- The Securities and Exchange Commission (SEC) is promoting the enhancement and standardization of registrants’ disclosures related to cybersecurity risk management, strategy, and governance by adopting a rule that requires public companies to disclose “material” cybersecurity breaches within four days of determining its materiality.
- The SEC wants to know: the processes the companies use to assess, identify, and manage cybersecurity risks, as well as the board’s oversight of such risks and management’s role in assessing and managing those risks.
- The rules apply to nearly all registrants that file periodic reports with the SEC (including foreign private issuers and smaller reporting companies).
- Registrants must also include their risk management, strategy, and governance disclosures in their 2023 annual reports.
The SEC wants public companies to be more transparent with its investors about cybersecurity. On July 26, 2023, it voted 3-2 to adopt new rules on disclosure to promote clarity surrounding “material” breaches and what’s being done to combat them. And it wants them to do this within four days of determining if a cybersecurity breach was material on Form 8-K.
However, delays may be permitted if immediate disclosure of the breach could pose a national security or public safety risk.
Defining “material” disclosures
According to the U.S. Supreme Court, a piece of information is material to investors when its disclosure “would be viewed by the reasonable investor as having significantly altered the ‘total mix’ of information made available.”
Why is the SEC implementing this rule change?
The SEC seeks to protect companies and investors as cybersecurity incidents have increased in number and sophistication in recent years. In their fact sheet they note: “Cybersecurity risks have increased alongside the digitalization of registrants’ operations, the growth of remote work, the ability of criminals to monetize cybersecurity incidents, the use of digital payments, and the increasing reliance on third party service providers for information technology services, including cloud computing technology (…) All of these trends underscored the need for improved disclosure.”
But corporations are contesting the rules, arguing this short announcement period is unreasonable — and could reveal vulnerabilities that could be exploited by more cybercriminals looking to take advantage of a company mid-breach.
What are the requirements for risk management, strategy, and governance disclosures?
Public companies will be required to disclose their cybersecurity breaches within a four-day time period. This disclosure must include additional details too, like the timing of the incident, its impact on the company, and management’s expertise on cybersecurity in Form 10-Ks (and Form 20-Fs for Foreign Filers).
How will the SEC cybersecurity rules affect you?
The SEC has observed that previous cybersecurity announcements have been inconsistent and inadequate.
Many public companies already have plans in place to share sensitive information about their cyber incidents with federal agencies (FBI). Last year, the Cybersecurity and Infrastructure Security Agency (CISA) adopted cybersecurity rules that require critical infrastructure entities to report breaches within three days to CISA. This reporting duplication could prove confusing and time-consuming.
Ultimately, all public companies need robust internal controls and reporting systems to maintain compliance with the SEC requirements. This assumes issuers already have top-tier cybersecurity technology and processes in place. If not, they’ll need to build these functions out to minimize subsequent fallout from investors and regulators when these inadequacies are made public in their reporting.
The SEC strives to protect investors, which isn’t a bad thing. However, the enforcement of these new rules may not be the most logical option to do so.
Ultimately, the question may not necessarily be how many days you should take to disclose your breach but who should actually be regulating cybersecurity, and who has the authority to call the shots. Cybersecurity is no longer a “nice to have” function in an organization.
How we can help
It’s important to stay vigilant to protect your organization from risk and maintain compliance. Our Technology and Cybersecurity Practice can help verify you are compliant and strengthen your overall cybersecurity, so these incidents are less likely to occur. And, if they do, you’ll be ready to mitigate risks sooner— and make progress towards compliance with the SEC’s new rules.
If you are ready to assess your cybersecurity posture, or you have questions about
how the SEC’s new requirements could affect you, schedule a conversation with our Technology and Cybersecurity team today.
Proactive planning is vital
State and local governments are frequently constrained by their budgets. Proactive planning spreads both effort and budget into a longer timeframe, which allows investments to be made incrementally and resources to be consistently allocated.
Because cyberattacks are nothing new, many organizations have already prepared some sort of response plan. However, because the pace of cyberattacks and the sophistication of hackers is constantly increasing, your plan should be updated at least annually. A robust plan is a living document that involves cross functional teams that include IT professionals and leadership.
Risks should be identified and prioritized so that urgent needs can be addressed with immediate investments. Although, the complete (or updated) plan may never be complete, the prioritized pieces of it will form a framework through which cybersecurity becomes an ongoing conversation, and a lens through which daily work is viewed.
Have a contingency plan: know who to contact and how
A contingency plan should be in writing. The process of drafting a detailed plan that addresses many different scenarios is time consuming, and it is also necessary. The thought process and discussions that go into thinking through a robust response to a cybersecurity plan are valuable to the whole organization. When a cyberattack occurs, one of the greatest concerns is to stop the loss of sensitive information. Part of contingency planning will involve creating an information classification policy, so your information systems protect the highest value information with the highest level of security.
Contingency planning also involves a communication plan. In what order do you make phone calls to your incident response team, legal counsel, board of directors, insurance agent, or law enforcement? Who needs to know what, when? How do you document your actions?
If you think having these discussions is overwhelming and stressful in the planning stage, imagine what it would be like to try to make critical decisions when your firewall is open, your information systems are locked, and your daily work has come to a halt.
Update your system to reduce risk
State and local governments often have older IT systems, some of which have been in use for 20 years. These systems require patches to prevent cybercrime, and in most cases, the various information systems do not “talk” to each other.
One of the first steps you can take is to update your information systems. Part of this may involve a discussion of a policy manual and potentially some training so that people are aware of the risks that are constantly evolving. A standing IT governance committee may initially be dedicated to the upgrade, and later take on the ongoing task of mitigating cyber risks throughout your organization.
Mitigating some of these risks might include reviewing your cyber insurance policies to ensure that you have adequate coverage for overall data recovery and the cost of business interruption. This committee should also review your backup policies and services to ensure reliable storage in a separate location that is tested periodically to ensure compliance with your contracts.
Prepare to respond to cyberattacks
State and local governments should expect to be targeted — they have access to large amounts of personal information and data. Thus, it is crucial to have a plan that can be immediately put into action to protect this sensitive information for the people and communities you serve. Your response within the first 24 hours of the breach is critical to minimizing damage. With proper planning, even an aggressive attack can be survived with minimal losses.
If your organization is not yet prepared for a cyberattack, or you are interested in proactive planning against a breach, schedule a consultation with the MGO Technology Group or learn more about the services we provide here.
]]>The comment period for these proposed rules lasted for two months, ending on May 9, 2022. During that time, the SEC received more than 100 comments from various sectors, including legal, government, business, and nonprofit. These comments vacillated from critical to supportive, but many had several concerns about the rule’s provisions. For those curious about the specific apprehensions, our Technology and Cybersecurity team analyzes them, as well as the suggested solutions, in this article.
Most common concerns regarding the SEC’s cybersecurity proposal
Within the comments provided on the proposal, there were eight key issues broached along with solutions to these issues.
1. The four-day incident notice deadline
Many commenters believe being given a mere four days to report a cybersecurity incident was not enough time to truly analyze the incident and complete an accurate report. Worried a harried or slapdash report could yield even more security risks, they proposed more flexible solutions to provide accurate disclosures, like:
- A 30-day reporting deadline;
- Government-permitted reporting delays (as needed);
- A modification in the disclosure framework to ensure state notification statutes are exemplified; and
- Additional time for smaller companies to investigate, report, and fully disclose the situation as needed.
2. Law enforcement and national security exceptions
Feedback for the proposed rules also stated some specific incidents should benefit from delayed reporting exceptions, namely those that need to involve law enforcement or security investigations on a larger scale.
This solution allows those grappling with more challenging and involved cybersecurity incidents to remain compliant with the law while doing what is necessary to complete an investigation and strengthen security to prevent future incidents. It also gives law enforcement more freedom to complete their efforts — and prevents publicity that could tip off the attackers, who could then cover their tracks.
3. The definition of key terms
The SEC uses several words that could be misconstrued, have multiple meanings, or are not succinct enough to require disclosures surrounding them. These words, as pointed out in the comments, include:
- Cybersecurity threat,
- Cybersecurity incident, or
- Information systems.
To solve this and streamline compliance reporting requirements, commentors believe the SEC should utilize the thorough and uniform definitions employed by the National Institute of Standards and Technology (NIST), as well as those used in the Cybersecurity Incident Reporting for Critical Infrastructure Act of 2022 (CIRCIA), SEC’s Release Number 33-11028, and the 2016 Presidential Policy Directive on United States Cyber Incident Coordination.
In addition, the SEC can break down each incident or threat into a tier system to accurately encapsulate the severity each tier entails, better describing the impact on the organization.
4. The disclosure of the board of directors’ cybersecurity expertise
Comments also touched on the requirement to include the experience the members of a company’s board of directors have, finding it unnecessary to disclose and tedious to acquire. The suggestions given included eliminating this narrow requirement (primarily because if a board member(s) does not have heavy cybersecurity experience, that could reflect negatively on the company’s prioritization of cybersecurity) even if the company does, in fact, take cybersecurity seriously.
They also call for “cybersecurity expertise” to be defined using broad criteria so smaller companies can meet the requirement without struggling to find an “expert” just to tick a box — or to allow the requirement to meet with a leader at different level in the company besides the board of directors.
5. The accumulation of immaterial events requirement
Another criticism of the proposed rules targets the requirement to list previously undisclosed immaterial cybersecurity incidents, which many comments revealed to find unnecessary and vague, as an incident to one company may be deemed immaterial but found material to another. The lack of consistency and definition means their solution is to either scratch the requirement or, alternatively, provide more guidance on what these incidents should entail to be included, as well as an example of one — and set a one-year limit, as this requirement does not include one.
6. Security program disclosures
Requiring a company to disclose security program-related protocols and plans, like strategies and risk management tactics would, comments to the proposal argue, make the company more vulnerable to future security breaches — as well as inadvertently divulge protected information. To mitigate this, critics suggest removing the requirement to keep companies (and their security plans) safe, allowing a vague summary of the program to meet the requirement; or introducing a confidentiality clause.
7. Fear of regulatory discord
As cybersecurity becomes a bigger issue for all industries across the country, the SEC’s proposal could contradict other states’ laws and requirements regarding cybersecurity (and their varying definitions, triggers, timings, and more). This could create confusion for companies who want to remain compliant in the event of a cyberattack but are unsure of which requirements they must meet to determine if a breach has, in fact, occurred. Readers of the proposed rule believe creating standardized terms and requirements can help. Plus, the SEC should demonstrate how it will work with the other regulations so companies can align their requirements in a streamlined way.
8. Safe harbor provisions
It seemed to many if a company has already reported a material cybersecurity risk, it is redundant to be required to report it again via the Form 8-K. The provided (short) timeframe, too, could cause issues — in the case of a third-party breach, a company may hurry to complete the form without confirming it to be reliable or accurate, defeating the entire point of the form.
This requirement invited split opinions. Some comments mentioned two “safe harbors” (i.e., double reporting) is a good thing, helping the SEC to promote consistent disclosure. Others, however, stated that including both would be redundant, especially with a tight deadline and the lack of clear definitions for these incidents.
Our perspective on the response to the SEC’s cybersecurity proposal
As the SEC strives to increase transparency and prevent malicious cyberattacks, cybersecurity disclosure requirements will continue to change and strengthen. The number of comments received on this proposed rule indicates that companies across industries are not only invested in what these disclosure requirements mean, but they are willing to do what is necessary (albeit logical) to enhance and standardize the way they protect themselves and disclose risk.
Looking forward, the SEC will take these comments into consideration for the next draft of the proposal.
How we can help
While you wait for the next draft of the proposal, remember to stay vigilant—not only to protect your organization, but also to maintain compliance. To stay up to date, bookmark the SEC’s Cybersecurity news and our Technology and Cybersecurity insight library.
Professional service firms like MGO help verify you are compliant and strengthen your overall cybersecurity — so these incidents are less likely to occur, and if they do, you will be ready to mitigate risks at once. Let us know if you are ready to assess your cybersecurity or get started on a SOC for Cybersecurity.
For insights tailored to your company and industry, schedule a conversation with our Technology and Cybersecurity team today.
]]>The SEC’s concerns for reliable information systems aren’t without merit. Increased vulnerabilities and threats including remote work, reliance on cloud and third-party services, virtual and digital payments, and sophisticated malware and ransomware, prompted the proposal of these rules to mitigate potential costs and consequences for businesses and investors. Previous standards were not always adhered to, and cybersecurity disclosures were sometimes dismissed with investors and consumers left uninformed.
To provide more transparent, timely, and consistent information, the SEC has broken down the additional disclosures into four categories:
- Material cybersecurity incidents
- Risk management and strategy
- Governance
- Expertise
For anyone unfamiliar with the SEC’s new cybersecurity requirements, our Technology and Cybersecurity practice breaks down what they are and how you can best adhere to them to keep your organization compliant and secure.
Breaking down material cybersecurity incident disclosures
Under this rule, a company will be required to disclose cybersecurity breaches within four days of discovering the incident (note: this is not four days from the date of the breach itself). To determine if the incident involves material information, the company must consider if a shareholder would find the information breached relevant to making an investment decision. Examples of material cybersecurity breaches that would require this reporting include an impact on:
- Operational technology systems
- Stolen information with intent to extort
- Compromise of data or a network
- Ransomware attacks
- Theft of sensitive business information
Within this disclosure, a company is required to report as much as they can about the incident, including:
- When the incident was discovered
- A brief description of what the incident entailed
- Whether data was altered, taken, accessed, or used by the attacker
- How the incident directly affected operations
- If the company has resolved, or is resolving, the issue
A company is not required to disclose certain specific or technical details that could further hinder a resolution or assist attackers in perpetuating a breach, like its response plans, security systems, networks, and other existing vulnerabilities.
Risk management and strategy rules
The proposed amendment would also require a “consistent and informative” disclosure of a company’s cybersecurity risk management and strategy — including not only its own risk management standards but also third-party service providers and their mitigation.
The company would be expected to disclose how its cybersecurity risk management and strategy factor into the overall business strategy and business model related to the collection and handling of sensitive data and the business’s level of dependency on technology. These disclosures will allow investors to possess the information necessary to evaluate a company’s cybersecurity risk and its ability to potentially manage the impact of an attack.
Within this rule, a company would be required to disclose if it:
- Has a cybersecurity risk assessment and management program (with an attached description of said program).
- Uses third parties with that program, and, if so, has policies and procedures to evaluate their associated cyber risks.
- Has a cybersecurity program that considers prior cybersecurity incidents.
- Has had an incident that has affected or could affect the company.
- Has considered the cybersecurity risks in its business strategy, planning, and capital allocation — and how.
Key governance rules
The SEC’s proposal will ensure a company discloses how its board and management handle and take responsibility for cyber risk, including its general cybersecurity governance and the overall scope of the board’s oversight. Does the duty fall to the entire board, a committee, or specific board members? Are there processes for informing the board of potential risks, and how often do they discuss them? Is cyber risk considered a part of overall strategy and risk management?
In addition, it would require a description of the specified management’s role in managing the cybersecurity risks — like expertise, experience, and general role in implementing the cybersecurity measures. Other disclosures in this category include:
- Responsibilities for evaluating and managing cyber risk.
- If the company has a chief information security officer or similar role, and expertise level of the individual.
- How managers responsible for cybersecurity are informed and monitor efforts like discovery, identification, and remediation of breaches.
- How often the managers responsible for cybersecurity report to the board or committee.
Expertise
Under this amendment, companies would be required to disclose their directors’ expertise in cybersecurity, citing each by name along with prior work experience, level of expertise, certifications and degrees, and skillset.
Prepare your organization with a SOC assessment for cybersecurity
To know where your organization stands with its cybersecurity risks and strategy, an assessment is important — especially a System and Organization Controls (SOC) for Cybersecurity, a framework allowing organizations to communicate the effectiveness of their risk management program and information about their cybersecurity.
As we know, the recently issued SEC proposal would require companies to detail their cybersecurity risks and incidents as well as related books and records for up to five years. Participating in a SOC for Cybersecurity would enable your organization to prepare accordingly with no blind spots. This is especially important if your organization utilizes third-party risk management, a growing concern for many firms due to the increased risk associated with them.
With the SOC for Cybersecurity, you can equip your management, directors, investors, business partners, and other stakeholders with the controls they need to ensure you remain compliant with the SEC’s new additions.
Our perspective
While there have been no updates since the proposed rules, it is important to stay vigilant — not only to protect your organization, but also to maintain compliance. To stay up to date, bookmark the SEC’s Cybersecurity news and our Technology and Cybersecurity insight library.
Professional service firms like MGO help verify you are compliant and strengthen your overall cybersecurity — so these incidents are less likely to occur, and if they do, you will be ready to mitigate risks at once. Let us know if you are ready to assess your cybersecurity or get started on a SOC for Cybersecurity.
For insights tailored to your company and industry, schedule a conversation with our Technology and Cybersecurity team today.
]]>Proactive planning is vital
State and local governments are frequently constrained by their budgets. Proactive planning spreads both effort and budget into a longer timeframe, which allows investments to be made incrementally and resources to be consistently allocated.
Because cyberattacks are nothing new, many organizations have already prepared some sort of response plan. However, because the pace of cyberattacks and the sophistication of hackers is constantly increasing, your plan should be updated at least annually. A robust plan is a living document that involves cross functional teams that include IT professionals and leadership.
Risks should be identified and prioritized so that urgent needs can be addressed with immediate investments. Although, the complete (or updated) plan may never be complete, the prioritized pieces of it will form a framework through which cybersecurity becomes an ongoing conversation, and a lens through which daily work is viewed.
Have a contingency plan: know who to contact and how
A contingency plan should be in writing. The process of drafting a detailed plan that addresses many different scenarios is time consuming, and it is also necessary. The thought process and discussions that go into thinking through a robust response to a cybersecurity plan are valuable to the whole organization. When a cyberattack occurs, one of the greatest concerns is to stop the loss of sensitive information. Part of contingency planning will involve creating an information classification policy, so your information systems protect the highest value information with the highest level of security.
Contingency planning also involves a communication plan. In what order do you make phone calls to your incident response team, legal counsel, board of directors, insurance agent, or law enforcement? Who needs to know what, when? How do you document your actions?
If you think having these discussions is overwhelming and stressful in the planning stage, imagine what it would be like to try to make critical decisions when your firewall is open, your information systems are locked, and your daily work has come to a halt.
Update your system to reduce risk
State and local governments often have older IT systems, some of which have been in use for 20 years. These systems require patches to prevent cybercrime, and in most cases, the various information systems do not “talk” to each other.
One of the first steps you can take is to update your information systems. Part of this may involve a discussion of a policy manual and potentially some training so that people are aware of the risks that are constantly evolving. A standing IT governance committee may initially be dedicated to the upgrade, and later take on the ongoing task of mitigating cyber risks throughout your organization.
Mitigating some of these risks might include reviewing your cyber insurance policies to ensure that you have adequate coverage for overall data recovery and the cost of business interruption. This committee should also review your backup policies and services to ensure reliable storage in a separate location that is tested periodically to ensure compliance with your contracts.
Prepare to respond to cyberattacks
State and local governments should expect to be targeted — they have access to large amounts of personal information and data. Thus, it is crucial to have a plan that can be immediately put into action to protect this sensitive information for the people and communities you serve. Your response within the first 24 hours of the breach is critical to minimizing damage. With proper planning, even an aggressive attack can be survived with minimal losses.
If your organization is not yet prepared for a cyberattack, or you are interested in proactive planning against a breach, schedule a consultation with the MGO Technology Group or learn more about the services we provide here.
Because organizations’ vulnerabilities are being actively exploited right now, it is crucial to see if this could affect your organization. Read more about the recommended actions to protect your security and reach out to MGO’s Johnny Mays with any questions.
Immediate defense actions recommended include:
- Ensure you are up to date on the latest patches and system updates
- Update your organization’s blocklist (e.g., if Fortinet is not used, don’t allow key aspects of it to run on your system)
- Ensure your backups are taking place—and they are stored air gapped separate from your live network
- Implement network segmentation to restrict a potential adversary’s ability for lateral movement
- Perform a user access review/permissions clean-up to ensure admin/elevated access privileges are restricted only to those who need them. Employ the principle of least privilege for all users in your organization. If a subject does not need an access right, they should not have that right (no extraneous access)
- Instate multi-factor authentication to stop attackers in their tracks
- Require strong passwords
- Limit remote desktop protocol (RDP) as much as possible. Disable it where it is not needed and monitor RDP access/activity logs.
- Secure remote access by avoiding the use of public Wi-fi and adding VPN for remote access
- Add an email banner to emails received from outside your organization to defend against phishing
- Provide security training
- Monitor/disable the ability to click on hyperlinks in unknown emails
Proactive planning is vital.
Having a defined plan allows your organization to react seamlessly, protecting your company’s assets, data, and activity. This means preparing proactively and practicing periodically to be ready to execute the plan when an attack comes.
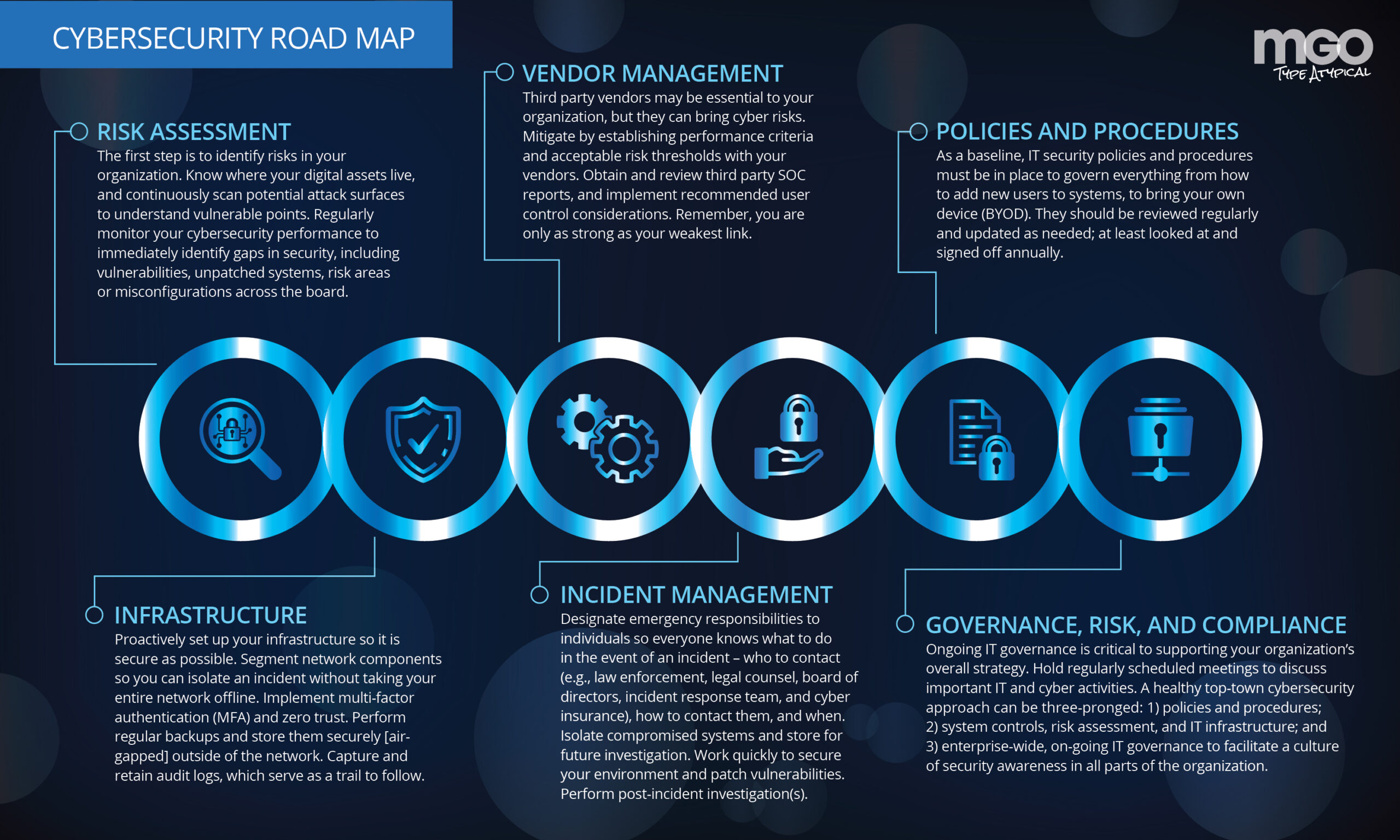
MGO has developed a roadmap to help organizations mitigate attacks within the first 24 hours of a breach. Instead of paying the ransom, ensure your company gets back to business after an attack. Understanding these top nine issues will prepare you to emerge unscathed after those first 24 hours.
1. Know who to contact — and how. When a cyberattack occurs, you will want to notify several groups within the first 24 hours: law enforcement, your legal counsel, the board of directors, incident response team, and cyber insurance. Think of them as your first line of defense in an emergency—you call them for help.
End users—individuals whose information or data is directly impacted—can be notified about the breach later, as there is a substantial amount of confidentiality involved. Businesses must avoid disclosing any weaknesses or exposures immediately following an attack.
2. Isolate and investigate.
Once you know which computers or systems have been affected, you want to isolate those involved and limit the damage. This way, you can utilize them for future investigation. By doing this, you can learn what went wrong, where your potential weak spots are, and how to avoid future mistakes. You want to move quickly to secure the systems and fix vulnerabilities — the only thing worse than one breach is multiple breaches. Remember to take all affected equipment offline and update your credentials so hackers cannot use the old ones to get back inside. Before completely shutting down any equipment, be sure you have surveyed the damage with a snapshot or copy the authorities can later review. An alternative to this is taking the affected equipment off the network to quarantine it—there will be no need to shut it down as it has been effectively partitioned from the rest of the network.
The designated incident response team will perform an immediate internal investigation upon isolation to determine the attack’s impact on critical business functions so the organization can jump into action to remediate. This team will also use their analysis to identify the attacker and discover other vulnerabilities where security can be tightened.
3. Implement manual procedures.
Before a breach, you want to define any manual, non-automatic procedures your team will need to implement during or after an attack. These procedures will allow for business “as usual” even during disruption. It is crucial to have these manual procedures in place already so that when the time arrives to use them, you know exactly what to do.
The implementation of these manual procedures must occur within the first 24 hours of the attack.
4. Contact your security service provider.
Work with your team of forensic experts. They will be able to determine if encryption was enabled at the time of the breach. They will analyze preserved data, review logs to see who had access to it and verify the compromised information. Your incident response team will also hand you forensic reports based on their findings, which you can use to take remedial measures.
5. Know your cyber insurance.
Review your cyber insurance regularly to make sure the policy provides the right level of coverage for your organization.
Generally, you want policies that support data recovery and cover the costs of business interruption.
6. Designate responsibility — ahead of time.
A cyberattack can cause chaos — it is designed to do so. It is crucial to designate responsibilities to different members of your cyber team so that everyone knows what is expected of them to bring the situation under control when a breach occurs. This will allow your organization to respond more seamlessly to the event.
7. Retain audit logs.
Audit logs provide a sort of breadcrumb trail to follow at an information systems level. (I’d discuss who is responsible for making sure these logs are functioning.) Ensure your audit logs are retained in the system so that you can respond within the first 24 hours of the breach. If you get attacked and do not have the audit logs, you probably won’t figure out what happened. This best practice generally suggests that logs should be retained for six months to a year.
8. Segment your network.
Setting up your network ahead of time to be segmented is essential because if a breach occurs on one server or site, it won’t lead to another breach. This allows you to isolate a breach and shut down one segment instead of taking the entire network offline. Your annual security assessment would be able to tell you if your segmentation plan was effective in containing the breach after the initial 24 hours.
9. Store backups — and back up daily at least.
The best way to recover from a ransomware attack is to have your backups ready to use. For this to be effective, your backups must be reliable; stored in a safe, separate place, and tested periodically to ensure that if something happens, you can bring the organization back online within those first 24 hours.
Be prepared for those first 24 hours.
Every organization should expect to be targeted, and all organizations need to have a plan of action to mitigate their risk when a cyberattack occurs. Because the first 24 hours of a breach are so crucial, the roadmap should be dedicated to helping operations protect themselves and prevent the attack from going to other areas of the organization. By preparing a plan, you will respond appropriately and get the company back on track with minimal lost revenue.
]]>As a large percentage of the US workforce transitions to work from home (WFH) situations due to the COVID-19 pandemic, we’ve looked at challenges that many organizations may face in setting up work from home (WFH) environments, as well as one of the most common tools used in making WFH resources available to your staff. Today, we’ll look at some of the best advice you, your IT team, or your managed service provider can provide your staff as they continue to work from home.
1. Turn on your corporate VPN, if provided, as soon as you login.
As stated in our previous article, the Virtual Private Network (VPN) is designed to make the connection between your employees and your corporate resources secure. Employees should get in the habit of activating the VPN as soon as their work or home laptops are turned on.
2. Change your password regularly
It is recommended that firms have a special procedure for incorporating password changes while employees are remote. For example, some setups require employees to be logged into the VPN before they initiate the password change on their own devices. Your employer’s technical staff or MSP should formalized the procedure and make it publicly available to you.
3. Avoid sharing your password
Sharing of passwords goes against almost everything we know about cybersecurity. However, in these times extraneous circumstances may require a transfer of passwords, especially in cases of troubleshooting. Try to avoid sharing your password, but if you must, follow these simple rules:
- ONLY share your password with a trusted source whose identity you can verify. This includes your local IT department or MSP. If you have any doubt about who you are sharing your password with, DO NOT SHARE IT. The inconvenience of not sharing your password is not worth the potential damage that could be caused by a data breach.
- ONLY share your password through a secure method. The safest is a phone call, but if you must use a messaging service, try to stick to simple SMS and do not use apps such as Facebook Messenger.
- As soon as the task requiring the password share is completed, change your password immediately. The longer this action is delayed the longer you and your firm are at risk.
4. Avoid letting other family members use your corporate laptop or devices.
It might be tempting to hand off your device to a family member for a simple task, but remember that in most cases you do not own your corporate devices and are liable for any damage or data leakage caused by your family members.
5. Be mindful of who is around you both virtually and in person.
Picture this scenario: You are on a call with someone in which confidential information is shared. A family member overhears and decides to share this information over their personal social media page for exposure, perhaps not understanding the confidential nature of this information. Suddenly you have a potential data breach of confidential information on your hands.
Though quarters might be tight, it’s important to be cognizant of who is around you at all times. This may include having discussions with family members so they understand that what might see or hear from you is confidential.
6. Remember that, in most cases, your work devices are not yours.
When you are issued a device, it usually comes the legal caveat that the device still belongs to the company along with anything that is introduced to that device. In most employment agreements the employer stipulates that they have the right to access, search, seize, and erase the device at any time. So if you have personal files and photos on any of your work devices, it would be prudent to move or back them up to a personal storage space.
7. Always listen to and follow the advice and notices of your IT staff.
As the COVID-19 situation progresses, new guidelines and rules may have to be developed. These should be communicated to you by your technical staff, HR personnel, or MSP. Assuming the source is verified, you should follow their guidance to the best of your abilities.
8. Never hesitate to ask questions of your IT staff if you are unsure of something.
In the realm of IT Security, there are no stupid questions. Your company has every interest in keeping you productive and safe. You can do your part by engaging with the IT staff or MSP through established channels. This can range from a critical system failure all the way down to reaching out to verify if new guidance you might have received did in fact come from the.
9. Consider how your family activities might affect available bandwidth in your home.
As you work from home, the strain on your home internet connection might become apparent as more devices are using the connection for longer periods of time. This will be especially true if you are home with other family members. You may notice lags on conference calls or the VPN taking longer to connect than usual.
While you can work with your internet service provider to see if you can increase the amount of bandwidth allocated to your house you may also want to consider network usability times with your family. This may be difficult, especially given the bandwidth resources needed for online school learning, but could be a necessary step in ensuring you have enough bandwidth during critical times such as video calls and high volume file transfers.
Ready to learn more? Join us for our up-coming webinar: Cultivating a Culture of Cybersecurity Awareness. Register here.
Or you can schedule a consultation with the MGO Technology Group here.
]]>The novel coronavirus/COVID-19 is having a growing and dramatic impact on us personally and on the global economy. Throughout this article we will provide business leaders with a perspective on the evolving situation and implications for their technology companies.
On one end of the spectrum, we are faced with new and difficult economic challenges – how we pivot and overcome fear in the face of adversity will define who the future leaders in the technology industry will be. On the other end of the spectrum, new growth opportunities in the industry remind us all that when technology is used right, it makes what was once was impossible, possible.
“Remember that weaknesses don’t matter if you find solutions.”
-Ray Dalio
The novel coronavirus is affecting technology in a variety of ways, which makes the pandemic’s impact very difficult to monitor and evaluate. “The economic outlook is evolving on a daily basis,” observed Federal Reserve Chairman Jerome Powell. “And it really is depending heavily on the spread of the virus, and the measures taken to affect it, and how long that goes on. And that’s just not something that’s knowable.
Writing down a forecast in these circumstances is challenging at best, and would lack usability as a result of the uncertainties noted above.
Despite the current clouds, at this point certain conclusions seem obvious:
– Life has changed and change creates opportunities: At one end of the spectrum sits Amazon and its plan to hire 100,000 workers and implement an immediate $2.00-an-hour raise through April. Examples of other tech sectors on this end of the spectrum include cloud computing, cyber security, EdTech and telemedicine.
– Consumer fulfillment? Yes. Consumer touch? Not so much: At the other end of the spectrum sits countless high-tech conferences (including Facebook’s F8 Developer Summit, Google’s I/O, Apple’s WWDC, and Microsoft Build to name a few) that have been postponed or moved to online-only. That’s likely a multimillion-dollar loss for the vendors and other companies that service these events. Similarly affected are in-person, consumer-focused tech sectors, such as payment processing and ridesharing, among others.
Impact of supply chain disruptions
At a macro level, the critical areas that are weighing heavily on the industry are production and supply chain management (mainly international), which have a direct financial impact on technology companies.
Production has been adversely affected by the virus’ effect on a main production source, China, and on other Asian countries that supply China. Consider electronics products: given that the concentration of products assembled in China is huge, significant problems are created for the entire tech industry, everything from semiconductors and printed circuit boards, to complete systems for consumer electronics, cars and industrial applications.
- A special Institute of Supply Management survey found COVID-19 kicked off supply chain disruptions for almost 75% of U.S. companies, with many of them now forecasting revenue declines for expected 2020 results. Additionally, of the companies expecting a negative impact, 80% expect the severity of the disruptions to accelerate beginning in the second quarter.
- Survey respondents, of which 81% are firms with revenues of less than $10 billion, cite a variety of developments that are impacting the supply chain, including the following estimates:
- Chinese manufacturers are operating at 50% of capacity
- 44% of companies taking part in the survey reported not having a plan in place to combat supply disruptions
- 62% of respondents say their deliveries from China are delayed
- 53% of respondents are having difficulty getting supply-chain information from China
- 48% are experiencing delays transporting goods within China
- TrendForce, a market research company, offers a dire forecast for first quarter global smartphone production: a 10% decline from expectations prior to the COVID-19 outbreak. Double-digit shipment declines also are forecast for smartwatches (-16 percent), notebooks (-12.3%), smart speakers (-12.1%) and video game consoles (-10.1%).
- In a recent survey aimed at determining the outbreak’s effect on supply chains, IPC International Inc., a trade association for the electronics manufacturing industry, found that – of 101 companies polled – 22 percent expect fewer new product introductions this year as a result of the COVID-19 outbreak.
- The study also found strong sentiments that COVID-19 will hurt worldwide enterprise and consumer IT spending. Thanks to significant government stimulus in the U.S., China, and elsewhere, some of the deferred spending is expected to return gradually in 2020’s second half.
- Tech sectors that touch (or are dependent upon) consumer spending also face difficult times. Uber Technologies Inc. and Lyft Inc. have already seen U.S. ridership plunge in March as Americans were ordered to stay at home.
Financial technology faces hardship
FinTech, with both B2C and B2B characteristics, sits somewhere in the middle of the overall tech industry.
Companies providing financial services – such as payments processing and lending to small companies, are experiencing a decline as those companies (especially retailers and eateries) close their doors temporarily and, in some cases, permanently.
PayPal Holdings Inc. (PYPL), which processes payments for 24 million online merchants, expects lower-than-forecast first quarter revenue because of less cross-border e-commerce activity. The company also has a $2.6 billion book of loans to small businesses and could face problems if borrowers start to miss payments or default entirely.
Square Inc. (SQ), a popular payment system, especially for small businesses, is being hit both by the drop-off in transaction volume and in its lending activities as well.
Opportunities for education technology and telecommunication
On the positive side, the widespread move to home-schooling and working from home has focused a spotlight on EdTech- and telecommuting-related companies, as well as companies providing office equipment, software, cloud computing, networking infrastructure and network security.
EdTech companies expected to get a boost include 2U, Inc., Chegg, Inc., Pluralsight, Inc., and K12, Inc. Among software companies that provide remote access and collaboration, Zoom, Slack, GoToMyPC, Zoho Remotely, Microsoft Office365 and Atlassian are forecast to outperform.
In the area of memory products, DRAM and NAND are not expected to be affected by the outbreak, as semiconductor fabrications are highly automated, with very low demands for manpower. These companies stocked up on materials before the Chinese New Year, so there shouldn’t be any short-term shortages.
Navigating a new reality
One certainty is that things will be different going forward. Optimists hope COVID-19 mimics the performances of SARS in 2002, the H1N1 influenza of 2009, and MERS in 2012. Come and gone more quickly than expected…permitting markets, economies and societies to bounce back rapidly. Pessimists, however, point to the longer duration and impact of HIV/AIDS.
The final impact is to be determined, of course, but it is clear that COVID-19 will leave an enormous impact on how we consume, how we learn, how we work and how we socialize and communicate.
Telecommuting
Telecommuting is here to stay – good news for many business enterprises that will benefit from lower staff and facility costs, and thereby higher profits. Makers of the applications facilitating telecommunication will also benefit greatly. Whereas smaller businesses that depend upon face-to-face interaction may face an uncertain future.
Online learning
Online education means larger class sizes, higher revenue per class and reduced operating costs at colleges and universities. It’s not a panacea for all types of learning, however; chemistry and biology labs and the arts being noteworthy examples.
Telemedicine
Until now, the idea of telemedicine was always a concept for the future. But, much like the way content will be consumed going forward, the way healthcare delivery occurs will also be disrupted. There are additional, cascading benefits as well: a video call keeps the patient out of the transit system, out of the waiting room and, most importantly, away from patients who need critical care.
Streaming
The jury is still out on movie theaters and live events. Streaming clearly will become an even more important way to deliver and consume content. Current streaming companies and those that pivot in this direction will benefit.
Internet infrastructure
Even with the unfortunate amounts of misinformation, the importance of the internet as a critical social, educational and communications solution has been evident from the start of the pandemic. Its importance will only grow in the future. Bandwidth will be a challenge, however, as certain parts of the country are served by an inferior infrastructure.
Supply chains
A huge percentage of U.S. companies are dependent on supply chains that have China as the priority provider. With China capacity halved, many U.S. companies don’t have a Plan B. It’s likely that popular products will be unavailable in coming months and companies are going to have to reconfigure supply chains going forward. This could cause some near- to mid-term dislocations.
What technology companies should focus on now
The Coronavirus pandemic will continue to affect profits and liquidity by increasing procurement expenses and capital costs while simultaneously forcing customers to defer purchases. In some cases, these consequences are already apparent. To protect tech companies’ businesses and to ensure they rebound as quickly as possible, tech companies will benefit from financial stress tests in which they examine their current cash flows and balance sheets. They can then determine how company finances might evolve if any of the scenarios defined by their stress tests materialize.
“Identify your problems, but give your power and energy to solutions.”
-Tony Robbins
To protect the ecosystem, companies in technology industry could look beyond their walls by setting new spending priorities considering different time horizons:
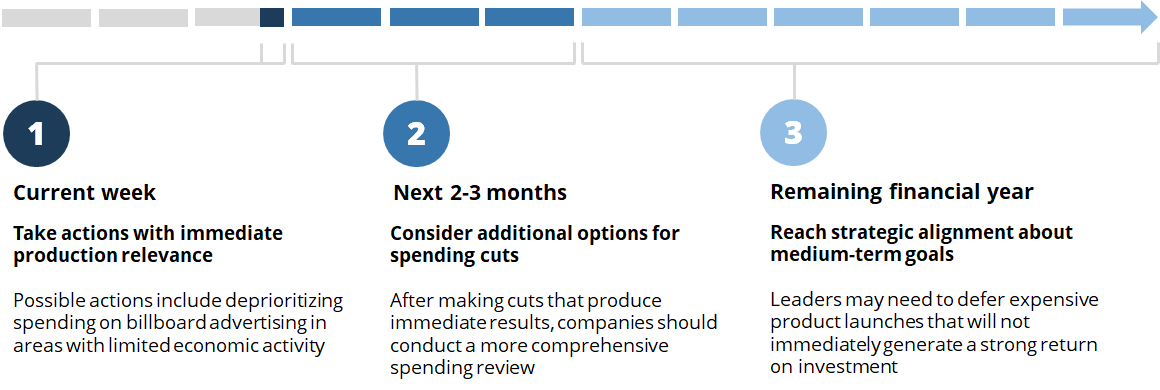
The impact of Coronavirus will continue to be felt for months to come, but the technology industry companies can move quickly to protect their employees, customers, and other members of their ecosystem.
About the authors
Cesar Reynoso is Office Managing Partner of MGO’s San Francisco office; Eric Harrison is a Managing Director in the San Jose Office; Eugene Ma is an Assurance Partner in the San Francisco Office, and Ashley Best is a Financial Analyst in the San Francisco Office.
In recent weeks, the global economy has entered uncharted territory. For the first time ever, many workers are under strict orders by state and local governments to ‘work from home if possible.’ For some firms this has not presented any issues, as they’ve had some employees work from home for years and mobile work capabilities are baked into the foundation of day to day activities. But many enterprises that did not previously have robust technology solutions to support a remote workforce, are now scrambling to establish adequate capabilities and protocols.
The silver-lining here is that any investments in remote capability are not only stop-gap measures. They represent a useful, long-term addition as employees are likely to expect remote capabilities moving forward – and are an essential disaster preparedness measure, in the event of another office site disruption.
To continue supporting firms navigating the trials of establishing remote capabilities, this piece of thought leadership examines one of the most common tools employed by companies to allow their staff to work remotely, the Virtual Private Network (VPN).
What is a VPN?
A VPN is a device that allows you to create a secure connection to another network over the Internet. In laymen’s terms, it will allow your employees to securely connect to your company resources over the open and unsecure internet. So this begs the question, how do you put a VPN into action to allow for remote access? In most cases it can be done by installing a simple device into your company’s server rack and then making sure all outside internet traffic is routed through the VPN. Setup of the device within your server room or closet requires technical knowledge of server wiring and network engineering.
If you do not have staff that meet the technical requirements, it is recommended that you reach out to an organization like MGO Technology Group, which has the expertise and technical staff needed to get a VPN racked and running in no time.
Identifying the “right fit’ VPN
Know that not all VPNs are created equally. While the market will provide any number of products that can meet your firm’s needs, not every product will be a fit. This is especially true in terms of capacity. When most companies consider a VPN solution, they typically look at how many staff members may need to work remotely on a regular basis. In the wake of a natural disaster such as the COVID-19 outbreak, your entire staff may need to work remotely for a sustained period of time. As such, it is important to factor the capacity of your VPN device into your decision making process. You may not need 100% of the VPN’s capacity most of the time, but you’ll be glad you have it when disaster hits.
It is also important that the outside internet connection you have into the VPN is adequate to handle the incoming traffic. You will need to work with your internet service provider to make sure the plan you choose has adequate bandwidth to handle the regular work activities of your staff. As with choosing and setting up the VPN, you are not alone in this endeavor. MGO Technology Group is ready to step in and help you make the choices you need for the uptime you desire.
Establishing VPN access
Once a VPN is installed, the next step is having your staff login into it in order to access company resources such as Exchange or FileShares. There are many different configurations a firm can employ to accomplish this task, but for now we’ll look at one of the more popular setups, VPN client software that is installed on company-owned laptops. Many VPN providers, such as CISCO or Check Point, offer VPN client endpoint software that you, your team, or your service provider can pre install into company laptops. This client endpoint software will automate the process of having your users connect to the VPN when they are outside of your office location. When installed and configured, an employee will only have to connect to the internet and then login to the client software to connect to the VPN.
The client software will also allow the user to connect to the VPN suing the same credentials that they use to login to their laptop thus eliminating the need to remember an additional password. By using client endpoint software the process of activating, using, and monitoring the VPN is simplified.
Understanding VPN vulnerabilities
As stated previously, the VPN will create a secure connection over the open internet back to your company resources. However, the VPN will not make everything secure. Like any device or setup, it has its vulnerabilities that must be acknowledged and mitigated. First and foremost, a VPN will not compensate for human error. While providing protection for the open and unsecure internet connection that an employee might use, it will not protect your employees from falling victim to a phishing scheme or downloading suspect software from a less than reputable website. Most VPNs are nothing more than a secure gateway into your company resources. Once that gateway is opened by a legitimate user, or a bad actor that has managed to steal legitimate credentials, anything can get through. Though a VPN secures the connection, it’s important that your employees still maintain good cyber hygiene by not sharing credentials, regularly changing passwords, and following the instructions of either your technical staff or managed service provider.
Though not as forward facing, but just as much of a threat are the vulnerabilities of the VPN device and software itself. Much like your company laptops and servers, VPN devices need to be properly maintained and updated less they become susceptible to newly discovered threats and vulnerabilities. This is where expertise comes into play. No matter how the VPN is deployed, you will need a technical team handling three distinct tasks after the VPN and associated software is put into place:
- They will need to train your users on how to properly use the VPN.
- They will need to make sure the both the VPN software and physical device remains secure.
- Finally, they will need to troubleshoot any issues that may come up from day to day operations. Even the most robust devices will require troubleshooting at some point.
Ready to talk VPNs and remote connectivity? MGO Technology Group is here to help. Let’s talk today.
]]>