactions.
Whether you’re interested in simply augmenting your team with additional financial knowledge, or undertaking a complete accounting transformation, we can help you with the people, processes, and technology you need to move your business forward.
To explore your options and start along the path to organizational change, contact us.
]]>- Expectations around sustainability and corporate social responsibility are becoming increasingly ubiquitous in the lives of customers, employees, and investors.
- Traditional private equity (PE) houses are increasingly considering ESG risks and incorporating opportunities for value creation across the due diligence and investment cycles.
- While the focus on specific ESG activities varies, there is a growing consensus that a structured approach to risk assessment and reporting is necessary to both create new value and protect existing value.
Private equity sees value in ESG
The private equity industry continues to push through the ambiguity surrounding ESG criteria to navigate risks and discover opportunities to increase investment returns. While many traditional PE houses are taking the “wait and see” approach, those that are proactive about integrating ESG considerations into their due diligence and investment cycles are being rewarded.
Regardless of the approach, the confluence of risk mitigation, opportunities for growth, expected regulation, and customer demand make it clear that ESG will be playing a critical role in short- and long-term value creation.
ESG: The shift from “nice” to “need.”
Private and public companies alike have been taking stock of their ESG risks and ramping up their ESG strategies for some time. What was once considered a “nice to have” has become table stakes for companies of all shapes and sizes looking to meet shifting stakeholder demands. Therefore, the most progressive private equity firms have incorporated ESG considerations (i.e., risks and opportunities) throughout all aspects of the investment lifecycle (i.e., due diligence, investment, exit). As “The Expanding Case for ESG in Private Equity” report from Bain & Company highlights:
“Firms recognize that consumers, regulators, employees, and sources of capital are energized by the notion that investors can and should use their economic clout to address the many existential crises we face as a society. Each of these groups is ramping up demands for change and, in many cases, rewarding it.”
While it’s clear that stakeholder demand is embedding ESG criteria into the investment lifecycle, there is still uncertainty surrounding how to measure and monitor ESG risk exposure and opportunities for growth.
Navigating ESG risks and developing new opportunities
A company’s ability to “tell its ESG story” has become synonymous with measuring ESG program maturity. Furthermore, the ability to take traditional business models and drive them towards sustainability-focused principles has been seen to unlock new business opportunities and create long-term value (i.e., loyalty) from consumers. This is especially true for the youngest consumers entering the period of their lives where they will have the most spending power.
To measure risk and develop new opportunities, PE firms are driving portfolio companies to:
- Identify or reassess priority ESG criteria (i.e., those which carry the highest impact for their industry); and
- Establish goals that can be measured and reported to internal and external stakeholders.
To accomplish this, an organization should adopt a structured approach that follows the most common frameworks and standards. Specifically, companies can increase the quality of their ESG program by adopting the most common standards and frameworks (e.g., Sustainability Accounting Standards Board (SASB) or Task Force on Climate-Related Financial Disclosures (TCFD)).
With a structured approach and quality reporting mechanisms, PE firms can continue to integrate ESG elements into portfolio companies throughout the investment lifecycle. By adhering to the most common standards, portfolio companies will be well positioned to comply with expected global regulatory changes.
Building and strengthening your ESG story
Whether you’re an acquisition target company or an established private equity house, a clear ESG strategy is needed to address shifting stakeholder demands. PE firms that have embraced the development of ESG strategies for themselves as well as their portfolio companies are poised to benefit from the changes on the horizon being driven by both stakeholders, customers, and regulation.
ESG’s value proposition may be clear, but a few questions remain as firms embrace ESG principles and build out their programs:
- Are your ESG strategy and expectations clear for your firm, portfolio companies, and investment targets?
- How have you integrated ESG into your value transformation processes for your portfolio companies?
- Does your ESG story convey a mature ESG program?
- By understanding where you are today in the ESG realm, you may be able to embrace the opportunities that are quickly developing.
If you are interested in learning more, schedule a conversation with our ESG team today.
]]>Private organizations, while not always smaller, often have limited resources in specialty areas, including accounting for income tax. This resource constraint —the work being done outside the core accounting team — combined with the complexity of the issues, means private companies are ideal candidates for, and can achieve significant benefit from, internal controls enhancements. Thinking beyond the present, the following are five reasons private companies may want to adopt public-company-level controls:
1. Future Initial Public Offering (IPO) – Walk before you run! If the company believes an IPO may be in its future, it’s better to “practice” before the company is required to be SOX compliant. A phased approach to implementation can drive important changes in company culture as it prepares to become a public organization. Recently published reports analyzing IPO activity reveal that material weaknesses reported by public companies were disproportionately attributable to recent IPO companies. Making a rapid change to SOX compliance can place a heavy burden on a newly public company.
2. Merger and Acquisition Deals – If the possibility of the company being sold to an M&A deal exists, enhanced financial reporting controls can provide the potential buyer with an added layer of security or comfort regarding the financial position of the company. Further, if the acquiring firm has an exit strategy that involves an IPO, the requirement for strong internal controls may be on the horizon.
3. Rapid Growth – Private companies that are growing rapidly, either organically or through acquisition, are susceptible to errors and fraud. The sophistication of these organizations often outpaces the skills and capacity of their support functions, including accounting, finance, and tax. Standard processes with preventive and detective controls can mitigate the risk that comes with rapid growth.
4. Assurance for Private Investors and Banks – Many users other than public shareholders may rely on financial information. The added security and accountability of having controls in place is a benefit to these users, as the enhanced credibility may impact the cost of borrowing for the organization.
5. Peer-Focused Industries – While not all industries are peer-focused, some place significant weight on the leading practices of their peers. Further, some industries require enhanced levels of security and control. For example, cannabis companies with a heavy regulatory burden, industries with sensitive customer data like lifesciences, and tech companies that handle customer data, often look to their peer group for leading practices, including their control environment. When the peer group is a mix of public and private companies, the private company can benefit from keeping pace with the leading practices of their public peers.
Private companies are not immune from the intense scrutiny of numerous stakeholders over accountability and risk. Companies with a clear understanding of the inherent risks that come from negligible accounting practices demonstrate their ability to think beyond the present, and to be better prepared for future growth or change in ownership.
]]>Deal structure can be viewed as the “Terms and Conditions” of an M&A deal. It lays out the rights and obligations of both parties, and provides a roadmap for completing the deal successfully. While deal structures are necessarily complex, they typically fall within three overall strategies, each with distinct advantages and disadvantages: Merger, Asset Acquisition and Stock Purchase.
In the following we will address these options, and common alternatives within each category, and provide guidance on their effectiveness in the cannabis and hemp markets.
Key considerations of an M&A structure
Before we get to the actual M&A structure options, it is worth addressing a couple essential factors that play a role in the value of an M&A deal for both sides. Each transaction structure has a unique relationship to these factors and may be advantageous or disadvantageous to both parties.
Transfer of Liabilities: Any company in the legally complex and highly-regulated cannabis and hemp industries bears a certain number of liabilities. When a company is acquired in a stock deal or is merged with, in most cases, the resulting entity takes on those liabilities. The one exception being asset deals, where a buyer purchases all or select assets instead of the equity of the target. In asset deals, liabilities are not required to be transferred.
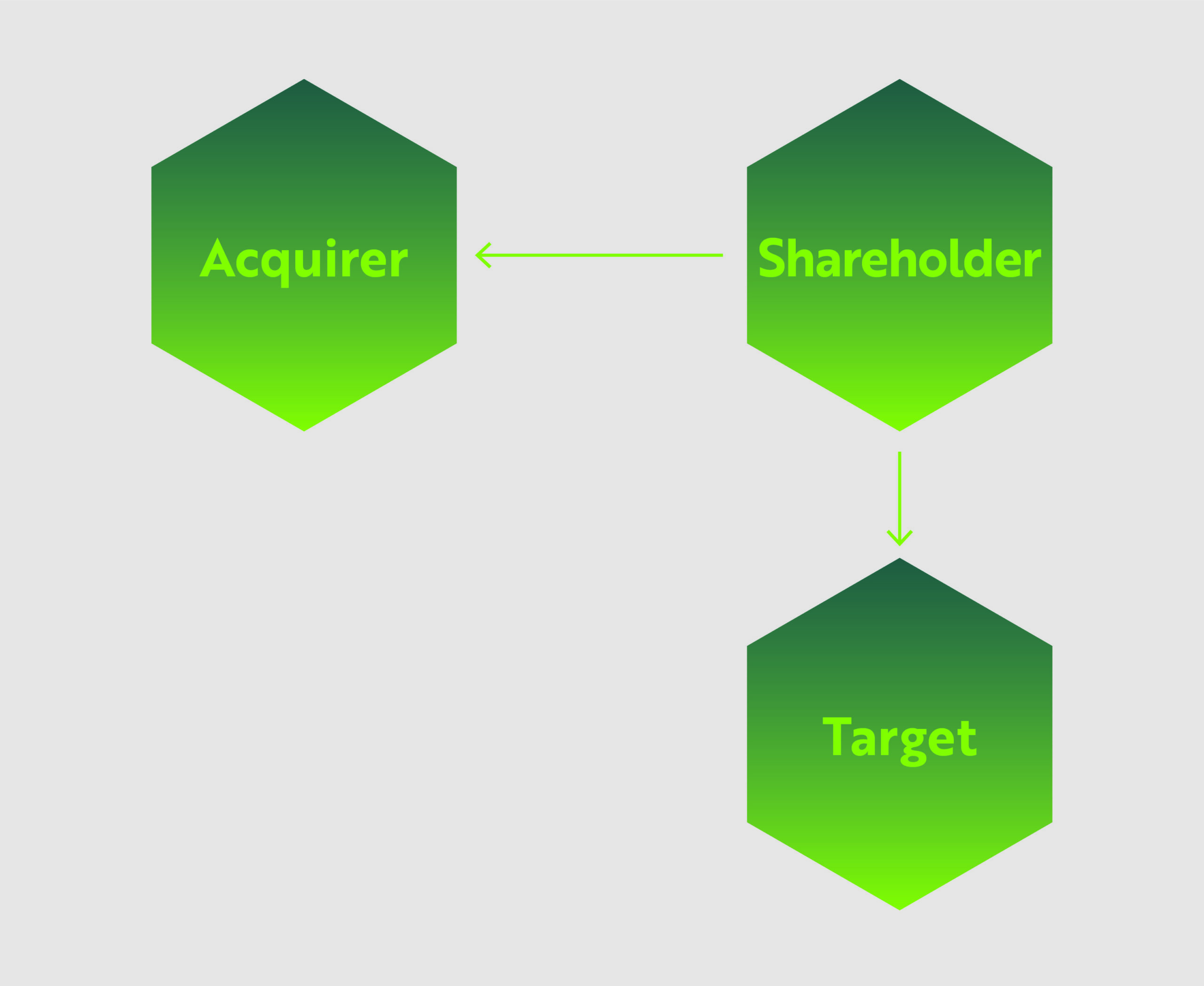
Shareholder/Third-Party Consent: A layer of complexity for all transaction structures is presented by the need to get consent from related parties. Some degree of shareholder consent is a requirement for mergers and stock/share purchase agreements, and depending on the Target company, getting consent may be smooth, or so difficult it derails negotiations.
Beyond that initial line of consent, deals are likely to require “third party” consent from the Target company’s existing contract holders – which can include suppliers, landlords, employee unions, etc. This is a particularly important consideration in deals where a “change of control” occurs. When the Target company is dissolved as part of the transaction process, the Acquirer is typically required to re-negotiate or enter into new contracts with third parties. Non-tangible assets, including intellectual property, trademarks and patents, and operating licenses, present a further layer of complexity where the Acquirer is often required to have the ownership of those assets formally transferred to the new entity.
Tax Impact: The structure of a deal will ultimately determine which aspects are taxed and which are tax-free. For example, asset acquisitions and stock/share purchases have tax consequences for both the Acquirer and Target companies. However, some merger types can be structured so that at least a part of the sale proceeds can be tax-deferred.
As this can have a significant impact on the ROI of any deal, a deep dive into tax implications (and liabilities) is a must. In the following, we will address the tax implications of each structure in broad strokes, but for more detail please see our article on M&A Tax Implications (COMING SOON).
Asset acquisitions
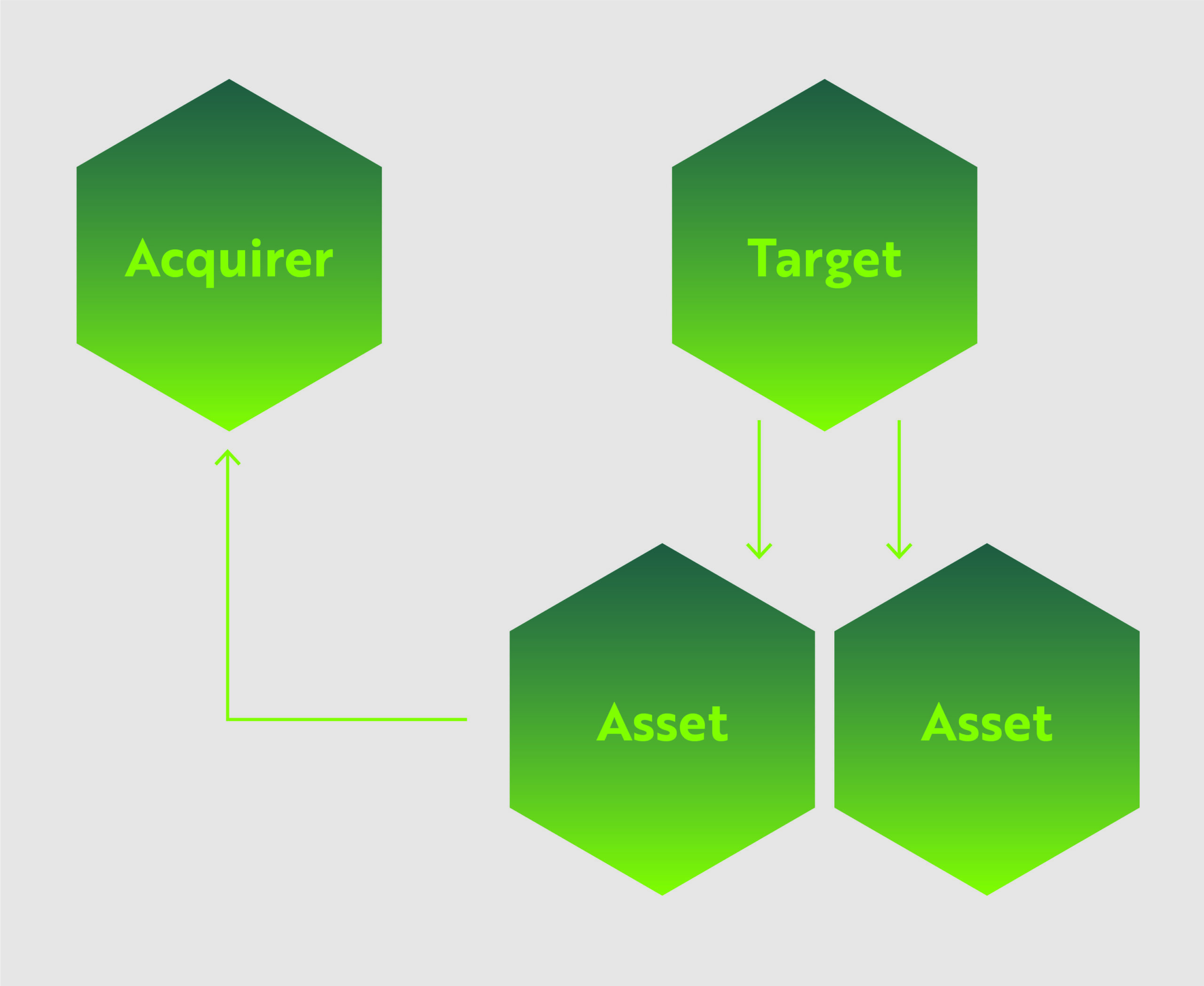
In this structure, the Acquirer identifies specific or all assets held by the Target company, which can include equipment, real estate, leases, inventory, equipment and patents, and pays an agreed-upon value, in cash and/or stock, for those assets. The Target company may continue operation after the deal.
This is one of the most common transaction structures, as the Acquirer can identify the specific assets that match their business plan and avoid burdensome or undesirable aspects of the Target company. From the Target company’s perspective, they can offload under-performing/non-core assets or streamline operations, and either continue operating, pivot, or unwind their company.
For the cannabis industry, asset sales are often preferred as many companies are still working out their operational specifics and the exchange of assets can be mutually beneficial.
Advantages/Disadvantages
Transfer of Liabilities: One of the strongest advantages of an asset deal structure is that the process of negotiating the assets for sale will include discussion of related liabilities. In many cases, the Acquirer can avoid taking on certain liabilities, depending on the types of assets discussed. This gives the Acquirer an added line of defense for protecting itself against inherited liabilities.
Shareholder/Third-Party Consent: Asset acquisitions are unique among the M&A transaction structures in that they do not necessarily require a stockholder majority agreement to conduct the deal.
However, because the entire Target company entity is not transferred in the deal, consent of third-parties can be a major roadblock. Unfortunately, as stated in our M&A Strategy article, many cannabis markets licenses are inextricably linked to the organization/ownership group that applied for and received the license. This means that acquiring an asset, for example a cultivation facility, does not necessarily mean the license to operate the facility can be included in the deal, and would likely require re-application or negotiation with regulatory authorities.
Tax Impact: A major consideration is the potential tax implications of an asset deal. Both the Acquirer and Target company will face immediate tax consequences following the deal. The Acquirer has a slight advantage in that a “step-up” in basis typically occurs, allowing the acquirer to depreciate the assets following the deal. Whereas the Target company is liable for the corporate tax of the sale and will also pay taxes on dividends from the sale.
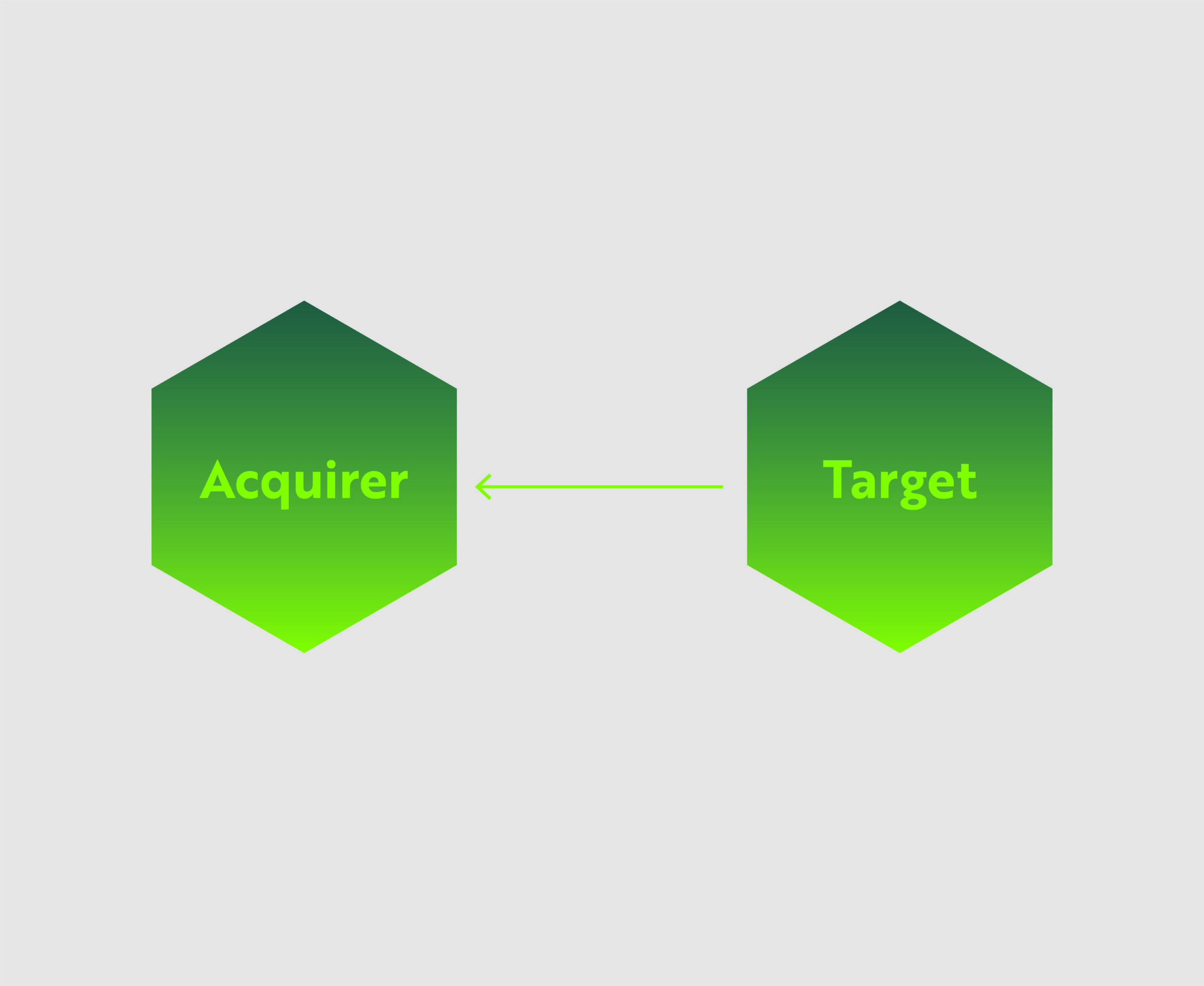
Stock/share purchase
In some ways, a stock/share purchase is a more efficient version of a merger. In this structure, the acquiring company simply purchases the ownership shares of the Target business. The companies do not necessarily merge and the Target company retains its name, structure, operations and business contracts. The Target business simply has a new ownership group.
Advantages/Disadvantages
Transfer of Liabilities: Since the entirety of the company comes under new ownership, all related liabilities are also transferred.
Shareholder/Third Party Consent: To complete a stock deal, the Acquirer needs shareholder approval, which is not problematic in many circumstances. But if the deal is for 100% of a company and/or the Target company has a plenitude of minority shareholders, getting shareholder approval can be difficult, and in some cases, make a deal impossible.
Because assets and contracts remain in the name of the Target company, third party consent is typically not required unless the relevant contracts contain specific prohibitions against assignment when there is a change of control.
Tax Impact: The primary concern for this deal is the unequal tax burdens for the Acquirer vs the Shareholders of the Target company. This structure is ideal for Target company shareholders because it avoids the double taxation that typically occurs with asset sales. Whereas Acquirers face several potentially unfavorable tax outcomes. Firstly, the Target company’s assets do not get adjusted to fair market value, and instead, continue with their historical tax basis. This denies the Acquirer any benefits from depreciation or amortization of the assets (although admittedly not as important in the cannabis industry due to 280E). Additionally, the Acquirer inherits any tax liabilities and uncertain tax positions from the Target company, raising the risk profile of the transaction.
Three types of mergers
1: Direct merger
In the most straight-forward option, the Acquiring company simply acquires the entirety of the target company, including all assets and liabilities. Target company shareholders are either bought out of their shares with cash, promissory notes, or given compensatory shares of the Acquiring company. The Target company is then considered dissolved upon completion of the deal.
2: Forward indirect merger
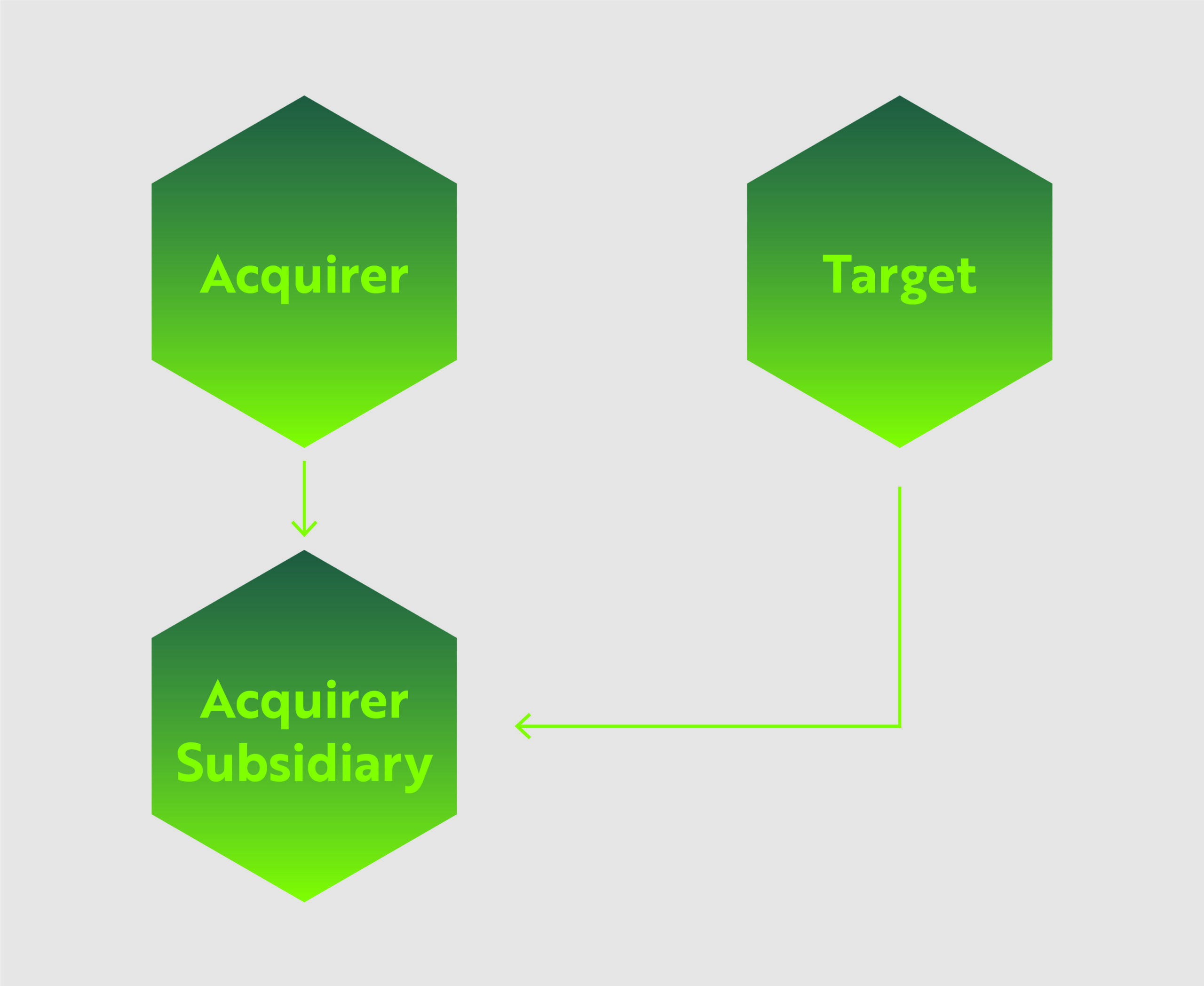
Also known as a forward triangular merger, the Acquiring company merges the Target company into a subsidiary of the Acquirer. The Target company is dissolved upon completion of the deal.
3: Reverse indirect merger
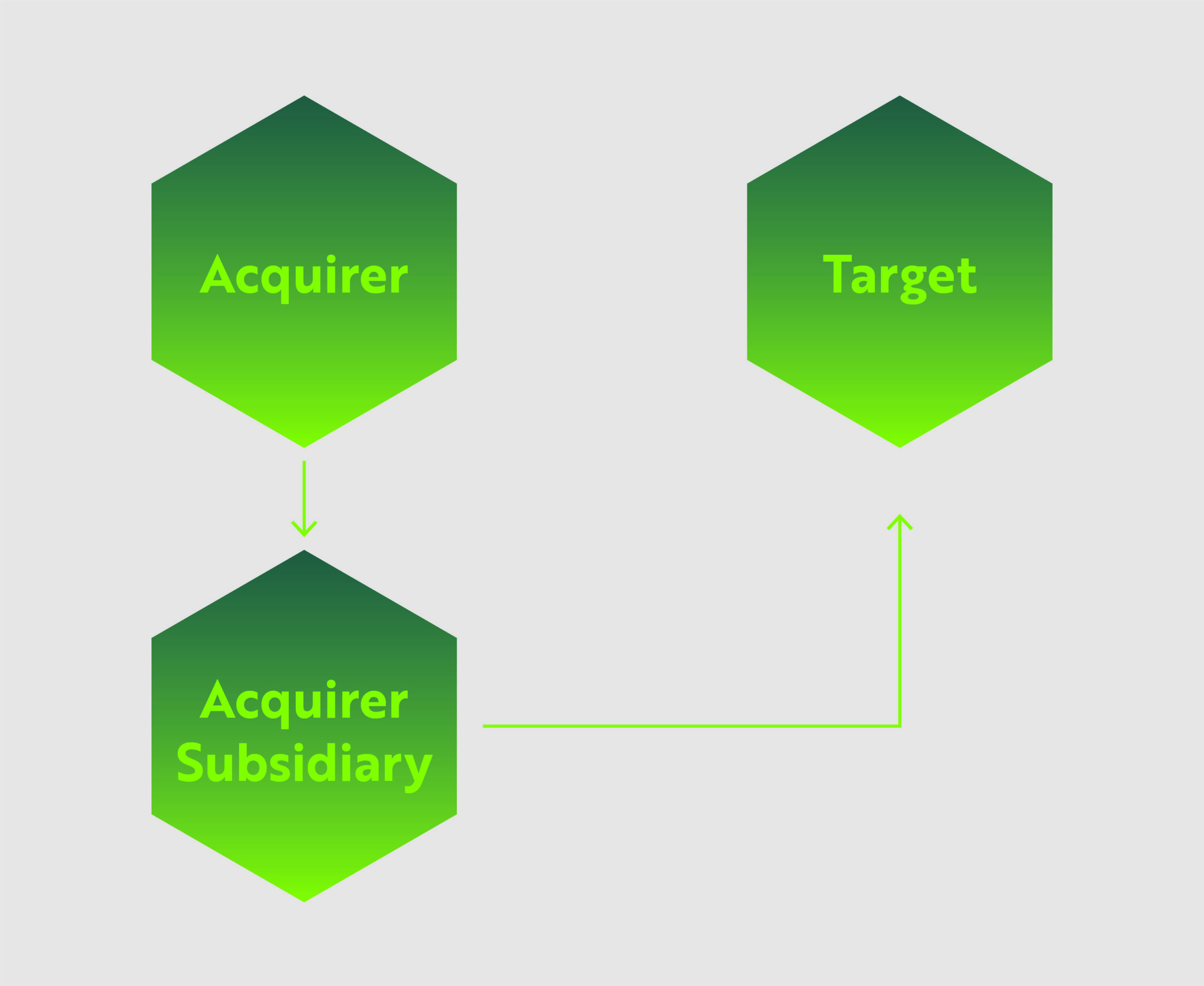
The third merger option is called the reverse triangular merger. In this deal the Acquirer uses a wholly-owned subsidiary to merge with the Target company. In this instance, the Target company is the surviving entity.
This is one of the most common merger types because not only is the Acquirer protected from certain liabilities due to the use of the subsidiary, but the Target company’s assets and contracts are preserved. In the cannabis industry, this is particularly advantageous because Acquirers can avoid a lot of red tape when entering a new market by simply taking up the licenses and business deals of the Target company.
Advantages/Disadvantages
Transfer of Liabilities: In option #1, the acquirer assumes all liabilities from the Target company. Options #2 and #3, provide some protection as the use of the subsidiary helps shield the Acquirer from certain liabilities.
Shareholder/Third Party Consent: Mergers can be performed without 100% shareholder approval. Typically, the Acquirer and Target company leadership will determine a mutually acceptable stockholder approval threshold.
Options #1 and #2, where the Target company is ultimately dissolved, will require re-negotiation of certain contracts and licenses. Whereas in option #3, as long as the Target company remains in operation, the contracts and licenses will likely remain intact, barring any “change of control” conditions.
Tax Impact: Ultimately, the tax implications of the merger options are complex and depend on whether cash or shares are used. Some mergers and reorganizations can be structured so that at least a part of the sale proceeds, in the form of acquirer’s stock, can receive tax-deferred treatment.
In conclusion
Each deal structure comes with its own tax advantages (or disadvantages), business continuity implications, and legal requirements. All of these factors must be considered and balanced during the negotiating process.
Catch up on previous articles in this series and see what’s coming next…
]]>Deadline extension for QOF investors
QOF investors with a deadline to invest their qualified capital gains in a qualified opportunity fund (“QOF”) between April 1, 2020 and December 31, 2020, now have until December 31, 2020 to invest those gains. This relief is applied automatically.
Relief for testing failures
A QOF must hold 90% of assets in a qualified opportunity zone property. This 90% standard is tested twice throughout the year, typically June 30th and December 31th. Those that fail the test are assessed a penalty if they cannot show “reasonable cause” for the failure.
The new IRS guidance removes penalties for QOFs that fail the 90% testing between April 1, 2020 and December 31, 2020. This failure will also be disregarded when the IRS determines whether a QOF meets the opportunity zone requirements for future tax years.
Relief for 30-month substantial improvement period
One of the key requirements that a qualified opportunity zone business property must meet is that substantial improvements, exceeding the original cost of the property, must be made within a 30-month period following the date of acquisition.
The new IRS guidance disregards the nine month period of April 1, 2020 to December 31, 2020 in determining the 30-month substantial improvement period.
Working Capital Safe Harbor Deadlines Extended
For an entity to qualify as be a Qualified Opportunity Zone Business (QOZB), no more than 5% of its assets can consist of Nonqualified Financial Property (NFP). One exception allows for a working capital safe harbor, where cash can be held in conjunction with a plan for expending that capital within a 31 month timeframe.
A QOZB in a Federally-declared disaster zone may extend this timeframe by up to 24 months. On March 31, 2020, President Trump issued an emergency declaration for all 50 states, the District of Columbia, and five territories. This effectively extended the working capital safe harbor timeline by 24 months.
QOF reinvestment period extended 12 months
When a QOF sells or disposes of QOZ property, if the QOF reinvests the proceeds into a QOZ property within a 12 month period following the sale, the proceeds are calculated as QOZ property for purposes of the 90% investment standard.
Under the IRS guidance, if January 20, 2020 falls within a QOF’s 12 month reinvestment period, that QOF is allowed up to an additional 12 months to reinvest in QOZ property.
Final thoughts
The deadline extensions and other forms of relief provided by IRS Notice 2020-39 provide much-needed relief for investors whose QOZ purchases and improvement plans were disrupted by the COVID-19 pandemic.
For guidance on how these rules will impact your investments, please contact us for a consultation.
]]>With the onset of the COVID-19 pandemic, traditional business practices for most organizations shifted nearly overnight. Whether that means companies have switched to remote-work strategies, increased their reliance on virtual applications, or even changed their product mix to stay relevant, the transition has been swift. While some of these shifts have demonstrated the adaptability and resilience of the business world, there are new and increased risks that must not be overlooked during this time, some of which include insurance and disaster relief fraud.
Additionally, we have seen major economic impacts since the virus’s spread. In the past weeks there have been record-breaking unemployment filings, including over 3 million initial claims for the week ended March 21, 2020 and over 6.6 million initial claims for the week ended March 28, 2020. Economists at the Federal Reserve district project total employment reductions of 47 million, or a 32.1 percent unemployment rate. US stock markets remain volatile and the Dow was down approximately 37% during the week of March 23, 2020. The economic losses are significant and will put extreme financial pressure on companies and individuals.
Given the above considerations, we’ve entered an era with the potential for a “perfect storm” of conditions and motivations that increase the risk of fraud, in its various forms, as a direct result of the global COVID-19 pandemic.
Types of fraud to be aware of
Fraud is generally defined as “wrongful or criminal deception intended to result in financial or personal gain.” Oftentimes we see this in the form of theft, which can be tangible goods and materials, or intangible assets, including private data or intellectual property.
A second form of fraud to consider is related to the intentional misrepresentation of company financial information. This often presents in the form of inaccurate profit and loss numbers, increased assets on a balance sheet, or under-reporting of major liabilities. This type of fraud is committed in order to attract investment, financing, or to avoid penalties for poor performance.
Why do we see the increased risk?
In almost every instance of identified fraud, there are three components involved which we generally refer to as the Fraud Triangle:
- Incentive and Pressure
- Rationalizing
- Opportunity
Given the major losses in the stock markets, unprecedented job losses, change in both consumer and B2B buying habits, and a general feeling of uncertainty, there are several emerging pressures and incentives to commit a fraudulent act.
When these pressures start to have to real impact on individuals and companies, that’s when the rationalizing begins. Individuals may think, “I need to this to survive and the company has so much money they will be fine.”
Company executives may think, “So many people’s jobs depend on this company’s survival, we have to do what we have to do to stay afloat.”
Lastly, as layoffs continue and remote work increases, the ability to follow internal controls will become more challenging and there will be less employee oversight. Employees may obtain increased authority as well. As such, the opportunities to commit fraudulent activities will increase.
Who are the potential perpetrators?
From a theft perspective, employees, vendors, and customers are the riskier population. Employees have access, knowledge, and are likely feeling the economic and personal impacts of the COVID-19 pandemic the most. Vendors can potentially be struggling during these times as well, which will increase their need to sell as much product and collect as much cash as possible. Lastly, customers, like the rest of the group, are feeling the pressure and when situations begin to look desperate, they will look to reduce their costs as much as possible.
What your organization can do about it
First, start with a common sense approach: pay attention and don’t forgo your standard risk mitigation procedures. Next, consider undertaking the following solutions:
1. Fraud Risk Assessment: Have you done a fraud risk assessment over your organization in the COVID-19 era? Have you done one recently at all? Whether this is done throughout the organization, or within a specific group of individuals or transactions, an updated fraud risk assessment can identify the risky areas in your business where you are most exposed to financial loss.
2. Respond to Identified Fraud: If you already suspect fraudulent activity is taking place, a forensic investigation can uncover much of these occurrences and help to resolve the issue by identifying the perpetrators and putting a stop to the activity.
3. Policies and Procedures Update: Have your policies and procedures been updated as a result of the changes to your business operations in the COVID-19 environment? Changes should be reflected in your controls as soon as possible. These need to be evaluated to ensure key controls are in place and functioning effectively in consideration of the changes to the way your business runs.
If you are unsure whether your controls are designed in a way that will prevent or detect fraud, we recommend consulting with professionals who can review your procedures and assist in implementing appropriate and efficient checks and oversight to reduce your risk of fraud.
4. Staff Re-Alignment: Current staffing models are changing. Whether you are short-staffed due to the outbreak, or concerned about cash flow related to fixed salaries, you might need some help. This is a time to consider innovative and affordable solutions that can be provided on an as-needed or periodic basis that relieves some of the fixed costs of hiring full-time employees, without losing any risk control or mitigation capabilities.
For example, you might want to consider outsourcing your internal audit function and hire consultants to perform these duties quarterly to avoid the annual internal audit salary expenses.
5. IT Risk Assessment: In these uncertain times, with nearly all business operations being handled online, there are additional risks to consider. A comprehensive risk assessment can be extremely valuable in avoiding financial or data losses. Additionally, there are some questions you should consider under the following categories:
a. Software – When was the last time you evaluated your systems, updated software, or performed an access and authorization review? Are you appropriately managing costs related to licenses for software?
b. Hardware – Are your hardware systems adequate to handle this level of remote work and online transacting? How strong are your physical safeguards to these assets?
c. People – Are your staff appropriately trained for this fully digital environment? Have policies and procedures for remote-work been implemented? Are individuals following these? Do you have the appropriate level of IT support staff to assist in the event of application failure and business interruption?
Final Thoughts
As described above, due to the economic impacts of the COVID-19 virus, it is anticipated that an increase in fraud will occur and it is important to note that this increased risk can have a significant impact on your operating cash flows if left ignored. It is important to update your fraud risk assessment, put a stop to any potential fraud, update your policies and procedures given the transition to virtual offices, evaluate your staffing needs, and consider increased IT risks.
The MGO Advisory Services Practice can help your organization with these activities, so please reach out with any questions.
]]>The coronavirus probably has not hit its peak yet, but every facet of daily life has already been affected. Many companies are actively reaching out to their customers to ensure operations will continue under the best of circumstances and as government regulations allow. For many companies this means supporting a widely spread remote worforce.
As we are already in the midst of this crisis, the chance for your firm to proactively prepare for disrupted operations has passed, but this does not mean there is nothing that can be done. Thanks to the plethora of cloud-based processing options, it is still possible to fully secure resources for the majority of your staff to work remotely. It may be more expensive right now, but that is still a better alternative than shuttering operations entirely. For companies that have already gone remote, you have probably deployed your remote desktop connections, trained your staff on remote conferencing options, and made sure your phone data plans are paid up for any type of mobile device solution you choose to use. Now that these features are fully deployed, this is a great time to review them for potential cybersecurity risk factors.
As is the case with on premise work, cybersecurity has no ‘one size fits all’ solution for remote environments. Each company is going to be different and will require its own strategy to mitigate risk. However, there are some basic steps companies can take to ensure that their cyber risk is limited as much as possible during this time of remote work.
Risks of relying on public internet
The single largest risk factor for remote work is the public internet that is being used by your staff to access your company data, but there are some simple steps you can take to mitigate risk from the largely unsecured public internet.
First and foremost is the securing and monitoring of all connections into your infrastructure. Think of all connections to your data, from any location, as a phone call. A device calls into the physical location of your data to access it, process it, and possibly transfer it to another location, much as you would see with a phone call or fax machine. The key is to identify the various points from which these devices can ‘call into’ your physical infrastructure and then limit the number of devices that can actually make this call. Identifying and securing the remote access points of your company data or network infrastructure is most likely the easier of the these two tasks as in most circumstances you should have near full control over the physical space in which your data storage device resides.
Establishing a secure infrastructure
From here, the simplest and most effective means of protection is to erect a firewall to keep out unauthorized calls. Step two is to do as much as you can to secure the connections that you want to allow through the firewall. The simplest means to accomplish this is through a Virtual Private Network (VPN) that will not only provide verification of the authorized connections past your firewall, but will also create a secure tunnel by which the call into your data can travel.
The VPN will compensate for most security provisions your staff’s at home internet might or might not have. From there, you will need to look carefully at which devices you actually will allow in through your firewall. It would be prudent to direct your technical team or IT Vendor to create a list of approved devices that is as small as possible. You should limit approved devices to company issued laptops and mobile handsets. You can expand this list to employee owned devices, but this should only be done with the advent of a Mobile Device Manager (MDM) solution. While a VPN will compensate for an insecure connection, an MDM will compensate for the lack of cybersecurity protection an employee owned device may or may not have. At this point, you might be asking, where can I find VPNs, MDMs, etc. Thankfully there are plenty of businesses on the open market that have these tools, and even technical staff, setup and ready to deploy and are just waiting for a company like yours to engage them for assistance. By employing these two relatively simple steps, your company can create remote work infrastructure that will significantly cut down on the risks of employees working from home over the open internet.
Vigilant infrastructure maintenance
Now that we have looked at what infrastructure should be put in place, we next need to look at how to properly maintain the infrastructure. As with the technical tools listed above, the market has plenty of Managed Service Providers (MSPs), such as MGO Technology Group, that are ready to engage and provide you with the technical staff and tools your company will need to effectively continue operations during this crisis. Make no mistake about it, your remote work environment is going to require some form of troubleshooting, either in the form of equipment malfunction or staff training on how to properly use the tools mentioned above. This is where having a good level one (L1) IT support staff comes into play in your cybersecurity strategy. In order to properly mitigate the risks of data breach or leakage, your staff will need to correctly use the tools you have put into place. Never underestimate how far a well-trained and well-equipped IT support staff can go in correcting the human errors not caught by your VPNs, Firewalls, and MDMs.
Access professional guidance
In order to weather this crisis or any over further disruption your company might experience, you are going to need good equipment and knowledgeable people to install and maintain this equipment. Finding, maintaining, and retaining the equipment and staff can be a difficult and time consuming endeavor. As mentioned above, you may want to consider engaging with technical MSPs who have the training and resources in order to install and maintain the infrastructure your company will need to not only allow your employees to work from home, but to also switch back to working on premise as soon as the situation improves.
For more guidance or to schedule a consultation, contact us here.
]]>Every organization needs a mobile device strategy for its employees. There is no way around it and there is no way to avoid it. Your organization must develop a clear policy for how your employees will use mobile devices to interact with your IT environment. Having no policy is no longer an option as it will open up your firm to exposure from so-called ‘Shadow IT’ as users will circumnavigate your IT infrastructure and e-mail documents over non-sanctioned channels so they can continue to work on their own mobile devices. Granted, a fully implemented mobile device policy may not eliminate these risks entirely, but it will go a long way toward reducing your organization’s overall risk exposure to a potential data breach. The first step of developing this policy is to answer a not so simple question; will your firm issue it’s own devices to employees or allow them to Bring Their Own Device (BYOD)?
Upsides and downsides of mobile device programs
There are two potential mobile devices programs; BYOD and Corporate Owned Devices (COD). Since every organization is unique, we do not intend to make a recommendation as to which strategy might be better. Our intent is to examine both polices and help you identify if one might be a better fit for your organization.
Before either of these programs is implemented, your organization will need Mobile Device Management (MDM) software. MDM is a crucial element to centrally manage and monitor any mobile devices that interact with your infrastructure. Your MDM must be in place before any device is allowed access to your network.
Examining a corporate-owned device policy
With COD your firm issues devices to your employees for corporate use and completely disallows the use of non-corporate device within your corporate infrastructure. Your firm takes responsibility for the devices’ setup, maintenance, and troubleshooting. While this policy does increase the setup time to make an employee fully ‘active’ within your IT setup, it allows for complete control of the hardware and associated software that is allowed within your firewall.
This setup has the advantage of having the lower overall security concerns of the two polices. You can chose every feature that is allowed on the device, right down to personal logons, and the actual applications allowed on the device. Since your organization owns the devices, they will already fall under any established guidelines the firm may have for governance of IT assets and thus minimize or eliminate the need for any extra work from your legal department to govern employee behavior.
While COD does allow for increased security and governance, it also has an overall higher price tag as your organization will be required to own every part of the mobile devices’ lifecycle — right down to maintaining a relationship with a cell phone provider to provide data services for the devices. As a result, the COD approach has the highest cost outlay between the two polices. COD will also have a higher cost to internal IT resources as they will be called upon to maintain the device inventory, train the users if needed, troubleshoot, reclaim the devices from departing employees, and repurpose them for the next user as you would with any other end user IT assets. This is time that your IT department could be dedicating to other activities so you will have to decide if you want to add this responsibility to their overall work load.
The benefits and downsides of “Bring Your Own Device” policies
BYOD, as the name states, allows your employees to add their own devices to your corporate infrastructure. This approach eliminates many of the costs listed above, such as the outlay needed to procure and maintain devices of your own along with the need to maintain data plans for the devices. However, given the variety of handsets available to users in today’s market your organization will have to spend more time setting up the actual policy to ensure your firm maintains a secure environment before actually rolling it out to your employees.
Beyond setting up the MDM, you will need to decide which devices, operating systems, and setups you will allow in your BYOD program. For example, you may be willing to allow iPhones and Samsung handsets into the program without additional security enhancements, but may require other Android based handsets to be encrypted before allowing them onto your BYOD program. You will have to designate a team to continuously evaluate new handsets as they reach the market to see what setup changes might be needed to allow these devices onto your program.
In addition to researching and choosing the allowed hardware policy, your firm will also have to establish the BYOD onboarding policy for each individual device operating system to be distributed to the users once they agree to join the BYOD policy. Your IT department will have to assist the users in onboarding the device and will have to continue to troubleshoot issues such as connectivity to corporate services such as e-mail. Finally, it will be necessary to establish a legal framework beyond your regular IT policy to define the parameters in which your company can monitor and administer the personal devices allowed onto your BYOD policy. Most companies accomplish this by working with their legal department to draw up an agreement to be signed by the user that establishes the rights of the company to monitor, administer, and if need be, completely wipe the device using the MDM.
The most prominent argument in favor of BYOD is that all the costs for resources listed above are up front. Once the MDM, policies, and procedures are in place you need only worry about updating them rather than activity implementing them as you would with a COD policy. All of the other associated costs with the device are still the responsibility of the employee. However, this is also the most prevalent argument against BYOD from a security standpoint. While the MDM and legal agreement will allow your IT department to monitor the device for any potential vulnerabilities, you will generally not be allowed to actively manage it. The onus will still be on the employee to ensure the device is properly updated and that no suspicious software is added to it. While your IT department would be able to inform the employee of suspicious software or activity within the device itself, the only true recourse you would have to protect your environment would be to remove the device from the MDM and thus from the BYOD program.
Making the right choice for your organization
Both programs have their advantages and drawbacks. Both allow for mobile access to various company resources such as e-mail and file sharing. However, there are differences to consider within each program regarding cost outlay, day to day maintenance, and overall security posture. Of course, neither of these polices are set in stone. Many companies are experimenting with a hybrid option that would allow employees to choose between a company device and joining a BYOD program in an attempt to fill the gaps present in both standalone programs. Each policy can be tailored to fit your company’s needs, but your IT department must make sure the proper back end work is done on both the MDM and the devices themselves to ensure that a proper IT security postured is maintained throughout your organization.
]]>Everything changes, except when it doesn’t
Time and time again we’ve seen reactions to various accounting scandals, after which new policies, procedures, and legislation are created and implemented. An example of this is the Sarbanes-Oxley Act (SOX) of 2002, which was a direct result of the accounting scandals at Enron, WorldCom, Global Crossing, Tyco, and Arthur Andersen.
SOX was established to provide additional auditing and financial regulations for publicly held companies to address the failures in corporate governance. Primarily it sets forth a requirement that the governing board, through the use of an audit committee, fulfill its corporate governance and oversight responsibilities for financial reporting by implementing a system that includes internal controls, risk management, and internal and external audit functions.
Governments experience challenges and oversight responsibility similar to those encountered by corporate America. Governance risks can be mitigated by applying the provisions of SOX to the public sector.
Some states and local governments have adopted similar requirements to SOX but, unfortunately, in many cases only after cataclysmic events have already taken place. In California, we only need to look back at the bankruptcy of Orange County and the securities fraud investigation surrounding the City of San Diego as examples of audit committees that were established in response to a breakdown in governance.
Taking your audit committee on the right mission
Governments typically establish audit committees for a number of reasons, which include addressing the risk of fraud, improving audit capabilities, strengthening internal controls, and using it as a tool that increases accountability and transparency. As a result, the mission of the audit committee often includes responsibility for:
- Oversight of the external audit.
- Oversight of the internal audit function.
- Oversight for internal controls and risk management.
Chart(er) your course
Most successful audit committees are created by a formal mandate by the governing board and, in some cases, a voter-approved charter. Mandates establish the mission of the committee and define the responsibilities and activities that the audit committee is expected to accomplish. A wide variety of items can be included in the mandate.
Creating the governing board’s resolution is the first step on the road to your audit committee’s success.

Follow the leader(ship)
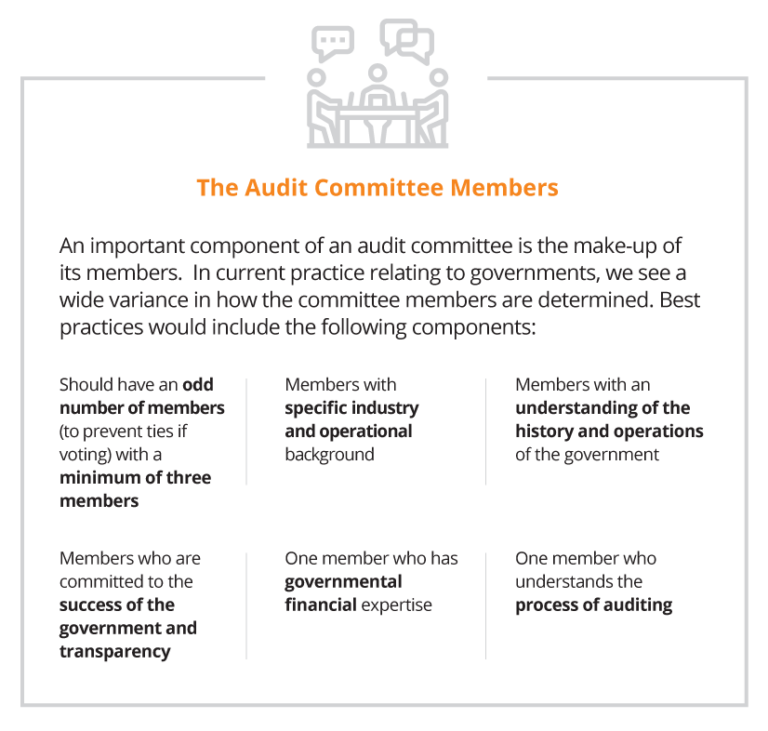
In practice we see a combination of these attributes, ranging from the full board acting as the audit committee, committees with one or more independent outsiders appointed by the board, and/or members from management and combinations of all of the above. While there are advantages and disadvantages for all of these approaches, each government needs to evaluate how to work within their own governance structure to best arrive at the most workable solution.
Strike the right balance between cost and risk
The overriding responsibility of the audit committee is to perform its oversight responsibilities related to the significant risks associated with the financial reporting and operational results of the government. This is followed closely by the need to work with management, internal auditors and the external auditors in identifying and implementing the appropriate internal controls that will reduce those risks to an acceptable level. While the cost of establishing and enforcing a level of zero risk tolerance is cost prohibitive, the audit committee should be looking for the proper balance of cost and a reduced level of risk.
Engage your audit committee with regular meetings
Depending on the complexity and activity levels of the government, the audit committee should meet at least three times a year. In larger governments, with robust systems and reporting, it’s a good practice to call for monthly meetings with the ability to add special purpose meetings as needed. These meetings should address the following:
External Auditors
- Confirmation of the annual financial statement and compliance audit, including scope and timing.
- Ad hoc reporting on issues where potential fraud or abuse have been identified.
- Receipt and review of the final financial statements and auditor’s reports
- Opinion on the financial statements and compliance audit;
- Internal controls over financial reporting and grants; and
- Violations of laws and regulations.
Internal Auditors
- Review of updated risk assessments over identified areas of risk.
- Review of annual audit plan, including status of the prior year’s efforts.
- Status reports of ongoing and completed audits.
- Reporting of the status of corrective action plans, including conditions noted, management’s response, steps taken to correct the conditions, expected time-line for full implementation of the corrective action and planned timing to verify the corrective action plan has been implemented.
Establish resources that are at the ready
Audit committees should be given the resources and authority to acquire additional expertise as and when required. These resources may include, but are not limited to, technical experts in accounting, auditing, operations, debt offerings, securities lending, cybersecurity, and legal services.
Taking extra steps now will save time later
While no system can guarantee breakdowns will not occur, a properly established audit committee will demonstrate for both elected officials and executive management that on behalf of their constituents they have taken the proper steps to reduce these risks to an acceptable tolerance level. History has shown over and over again that breakdowns in governance lead to fraud, waste and abuse. Don’t be deluded into thinking that it will never happen to your organization. Make sure it doesn’t happen on your watch.
]]>