- Internal controls, especially around fraud prevention, are essential for limiting losses, driving efficiency, improving accountability, and boosting company value during investments or M&A deals.
- The “tone at the top” from leadership in fostering an ethical environment, along with proper segregation of duties, are key elements for fraud prevention and strong internal controls.
- Well-established policies and procedures, like Delegation of Authority rules and restricted system access protocols, are also vital for maintaining adequate controls to enable company growth.
~
As the economy stands on shaky legs, private equity and venture capital firms are necessarily careful and strategic when assessing potential investment opportunities. Whether your long-term plan includes acquiring another company, selling your business, or seeking new capital, strengthening your internal control environment — with a focus on preventing fraud — is a powerful way to increase actual and perceived value.
In the following, we will lay out the reasons why fraud prevention is an essential element to proper corporate governance and illustrate key areas to examine whether your internal control environment is built to help your operation succeed.
The Importance of Internal Controls in Fraud Prevention
A robust internal control system is the first step toward managing, mitigating, and uncovering fraud. A strong internal control environment will:
Protect your company’s assets by reducing the risk of theft or misappropriation of cash, inventory, equipment, and intellectual property.
Detect fraudulent activities or irregularities early on and deter employees from attempting fraud in the first place.
Provide cost savings by limiting opportunities for financial losses, costly investigations, and legal expenses associated with fraud.
Drive operational efficiency by providing clear processes and guidelines that reduce the risk of errors or inefficiencies in day-to-day operations.
Improve employee accountability by implementing checks and balances that discourage unethical behavior.
When seeking an investment or undertaking a significant M&A deal, you should have a firm grasp of the strength and quality of your internal control environment. Not only will you reduce the risk of fraud in the near term, but you will also cultivate confidence with potential investors and M&A partners.
Fraud Prevention Starts with the “Tone at the Top”
The first key element to look for in measuring the strength of your internal controls is ensuring a clear and proactive “tone at the top”, meaning an ethical environment fostered by the board of directors, audit committee, and senior management. A good tone at the top encourages positive behavior and helps prevent fraud and other unethical practices.
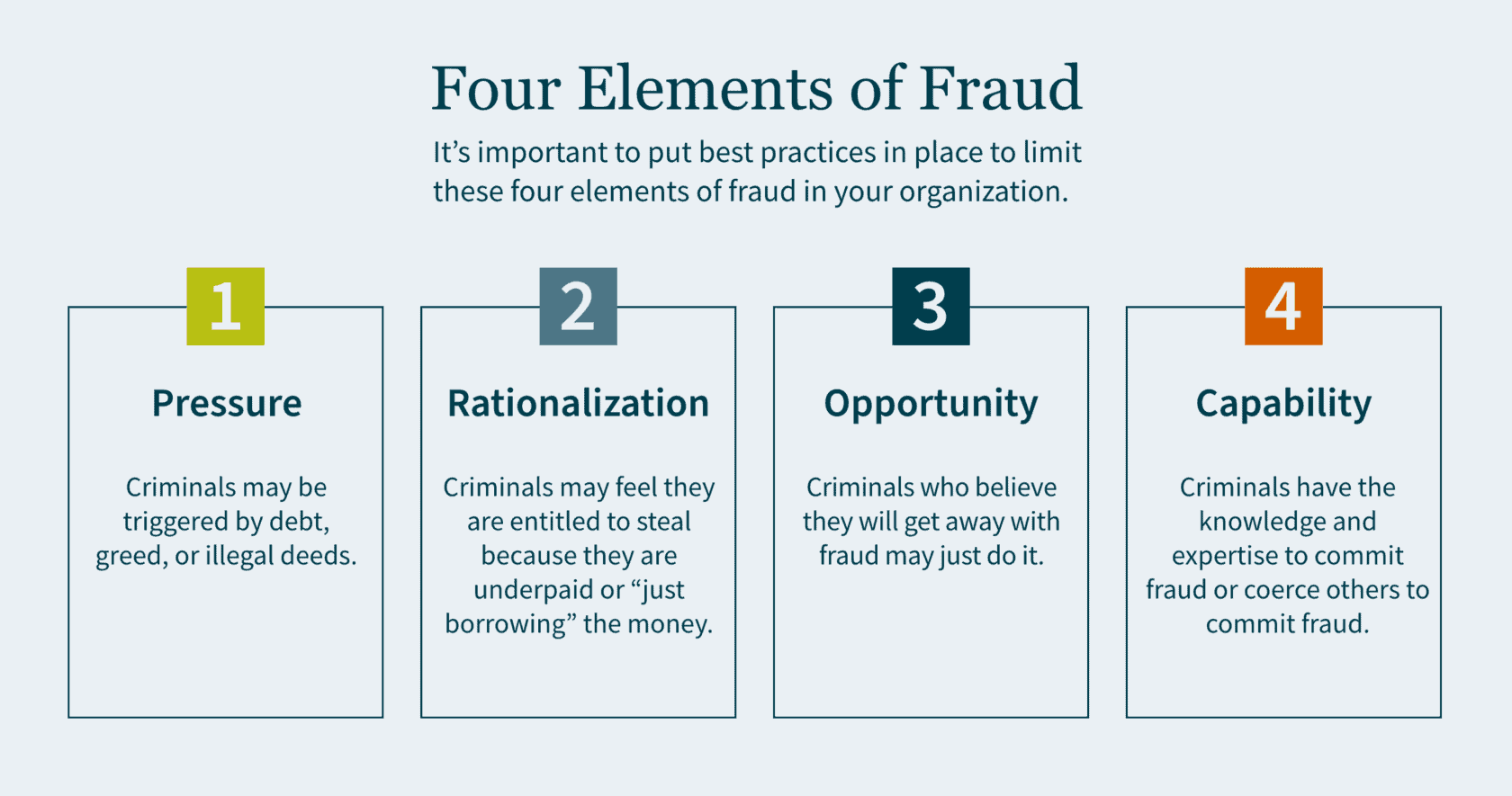
There are four elements to fraud: pressure, rationalization, opportunity and capability.
Pressure motivates crime. This could be triggered by debt, greed, or illegal deeds. Individuals who have financial problems and commit financial crimes tend to rationalize their actions. Criminals may feel that they are entitled to the money they are stealing, because they believe they are underpaid. In some cases, they simply rationalize to themselves that they are only “borrowing” the money and have every intention of paying it back.
Criminals who can commit fraud and believe they will get away with it may just do it. Capability means the criminal has the expertise as well as the intelligence to coerce others into committing fraud. The board of directors is responsible for selecting and monitoring executive management to ensure best practices are in place to limit the motivations of all four elements of fraud.
Proper Segregation of Duties for Internal Controls
The second key element to look for in your internal controls is a well-established segregation of duties. The idea is to establish controls so that no single person has the ability that would allow them the opportunity to commit fraud. Companies must make it extremely difficult for any single employee to have the opportunity to perpetrate a crime and subsequently cover it up.
Fraud Controls
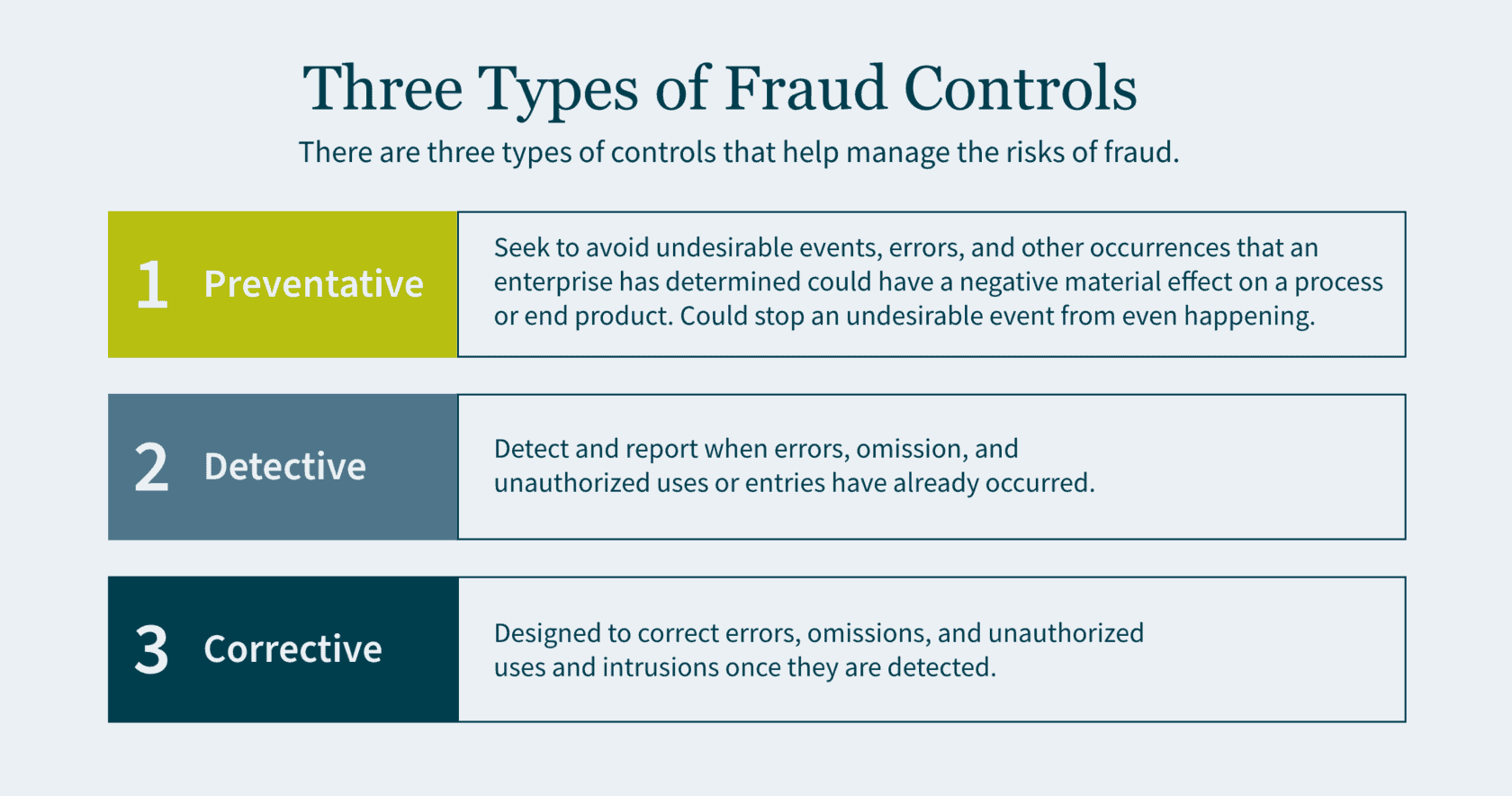
There are three types of controls that help manage the risks of fraud: preventative, detective, and corrective.
- Preventative controls seek to avoid undesirable events, errors, and other occurrences that an enterprise has determined could have a negative material effect on a process or end product. Preventative controls are the best of the three as they are the first line of defense and a backstop to fraud. If designed correctly, preventative controls stop an undesirable event from even happening.
- Detective controls exist to detect and report when errors, omission, and unauthorized uses or entries have already occurred. Although it is important to identify these adverse events, you are doing so after the fraud has already been committed.
- Corrective (also referred to as compensating) controls are designed to correct errors, omissions, and unauthorized uses and intrusions once they are detected.
Preventing Misappropriation of Assets
An important component of segregation of duties is to prevent the misappropriation of assets and reduce fraud risk. Below are some examples of best practices for various types of assets:
- Cash Receipt: segregate the receipt of cash/checks and the recording of the journal entry in the accounting system into two roles.
- Accounts Receivable: segregate the responsibilities of recording cash received from customers and providing credit memos to customers. (If one person performs both functions, it creates the opportunity to divert payments from the customer to the employee and then cover the theft with a matching credit to the customer’s account).
- Cash Reconciliation: the individuals who authorize, process, or record cash should not perform the bank reconciliation to the general ledger.
- Inventory: individuals who order goods from the suppliers should not have the ability to log the goods received in the accounting system.
- Payroll: segregate the responsibilities of compiling gross and net pay for payroll, with the responsibilities of verifying the calculation. (If a single individual performs both functions, it allows for the opportunity to increase personal compensation and the compensation of others without authorization. It also provides an opportunity to create a fictitious payee and make corresponding payroll checks).
The Importance of Policies and Procedures
The third key element to look for in your investees is well-established policies and procedures. Make sure that any company you consider acquiring has basic policies and procedures in place, such as Delegation of Authority (DOA).
The DOA is a policy where the executive team delegates authority to the management of the company. Individuals should be considered appropriate to fulfill delegated roles and responsibilities. The DOA should be reviewed at least annually. Subsequently, it is important to ensure that the DOA is being followed, and that approvals do not deviate from it. Any such anomalies should be rare and, when they do occur, they need to be reviewed and approved. Constant deviations from the DOA may be a sign that the DOA needs to be restructured.
A second essential policy and procedure is restricted computer and application access. This is to protect sensitive company financials and proprietary data. The company should have a robust control environment and maintain computer logins and password access on a need-to-know basis. Access should only be granted by the owner of the application or system and subsequently logged by the administrator. Now more than ever companies are hiring remote employees. This shift in the dynamic workspace further emphasizes the need for a quality IT controls environment.
How We Can Help
As you prepare your company for future growth, getting an impartial third-party opinion on your internal control environment can be a powerful tool for finding gaps and inefficiencies, and implementing value-added changes.
Our dedicated Public Company teams offer a deep level of industry experience and technical skills. We can help prepare your company for a major capital raise, including going public via an IPO or RTO. Or we can help optimize value for an M&A deal, whether you are buying or selling. Contact us today to access an external, holistic vision focused on helping you grow and succeed
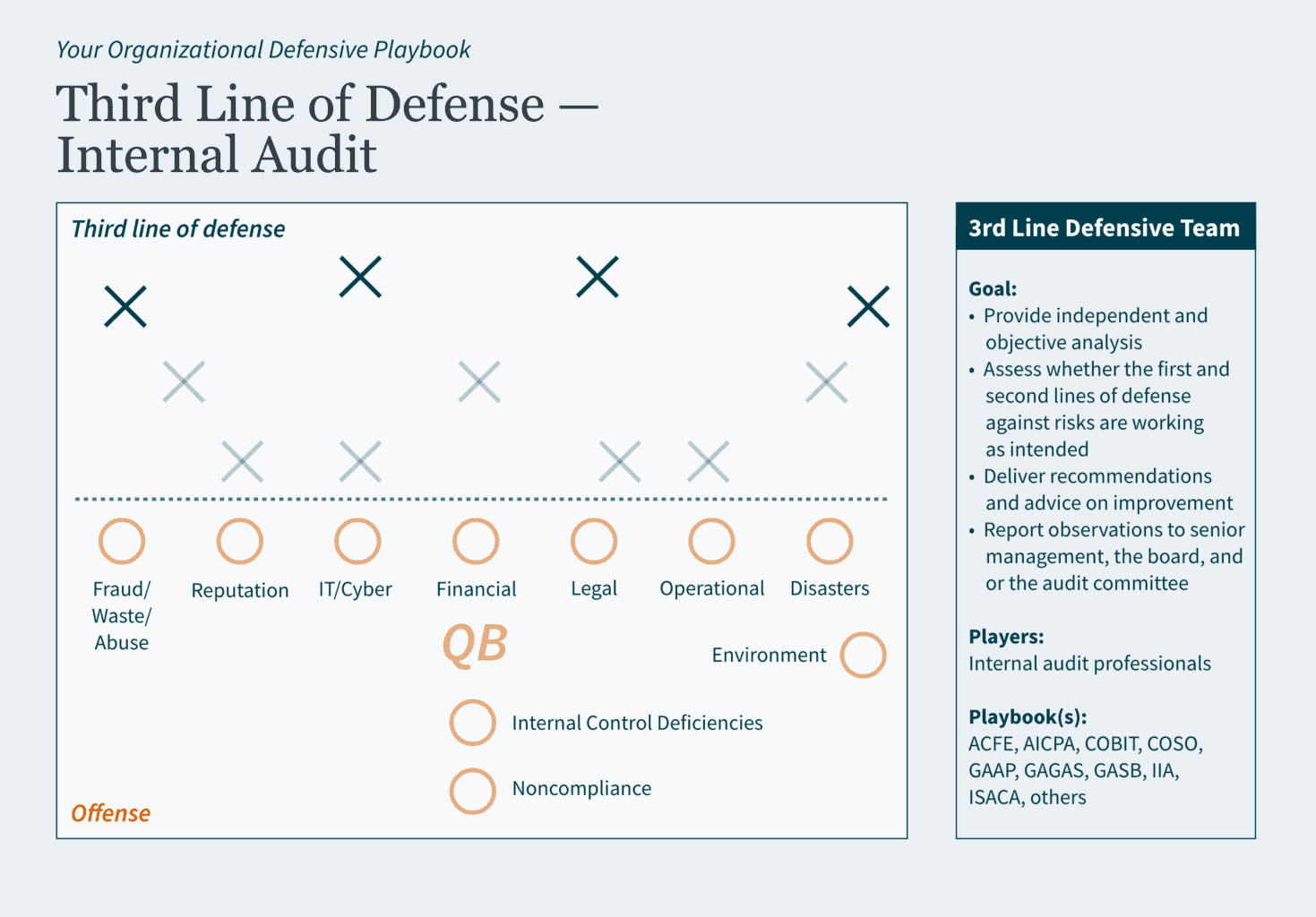
]]>- State and local governments need defensive strategies to protect against risks like fraud, financial loss, and reputational damage, and checks to ensure those strategies are working.
- The Three Lines Model executes three levels of protection designed to prevent risks from disrupting your operations and causing damage or loss.
- As the third-line defense, internal auditing analyzes the entire field to identify potential weaknesses and ensure your defensive strategies are effective at averting risks.
~
At the start of the football season, sports analysts spend a lot of time talking about who will be the player to lead their team to a championship. Yet, as we learn year after year, championships are not won by a single player. It is a collective effort, based on an assembly of individuals pooling their talents together in pursuit of a common goal.
In sports, the common goal is a championship. In business, the goal is to generate profit by establishing customer loyalty for your products or services. In government, the goal is to make our communities ideal places to live, work, and play. To win in all these instances, you need a strong team with contributions from every player.
Football fans often hear the refrain, “offense wins games, but defense wins championships.” Government teams looking to achieve their goals should not overlook the necessity of a robust defense — with internal auditing giving you the upper hand over your opponent.
What is Internal Auditing?
According to The Institute of Internal Auditors (IIA), internal auditing is an independent, objective assurance and consulting activity designed to add value and improve an organization’s operations. Internal auditing provides a systematic approach to evaluating and improving the effectiveness of governance, risk management, and controls processes.
To simplify: Your organization has goals (objectives). However, obstacles (risks) may exist that keep your organization from reaching its goals. You should develop strategies (internal controls) to prevent those obstacles from occurring, and continuously check to make sure your strategies are working properly (monitoring). To avoid confirmation bias — where you only seek and accept information that supports your goals — you should seek validation from an objective entity (internal audit) to evaluate if your strategies truly position your organization to succeed.
To accomplish all this, you need a coalition of talented individuals that can identify risks, strategize against them, prevent or detect risk infiltration, and consistently monitor emerging risks to provide guidance on how to stay ahead of the curve. In football terms, you need a strong defensive line!
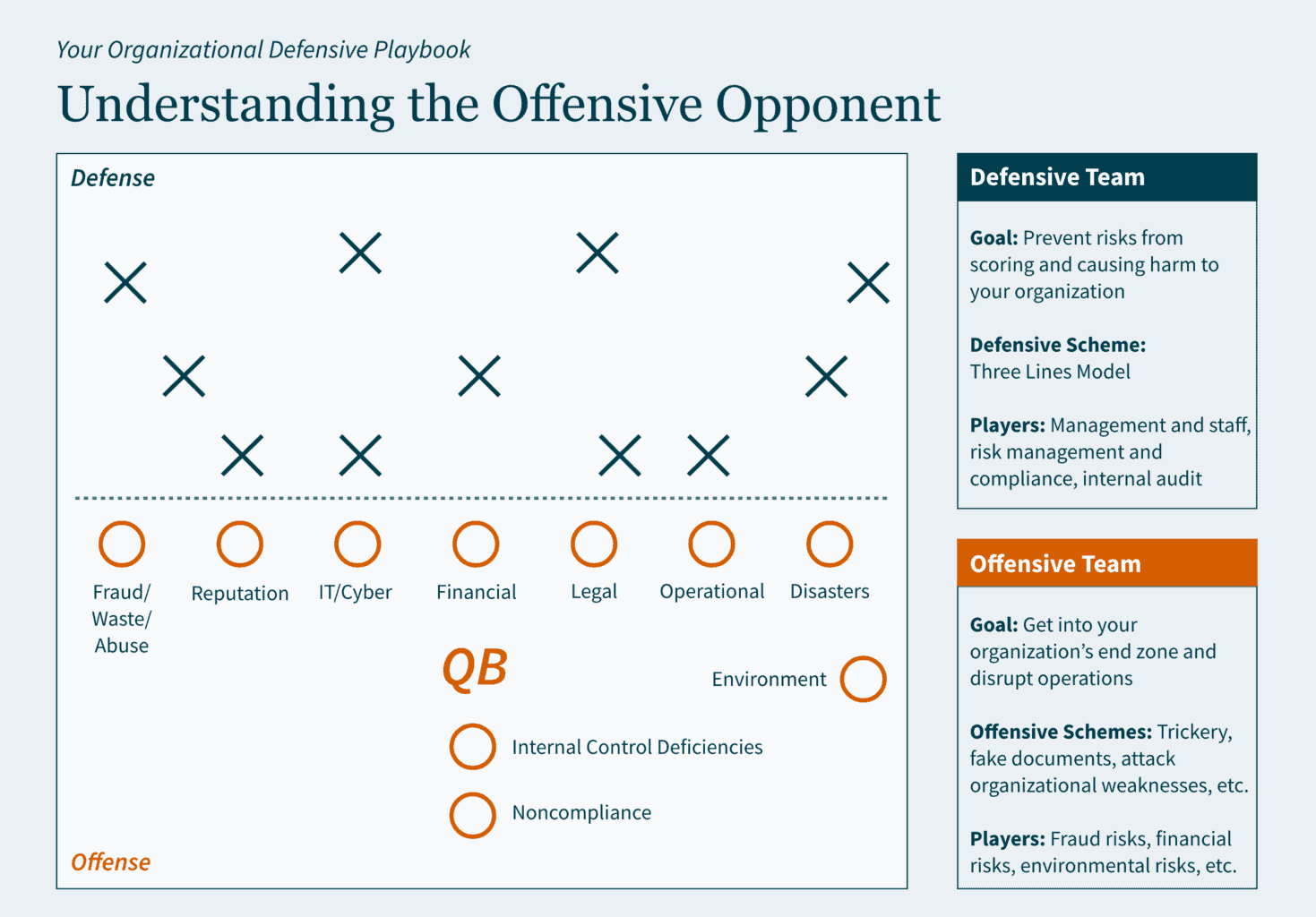
Three Lines of Defense
Let’s say that risk is the offensive team. Its goal is to get into your organization’s end zone to disrupt operations. The quarterback could be a hacker, fraudster, or unintentional human error. The offensive team also has other formidable players: fraud risks, cyber-attack risks, liquidity risks, etc.
Organizations need a more skilled, agile, and experienced defensive team to counteract the activity of the risk offense. Enter IIA’s Three Lines Model. This defensive strategy executes three levels of protection designed to keep risk from causing extreme financial or other damage.
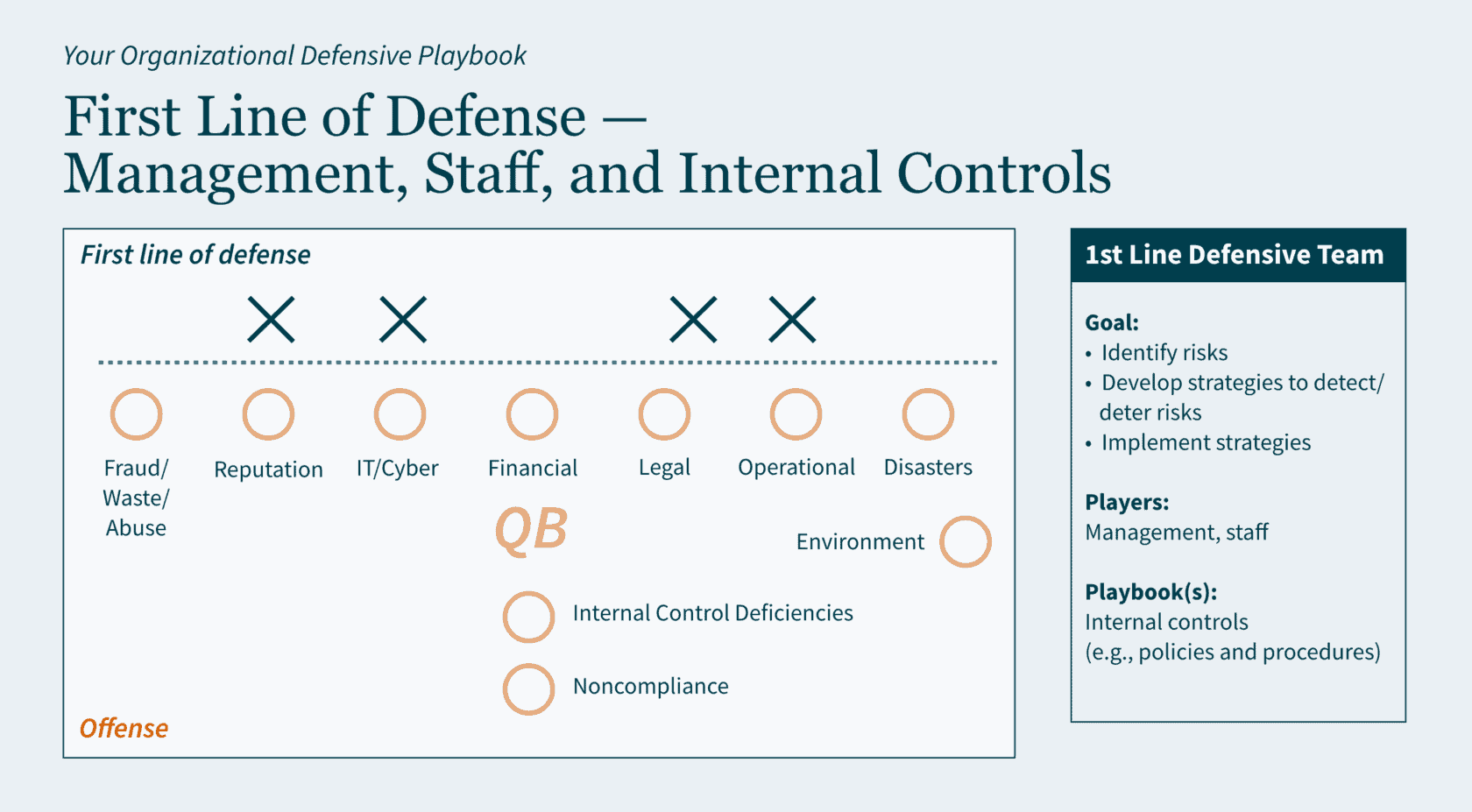
The Three Lines Model defines defensive roles and responsibilities as follows:
- First Line of Defense – develops strategies to address risks
- Second Line of Defense – monitors strategies
- Third Line of Defense – provides assurance that strategies are truly effective at mitigating risks
Let’s look at the organizational playbook to understand the goals of the offensive and defensive teams and the Three Lines defensive strategy.
Understanding the Offensive Opponent
Organizations are trying to prevent risks from disrupting operations and causing financial and/or other damages. If the risk team scores in your end zone, that means they have exposed a weakness in your organization. Depending on the weakness, it could cost you a little (inefficient operations) or it could cost you a lot (major cyberbreach with financial and reputational damages) … but it will cost you!
Defining Each Line of Defense
First Line of Defense: Management, Staff, and Internal Controls
The first line of defense consists of the organizational staff associated with daily operations, delivery of goods and services, and identifying and addressing risks. For example, to minimize the risk of hacking via password breaches, this line would create a password policy and accompanying procedure, set up systems requirements accordingly, and follow the policy and procedures in daily operations.
Second Line of Defense: Risk Management and Compliance Functions
The second line of defense consists of the organizational staff that monitor your organization’s adherence to its own policies and procedures and other required guidance (e.g., regulations, laws, etc.). For example, to ensure that your organization is following its policies and procedures for minimizing hacking via password breaches, this line would periodically analyze data to ensure compliance with internal guidance, industry best practices, etc.

Third Line of Defense: Internal Audit
The third line of defense consists of internal audit professionals with knowledge in various industries. Internal audit conducts real-time assessments and communicates any weaknesses in the first two lines. Using the prevention of hacking example from above, in addition to assessing password protocols and practice, internal audit may identify that your organization has improper access controls that increase the risk of hackers infiltrating your organization’s systems. Internal audit would provide recommendations for improvement and express urgency for corrective action.
Defensive Benefits of Internal Auditing
Internal audit is not an adversary, it is part of your team. Internal audit collaborates with your management and staff, in real time, to understand your organizational goals, concerns, strengths, and weaknesses. Where external audit provides your management with an analysis of a snapshot in time, internal audit continuously and systematically provides value-added feedback to your management and your board and/or audit committee.
Internal audit assists with ensuring your organizational playbook(s) remain relevant. As the third or last line of defense, it analyzes the entire field (the organization) to make sure your defensive strategies (internal controls) are effective at averting risks from scoring (causing financial, operational, reputational, etc., losses).
Part of the analyses conducted by internal audit include (but are not limited to):
- Conducting risk assessments to identify the likelihood and potential impact of risks to assist the organization in focusing resources on prioritized areas for improvement.
- Assessing your information technology and cybersecurity environments to identify and advise on protecting organizational data, improving IT infrastructure, preparing disaster recovery strategies, etc.
- Assisting in preparing for external audits by assessing if the organization’s financial statements are accurate, complete, compliant with regulations, and free from material misstatement.
- Conducting performance assessments to identify areas for efficiency and effectiveness improvements.
Internal audit strengthens your organization’s improvement efforts by bringing reinforcements to your already stellar team. The internal audit group delivers additional resource capacity, skills, and perspectives — including extensive knowledge about various industry standards as internal audit professionals are required to maintain continuing education in their specific areas of focus.
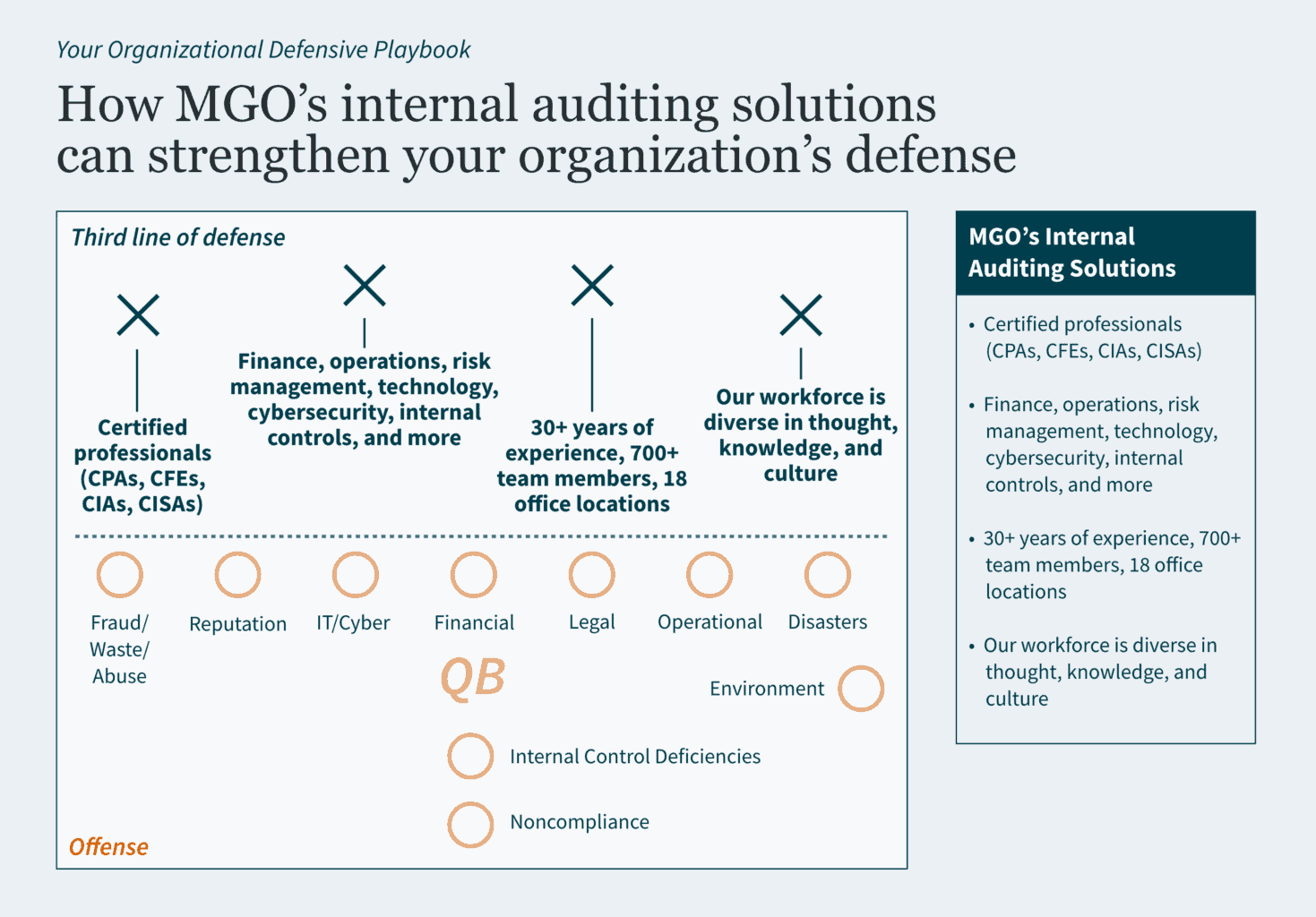
How MGO Can Strengthen Your Team’s Defense
MGO has a defensive line that is ready and motivated to support your organization. Stacked with professionals experienced in areas like state and local government, fraud, audit and assurance, government audit, and cybersecurity, our team is diverse in thought, knowledge, and culture — and we bring those perspectives to the field for you. Contact us today to learn how our internal auditing solutions can boost your organization’s defense.
Executive Summary:
- The Sarbanes-Oxley (SOX) Act established stricter financial reporting requirements for public companies, leading to increased scrutiny of Information Produced by the Entity (IPE).
- IPE carries different levels of risk depending on whether it is system-generated and manually prepared IPE. Strong documentation is key to validating completeness and accuracy of IPE.
- Best practices for IPE documentation include identifying the source, parameters, and format of reports; validating totals and counts; retaining screenshots; and having knowledgeable reviewers.
~
Passed by Congress in 2002, the Sarbanes-Oxley (SOX) Act revolutionized public company audits by introducing financial reporting requirements aimed at increasing transparency and preventing fraud. Most notably, the SOX Act established the Public Company Accounting Oversight Board (PCAOB), a nonprofit organization that oversees the audits of public companies to protect investors and further the public interest in the preparation of informative, accurate, and independent audit reports.
The PCAOB refines its auditing standards annually and, in recent years, the organization has placed greater scrutiny on the work of external auditors. To keep up with PCAOB compliance, external auditors have imposed more rigorous documentation requirements on companies. As a result, companies have felt pressure to provide more expansive Information Produced by the Entity (IPE).
If external auditors have applied greater scrutiny on your reporting, you may be wondering: What level of documentation is sufficient? How can you improve your documentation to avoid deficiencies and provide greater clarity? In this article, we will discuss: 1) what IPE is, 2) the risks associated with different IPE, and 3) how to document your IPE thoroughly.
What is IPE?
IPE is any information created by a company used as part of audit evidence. Audit evidence may be used to support an underlying internal control or as part of a substantive audit. Although there are documentation and risk severity differences between system-generated and manually prepared IPE, the fundamental questions that need to be addressed are the same:
- Is the data complete?
- Is the data accurate?
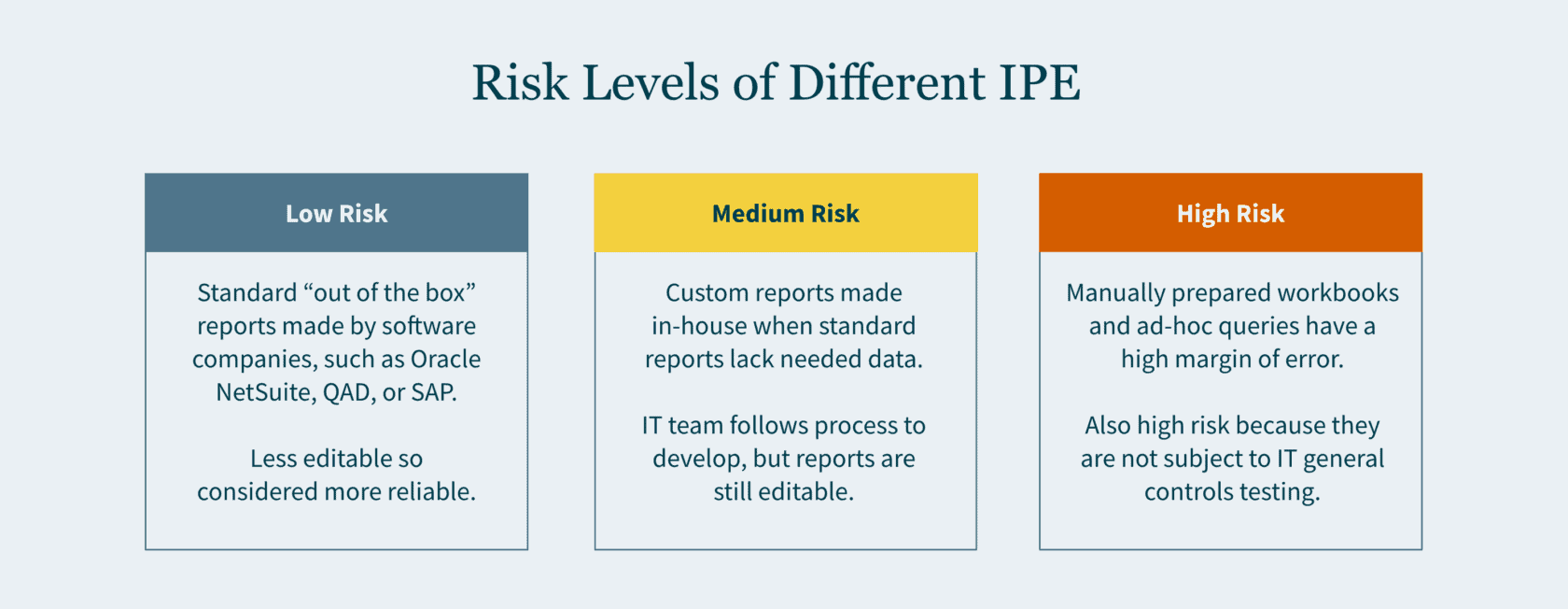
Risk Levels of Different IPE
Here is an overview of how risk levels vary for different types of information you report to auditors:
Low Risk
“Out of the box” reports carry the lowest risk. These reports are also referred to as “standard” or “canned” reports. Standard reports have been developed by software companies — such as Oracle NetSuite, QAD, or SAP — as part of their enterprise resource planning (ERP) systems. Typically, the end user (you) and even your IT team cannot modify these reports. Given the constrained editability, greater reliance is placed on these reports.
Medium Risk
Custom reports are typically driven by the business team and developed in-house by your company’s IT team. When your company’s ERP system does not have a report that would provide sufficient data, the in-house developers create a custom report. The IT team follows their change management process when developing the request report. If the report results do not align with your business team’s expectations, the query is refined, and the process is repeated until it does.
High Risk
A manually prepared workbook or an ad-hoc query are inherently the riskiest documentation. A manually prepared workbook may be a debt reconciliation prepared by your staff accountant, or a list of litigations the company is involved in drafted by your legal department. Given that these are manually drafted, the margin of error may be high.
An ad-hoc query is considered high risk since the report is not subject to IT General Controls (ITGC) testing. The end user may input any parameters to generate the report. Since no control testing is performed by your company, external auditors would need to rely on their own IT team to vet the nonstandard query.
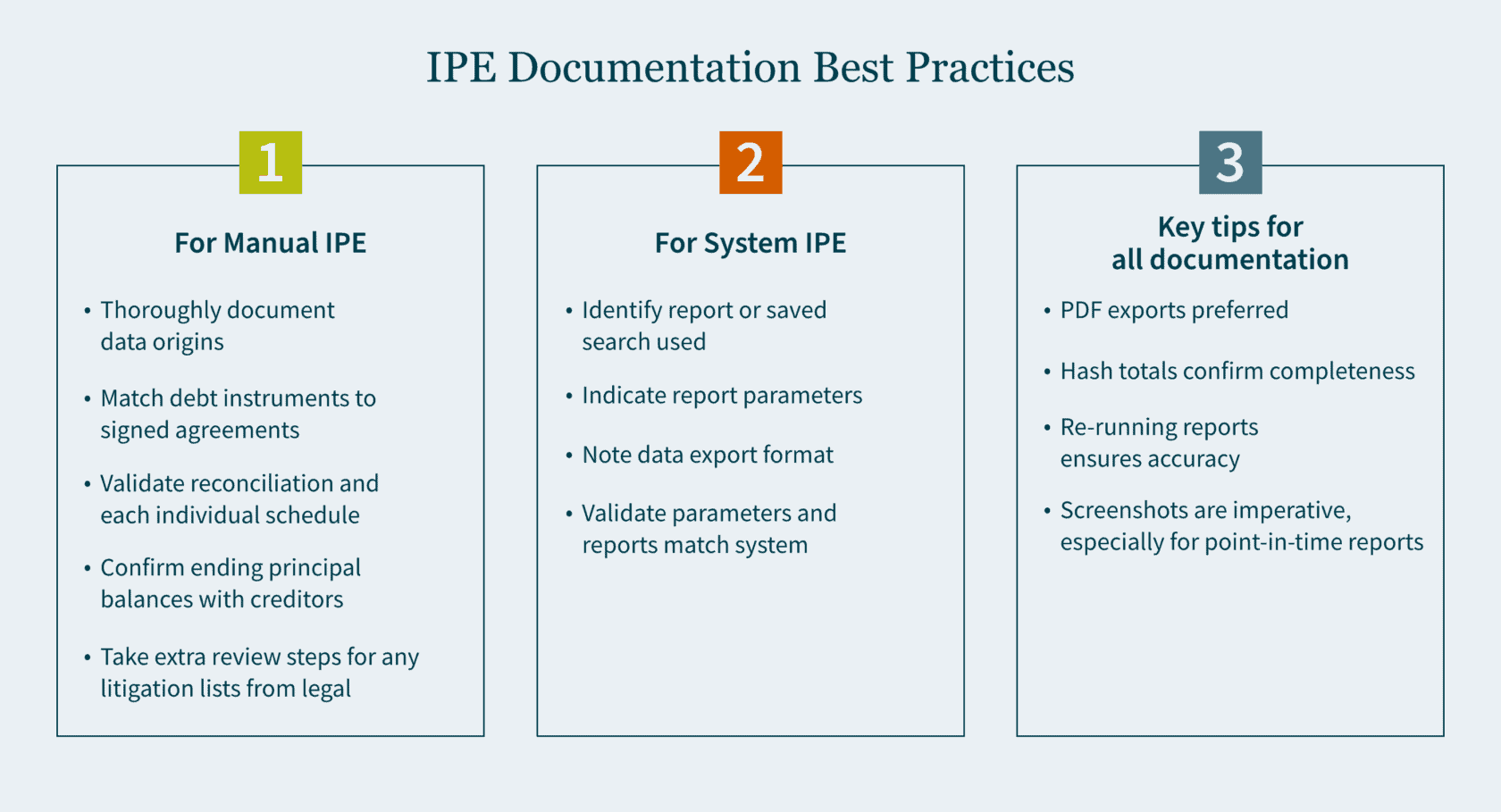
How to Document IPE?
Your documentation will vary to a certain degree depending on whether the IPE is manually prepared or system generated. In either case, it is important to be as thorough as possible when documenting your procedures.
Manual IPE
For a manually prepared workbook, provide thorough documentation about the origins of the data. It is ideal to have someone who is privy to the information review the workbook.
When the reconciliation is comprised of debt instruments, the reviewer should do the following:
- Match the list of individual debt instruments to the signed agreements.
- Validate the reconciliation and each individual schedule for mathematical accuracy.
- Confirm ending principal balances with creditors (where possible).
If the list consists of litigations compiled by the legal department, the reviewer should do the following:
- Send confirmations to outside counsel (where possible).
- Obtain a list of commitments and contingency journal entries made to an accrual.
These additional steps provide greater comfort that the list compiled is complete and accurate.
System-Generated IPE
For system-generated IPE, there are a handful of questions to keep in mind:
- Have you identified the report or saved search that was used?
- What parameters were used to generate this report?
- In what format is the data exported?
- After you run your report and confirm the parameters are correct, what format should be utilized for your export?
Exported Data
Most ERP systems allow the exporting of data in the following four formats:
- PDF (portable document format)
- Excel
- CSV (comma-separated values)
- Text file
One major drawback in an Excel, CSV, and text file is that, by their nature, they are editable upon export. An additional drawback of a text file is that it does not contain formatting. As the volume of data grows, proving out the completeness and accuracy becomes more challenging. For these reasons, a PDF export is typically preferred.
After the data is exported in one of the four formats, you want to ensure that it agrees back to the system (completeness and accuracy). Here are a few ways to do that:
- Does the exported data have dollar amount totals? If so, agree the total dollar amount to the system.
- Does the exported data have hash totals? An example of a hash total is employee ID numbers which in aggregate have no real value other than providing confirmation that the data is complete and accurate.
- Does the report have a total line count? If totals are not available, line counts may be used. However, it is important to note that while the line count may agree, the data itself could have still been inadvertently manipulated.
Screenshots of Data
Retaining screenshots is imperative for documentation. A detailed screenshot should include some (if not all) of the following:
- Totals (dollar amounts, hash amounts, etc.)
- Lines count
- Parameters utilized
- Time and date stamp
The first three items validate the completeness and accuracy of the exported data. The fourth item confirms when the report was run and if it was timely. There are many reports that are point-in-time and may not be recreated at a future date. Knowing the constraints of the reports you use is important. Retaining screenshots cannot be overemphasized, especially for point-in-time reports.
Certain ERP systems or online portals do not provide a preview of the report prior to the export. This puts a constraint on the validation of completeness and accuracy, as it inhibits screenshots from being taken. In this case, as part of the review, the reviewer should re-run the report and validate that the original report used matches the information in the re-run report.
Strengthen Your SOX Compliance by Implementing Best Practices
There is no perfect science to IPE documentation. But the end goal is to be as detailed as possible. By simply focusing on the fundamental questions and ensuring that your documentation addresses them, your documentation will inevitably improve.
Developing best practices for your team is the cornerstone for any successful audit. Ensure you have the right guidance to make it happen. Our Audit and Assurance team can tailor a SOX environment to meet your needs. Contact us today to learn more.
]]>- The Securities and Exchange Commission (SEC) is promoting the enhancement and standardization of registrants’ disclosures related to cybersecurity risk management, strategy, and governance by adopting a rule that requires public companies to disclose “material” cybersecurity breaches within four days of determining its materiality.
- The SEC wants to know: the processes the companies use to assess, identify, and manage cybersecurity risks, as well as the board’s oversight of such risks and management’s role in assessing and managing those risks.
- The rules apply to nearly all registrants that file periodic reports with the SEC (including foreign private issuers and smaller reporting companies).
- Registrants must also include their risk management, strategy, and governance disclosures in their 2023 annual reports.
The SEC wants public companies to be more transparent with its investors about cybersecurity. On July 26, 2023, it voted 3-2 to adopt new rules on disclosure to promote clarity surrounding “material” breaches and what’s being done to combat them. And it wants them to do this within four days of determining if a cybersecurity breach was material on Form 8-K.
However, delays may be permitted if immediate disclosure of the breach could pose a national security or public safety risk.
Defining “material” disclosures
According to the U.S. Supreme Court, a piece of information is material to investors when its disclosure “would be viewed by the reasonable investor as having significantly altered the ‘total mix’ of information made available.”
Why is the SEC implementing this rule change?
The SEC seeks to protect companies and investors as cybersecurity incidents have increased in number and sophistication in recent years. In their fact sheet they note: “Cybersecurity risks have increased alongside the digitalization of registrants’ operations, the growth of remote work, the ability of criminals to monetize cybersecurity incidents, the use of digital payments, and the increasing reliance on third party service providers for information technology services, including cloud computing technology (…) All of these trends underscored the need for improved disclosure.”
But corporations are contesting the rules, arguing this short announcement period is unreasonable — and could reveal vulnerabilities that could be exploited by more cybercriminals looking to take advantage of a company mid-breach.
What are the requirements for risk management, strategy, and governance disclosures?
Public companies will be required to disclose their cybersecurity breaches within a four-day time period. This disclosure must include additional details too, like the timing of the incident, its impact on the company, and management’s expertise on cybersecurity in Form 10-Ks (and Form 20-Fs for Foreign Filers).
How will the SEC cybersecurity rules affect you?
The SEC has observed that previous cybersecurity announcements have been inconsistent and inadequate.
Many public companies already have plans in place to share sensitive information about their cyber incidents with federal agencies (FBI). Last year, the Cybersecurity and Infrastructure Security Agency (CISA) adopted cybersecurity rules that require critical infrastructure entities to report breaches within three days to CISA. This reporting duplication could prove confusing and time-consuming.
Ultimately, all public companies need robust internal controls and reporting systems to maintain compliance with the SEC requirements. This assumes issuers already have top-tier cybersecurity technology and processes in place. If not, they’ll need to build these functions out to minimize subsequent fallout from investors and regulators when these inadequacies are made public in their reporting.
The SEC strives to protect investors, which isn’t a bad thing. However, the enforcement of these new rules may not be the most logical option to do so.
Ultimately, the question may not necessarily be how many days you should take to disclose your breach but who should actually be regulating cybersecurity, and who has the authority to call the shots. Cybersecurity is no longer a “nice to have” function in an organization.
How we can help
It’s important to stay vigilant to protect your organization from risk and maintain compliance. Our Technology and Cybersecurity Practice can help verify you are compliant and strengthen your overall cybersecurity, so these incidents are less likely to occur. And, if they do, you’ll be ready to mitigate risks sooner— and make progress towards compliance with the SEC’s new rules.
If you are ready to assess your cybersecurity posture, or you have questions about
how the SEC’s new requirements could affect you, schedule a conversation with our Technology and Cybersecurity team today.
Everything changes, except when it doesn’t
Time and time again we’ve seen reactions to various accounting scandals, after which new policies, procedures, and legislation are created and implemented. An example of this is the Sarbanes-Oxley Act (SOX) of 2002, which was a direct result of the accounting scandals at Enron, WorldCom, Global Crossing, Tyco, and Arthur Andersen.
SOX was established to provide additional auditing and financial regulations for publicly held companies to address the failures in corporate governance. Primarily it sets forth a requirement that the governing board, through the use of an audit committee, fulfill its corporate governance and oversight responsibilities for financial reporting by implementing a system that includes internal controls, risk management, and internal and external audit functions.
Governments experience challenges and oversight responsibility similar to those encountered by corporate America. Governance risks can be mitigated by applying the provisions of SOX to the public sector.
Some states and local governments have adopted similar requirements to SOX but, unfortunately, in many cases only after cataclysmic events have already taken place. In California, we only need to look back at the bankruptcy of Orange County and the securities fraud investigation surrounding the City of San Diego as examples of audit committees that were established in response to a breakdown in governance.
Taking your audit committee on the right mission
Governments typically establish audit committees for a number of reasons, which include addressing the risk of fraud, improving audit capabilities, strengthening internal controls, and using it as a tool that increases accountability and transparency. As a result, the mission of the audit committee often includes responsibility for:
- Oversight of the external audit.
- Oversight of the internal audit function.
- Oversight for internal controls and risk management.
Chart(er) your course
Most successful audit committees are created by a formal mandate by the governing board and, in some cases, a voter-approved charter. Mandates establish the mission of the committee and define the responsibilities and activities that the audit committee is expected to accomplish. A wide variety of items can be included in the mandate.
Creating the governing board’s resolution is the first step on the road to your audit committee’s success.

Follow the leader(ship)
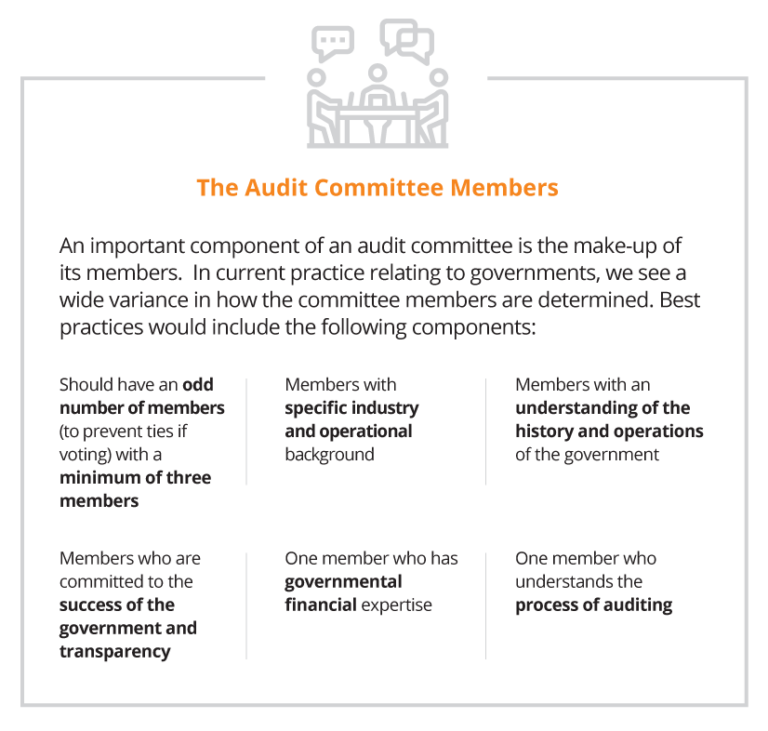
In practice we see a combination of these attributes, ranging from the full board acting as the audit committee, committees with one or more independent outsiders appointed by the board, and/or members from management and combinations of all of the above. While there are advantages and disadvantages for all of these approaches, each government needs to evaluate how to work within their own governance structure to best arrive at the most workable solution.
Strike the right balance between cost and risk
The overriding responsibility of the audit committee is to perform its oversight responsibilities related to the significant risks associated with the financial reporting and operational results of the government. This is followed closely by the need to work with management, internal auditors and the external auditors in identifying and implementing the appropriate internal controls that will reduce those risks to an acceptable level. While the cost of establishing and enforcing a level of zero risk tolerance is cost prohibitive, the audit committee should be looking for the proper balance of cost and a reduced level of risk.
Engage your audit committee with regular meetings
Depending on the complexity and activity levels of the government, the audit committee should meet at least three times a year. In larger governments, with robust systems and reporting, it’s a good practice to call for monthly meetings with the ability to add special purpose meetings as needed. These meetings should address the following:
External Auditors
- Confirmation of the annual financial statement and compliance audit, including scope and timing.
- Ad hoc reporting on issues where potential fraud or abuse have been identified.
- Receipt and review of the final financial statements and auditor’s reports
- Opinion on the financial statements and compliance audit;
- Internal controls over financial reporting and grants; and
- Violations of laws and regulations.
Internal Auditors
- Review of updated risk assessments over identified areas of risk.
- Review of annual audit plan, including status of the prior year’s efforts.
- Status reports of ongoing and completed audits.
- Reporting of the status of corrective action plans, including conditions noted, management’s response, steps taken to correct the conditions, expected time-line for full implementation of the corrective action and planned timing to verify the corrective action plan has been implemented.
Establish resources that are at the ready
Audit committees should be given the resources and authority to acquire additional expertise as and when required. These resources may include, but are not limited to, technical experts in accounting, auditing, operations, debt offerings, securities lending, cybersecurity, and legal services.
Taking extra steps now will save time later
While no system can guarantee breakdowns will not occur, a properly established audit committee will demonstrate for both elected officials and executive management that on behalf of their constituents they have taken the proper steps to reduce these risks to an acceptable tolerance level. History has shown over and over again that breakdowns in governance lead to fraud, waste and abuse. Don’t be deluded into thinking that it will never happen to your organization. Make sure it doesn’t happen on your watch.
]]>What is the cannabis banking crisis?
Very simply put, the conflict between state and local cannabis laws that allow for adult- and medicinal-use of cannabis are in conflict with federal laws that categorize cannabis as a Schedule I controlled substance. As a result, major banking institutions are reluctant to provide traditional banking services to cannabis companies due to the risk of federal prosecution for money laundering or a variety of other offenses.
As a result, the cannabis industry is almost exclusively cash-based. Cannabis business operations – including payroll, rent/lease payments, vendor payments and taxes – are primarily conducted with cash. This results in hundreds of thousands of dollars in cash being moved between locations, simply to pay farms or manufacturers, or even to pay taxes. This inefficient system leads to a wide variety of issues, including significant operational difficulties, and growing risk threats from both untrustworthy employees and out right robbery.
Cannabis businesses have found a number of creative ways to navigate the banking issue. Some business restructure so a professional services firm, not directly touching the cannabis, provides payroll and other financial services. Shops and dispensaries have adopted a variety of debit or gift card payment systems. And finally, a handful of cannabis operators have established relationships with local credit unions willing to work with the industry. But the vast majority of cannabis operators must navigate daily risks related to the collection and remittance of large cash sums.
The banking crisis hearing
“We’re trying to examine how outdated banking regulations on the federal level are hindering reform on the state level when it comes to marijuana,” said Democratic Congressman Gregory Meeks, chairman of the Consumer Protection and Financial Institutions subcommittee, in advance of Wednesday’s hearing. The event brought together a wide range of affected parties, including representatives of credit unions and banks, cannabis industry advocates, and finally government officials advocating for responsible cannabis laws.
The hearing was called to discuss the Secure and Fair Enforcement Banking Act of 2019 (SAFE act). The bill was introduced by a bipartisan coalition that includes Colorado Democratic Rep. Ed Perlmutter, Washington Democratic Rep. Denny Heck and Ohio Republicans, Rep. Steve Stivers and Rep. Warren Davidson. The SAFE act seeks: “To create protections for depository institutions that provide financial services to cannabis-related legitimate businesses, and for other purposes.”
Cannabis banking advocates emerge
Prior to the hearing, the American Bankers Association offered public support for the SAFE act, stating in part: “Simply excluding legal state cannabis activity from the banking sector has not prevented the growth and spread of this industry, but providing access to the banking system could help facilitate public safety, streamline tax payments, and enable effective oversight in the states where voters have chosen to embrace cannabis legalization.”
Fiona Ma, Treasurer for the State of California, offered her support for the bill in a written testimony that reads in part: “an effective safe harbor mechanism in federal law promotes the safety of the public, improves the efficiency of collecting the taxes and fees we use to regulate the industry, and does not allow the banks and credit unions to totally abdicate their responsibilities to know their customers and avoid illicit money laundering.”
“(Current laws) encourage tax fraud, add expensive monitoring and bookkeeping expenses and—most importantly—leave legitimate businesses vulnerable to theft, robbery and the violence that accompany those crimes,” said Maj. Neill Franklin, Executive Director of the Law Enforcement Action Partnership (LEAP). He closed his passionate testimony by stating that the “safety of thousands of employees, business owners, security personnel, police officers and community members is in your hands.”
What can cannabis businesses do until laws change?
The primary purpose of the hearing was to create public momentum for a change in cannabis banking laws. The House Financial Services subcommittee heard hours of public testimony, largely in support of changing federal laws to support the cannabis industry. While nothing concrete emerged from the hearing, allowing so many influential advocates and politicians to publicly support the cannabis industry represents a major step-forward.
It will be a long process before any laws change, but in the meantime there are a number of legal actions a cannabis business can take to alleviate the stress of being denied traditional banking relationships. Most of these, including restructuring a business or implementing alternative payment systems, are complex activities that require professional guidance to execute successfully.
Additionally, there are a number of cash management solutions and internal controls all cannabis businesses should implement to limit opportunities for fraud and criminal abuse, both internally and externally. The MGO | ELLO Cannabis Alliance has long been an advocate for responsible practices regarding cash management in the cannabis industry. The Alliance provides a comprehensive suite of risk management solutions designed to promote operational best practices in the cannabis industry.
For more information or to arrange a consultation, please contact us.
About the author:
Linda Hurley is the leader of the MGO | ELLO Alliance Governance, Risk, and Compliance practice. She has over 20 years of experience providing risk advisory, compliance, accounting, internal audit, and auditing services to a wide variety of public and private companies. She is primarily focused on providing cannabis enterprises with a holistic view of their risk and compliance needs. She designs and implements internal controls, risk management procedures, and governance practices that support every level of a cannabis organization.
]]>