- Cyber threats are increasingly elevating data and infrastructure risks for state and local governments. Proactive security standards and assessments can strengthen governmental defenses.
- Cyber Maturity Assessments (CMAs) evaluate preparedness to safeguard against, detect, isolate, and respond to system threats holistically across staff, procedures, and tools.
- Conducting a CMA can provide governments strategic advantages, such as: gauging risk management capabilities, fostering a security culture, mapping regulatory requirements, adapting to the evolving threat landscape, and informing cybersecurity strategies.
~
Cyber threats grow more sophisticated every day, increasing risks to sensitive data and critical services at the state and local level. With public-sector cyberattacks on the rise, today’s governments need to reinforce their cyber defenses to protect government operations and maintain constituent trust.
In the realm of cybersecurity, staying ahead of the curve is not just advisable; it’s imperative. In 2016, the Department of Defense (DoD) introduced a final rule amending the Defense Federal Acquisition Regulation Supplement (DFARS). This rule mandated new cybersecurity safeguards and cyber incident reporting for controlled unclassified information (CUI).
Transitioning from DFARS, the DoD has now developed the Cybersecurity Maturity Model Certification (CMMC), a framework designed to enhance the cybersecurity of government contractors. While state and local governments are not beholden to the CMMC, your team can still benefit from embracing CMMC standards and proactively developing comprehensive security programs.
5 Benefits of a Cyber Maturity Assessment for Your State or Local Government
To check your government against CMMC standards, a powerful tool you can employ is a Cyber Maturity Assessment (CMA) — which examines your organization’s overall preparedness to safeguard against, recognize, isolate, and react to cyber threats that could compromise sensitive data and systems. Analyzing more than just adherence to regulations, a CMA is a holistic analysis of people, processes, and tools that assesses the entity’s broader cyber risk exposure and defenses.
Here are five ways a CMA can be a trusted ally in fortifying your cybersecurity defenses:
1. Risk Management
The CMA framework addresses the crucial question: Is your organization equipped to navigate evolving risks effectively? With the assistance of CMA, state and local governments can gain insights into the maturity of their current processes and mechanisms. This empowers them to make informed decisions on risk mitigation strategies, ensuring a robust defense against emerging cyber threats.
2. Strengthening Security Culture
Promoting a culture of security and privacy by design is paramount in today’s digital landscape. CMA serves as a catalyst in fostering this mindset within organizations. By assessing the maturity of security practices, it enables state and local governments to identify areas for improvement, laying the foundation for a resilient security culture.
3. Understanding of Multiple Regulatory Requirements
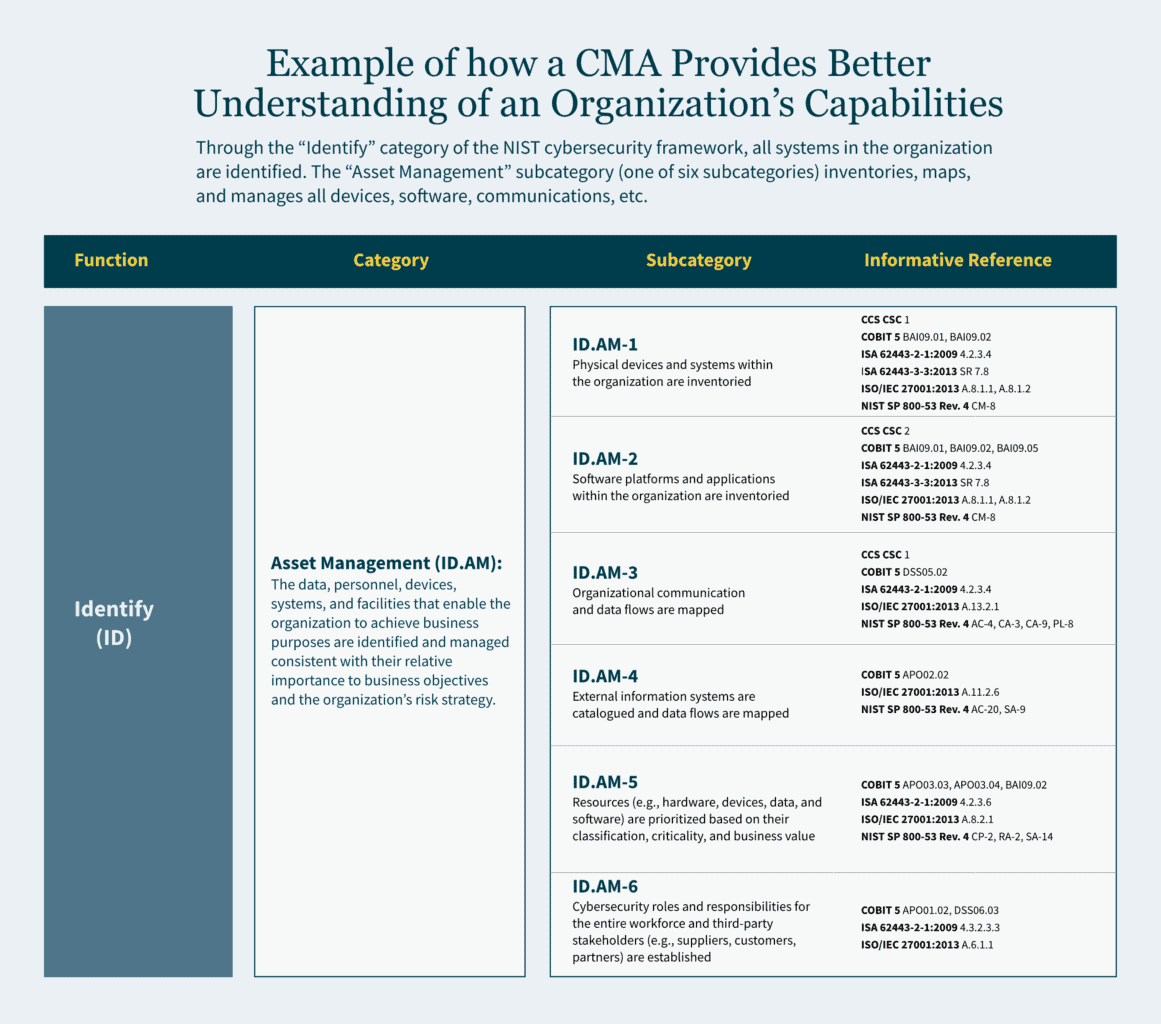
Navigating the complex web of regulatory requirements is a challenge for any government entity. CMA provides a comprehensive understanding of an organization’s capabilities to meet controls-based regulatory requirements. This not only ensures compliance but also establishes a framework for efficient regulatory adherence, minimizing vulnerabilities.
4. Proactiveness in an Ever-Evolving Cybersecurity Landscape
As cyber threats continue to grow in scale and sophistication, organizations must be proactive in adapting to the evolving landscape. CMA equips state and local governments with the foresight needed to stay ahead of cybercriminals. By identifying potential threats and vulnerabilities, organizations can implement strategies to drive growth and transformation while safeguarding their digital assets.
5. Determining Considerations for a Cybersecurity Strategy
Crafting an effective cybersecurity strategy requires a deep understanding of an organization’s capabilities and potential areas for improvement. CMA assists in identifying key considerations for a cybersecurity strategy, ensuring that state and local governments can rapidly adapt to the dynamic cybersecurity landscape.
Employing a Methodical Approach to CMA that Delivers Actionable Insights
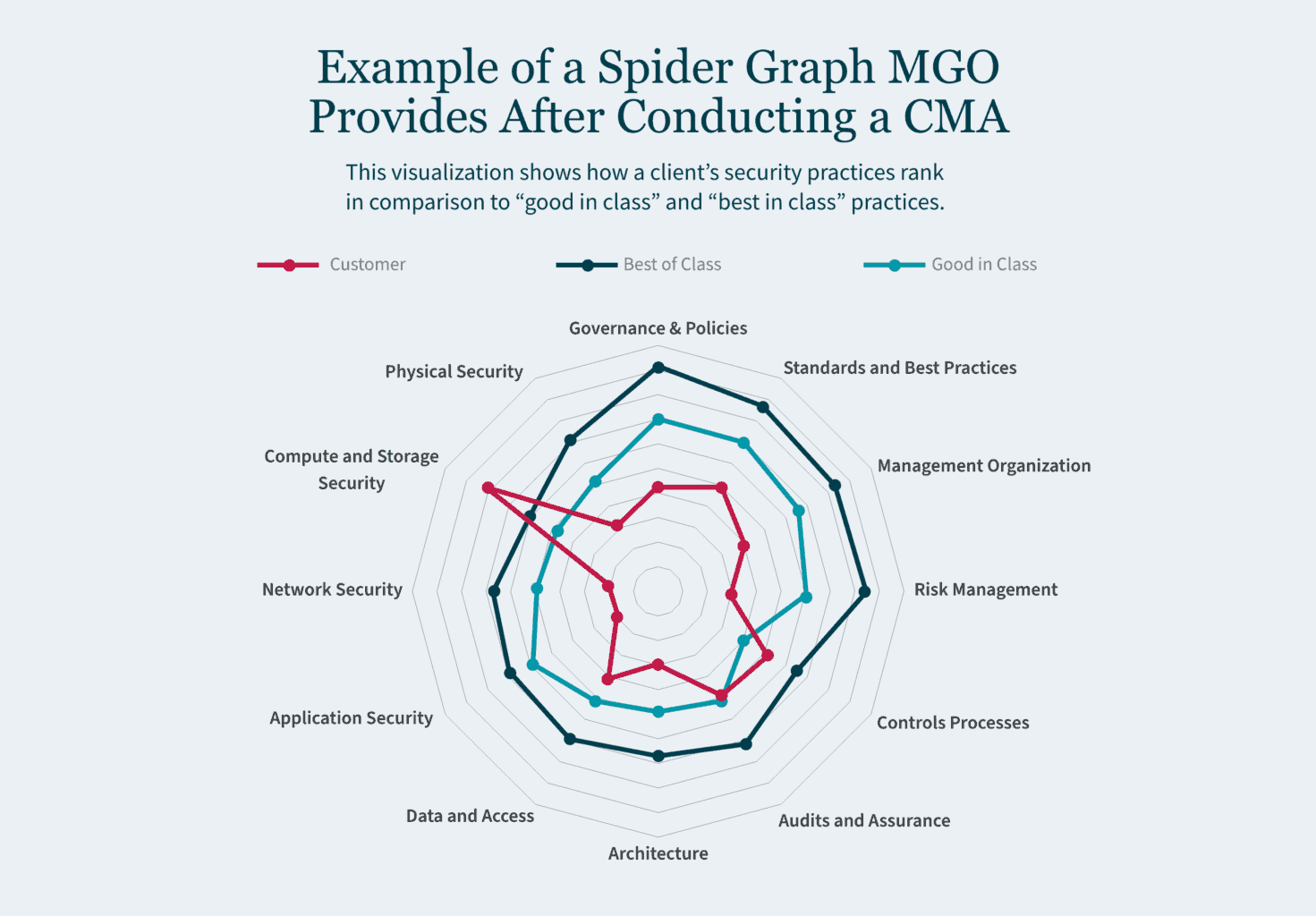
Conducting a productive CMA that yields meaningful insights requires experience with security frameworks and familiarity with the latest threat trends impacting state and local governments. At MGO, our Technology and Cybersecurity Advisory (TCA) team approaches each CMA engagement through a consistent methodology focused on mapping security practices to leading industry standards, evaluating core capability areas, and developing practical recommendations tailored to the organization.
Key elements of MGO’s CMA methodology include:
- Utilization of NIST Cybersecurity Framework (CSF), ISO 27001 or CIS Controls as a Baseline – The TCA team will help you identify current gaps in the security of information assets and determine potential opportunities for improvement relative to your organization’s size and stage in the lifecycle.
- Focus on Key Cybersecurity Capabilities – Emphasizing key cybersecurity capabilities including governance, detection, prevention, response and legal compliance, the TCA team will assist in aligning and mapping these capabilities against industry standards.
- Recommend Prioritized Areas of a Management Action Plan – The TCA team will assist you in identifying key areas of improvement and provide a risk-ranking to help prioritize moving forward.
- Maintaining Continuous Improvement – Instituting a recurring cycle of assessment and improvement is crucial, as cybersecurity maturity is a dynamic process that must adapt to evolving threats and business needs.
How We Can Help You Achieve Your Cybersecurity Goals
Our highly skilled team delivers in-depth cybersecurity and business knowledge that translates to outside-the-box thinking and practical recommendations. We will work with your team to conduct deep-dive walkthroughs and technical testing to help you manage potential cybersecurity issues. Reach out to MGO today to learn how our cybersecurity services can benefit your state or local government.
]]>Proactive planning is vital
State and local governments are frequently constrained by their budgets. Proactive planning spreads both effort and budget into a longer timeframe, which allows investments to be made incrementally and resources to be consistently allocated.
Because cyberattacks are nothing new, many organizations have already prepared some sort of response plan. However, because the pace of cyberattacks and the sophistication of hackers is constantly increasing, your plan should be updated at least annually. A robust plan is a living document that involves cross functional teams that include IT professionals and leadership.
Risks should be identified and prioritized so that urgent needs can be addressed with immediate investments. Although, the complete (or updated) plan may never be complete, the prioritized pieces of it will form a framework through which cybersecurity becomes an ongoing conversation, and a lens through which daily work is viewed.
Have a contingency plan: know who to contact and how
A contingency plan should be in writing. The process of drafting a detailed plan that addresses many different scenarios is time consuming, and it is also necessary. The thought process and discussions that go into thinking through a robust response to a cybersecurity plan are valuable to the whole organization. When a cyberattack occurs, one of the greatest concerns is to stop the loss of sensitive information. Part of contingency planning will involve creating an information classification policy, so your information systems protect the highest value information with the highest level of security.
Contingency planning also involves a communication plan. In what order do you make phone calls to your incident response team, legal counsel, board of directors, insurance agent, or law enforcement? Who needs to know what, when? How do you document your actions?
If you think having these discussions is overwhelming and stressful in the planning stage, imagine what it would be like to try to make critical decisions when your firewall is open, your information systems are locked, and your daily work has come to a halt.
Update your system to reduce risk
State and local governments often have older IT systems, some of which have been in use for 20 years. These systems require patches to prevent cybercrime, and in most cases, the various information systems do not “talk” to each other.
One of the first steps you can take is to update your information systems. Part of this may involve a discussion of a policy manual and potentially some training so that people are aware of the risks that are constantly evolving. A standing IT governance committee may initially be dedicated to the upgrade, and later take on the ongoing task of mitigating cyber risks throughout your organization.
Mitigating some of these risks might include reviewing your cyber insurance policies to ensure that you have adequate coverage for overall data recovery and the cost of business interruption. This committee should also review your backup policies and services to ensure reliable storage in a separate location that is tested periodically to ensure compliance with your contracts.
Prepare to respond to cyberattacks
State and local governments should expect to be targeted — they have access to large amounts of personal information and data. Thus, it is crucial to have a plan that can be immediately put into action to protect this sensitive information for the people and communities you serve. Your response within the first 24 hours of the breach is critical to minimizing damage. With proper planning, even an aggressive attack can be survived with minimal losses.
If your organization is not yet prepared for a cyberattack, or you are interested in proactive planning against a breach, schedule a consultation with the MGO Technology Group or learn more about the services we provide here.
]]>Giving state and local governments the resources to protect against hackers
The SLCIA updates the Homeland Security Act of 2002 to give the DHS leeway to utilize centers like the Cybersecurity and Infrastructure Security Agency (CISA) and Multi-State Information Sharing and Analysis Center (MS-ISAC). This will allow them to work with state, local, tribal, and territorial governments as needed, upon request.
This collaboration will encourage conducting cybersecurity exercises and hosting trainings meant to address current or future cyber risks or incidents. It will also provide operational and technical assistance to state and local governments to implement security resources, tools, and procedures to improve overall protection against attacks. The goal is to provide state and local governments with the support they need to defend themselves from hackers.
Resources to bolster government security capabilities
The SLCIA establishes a $500 million DHS grant program that will empower government institutions to increase their focus on cybersecurity. The bill also:
- Requires CISA to develop a strategy to improve cybersecurity of state, local, tribal, and territorial governments, enabling them to identify federal resources to capitalize on as well as set baseline objectives for their efforts;
- Indicates state, local, tribal, and territorial governments must develop a comprehensive cybersecurity plan to guide their usage of any grant money they receive;
- Establishes a state and local cybersecurity resiliency committee made up of representatives from state, local, tribal, and territorial governments to provide awareness of cybersecurity needs; and
- Enjoins CISA to assess the feasibility of a rotational program for the detail of approved government employees holding cyber positions.
The bill gives state and local governments the push they need to begin defending their networks. This can include the development of new strategies to boost their cybersecurity capabilities and acquisition of the funding needed to ensure their implementation. By investing in cybersecurity ahead of an attack, an entity is more likely to save money and protect its data.
Assessing eligibility for cybersecurity grants
Cybersecurity grants are available to municipalities of all sizes — but it’s important to start strategizing now by considering your IT infrastructure and cybersecurity frameworks. By applying for the grants, you indicate that you are taking your entity’s security seriously and taking the proper steps to qualify.
The State and Local Cybersecurity Improvement Act will provide up to $1 billion in grants for state, local, tribal, and territorial governments, allowing them to directly address their cybersecurity threats and risks. The program’s funding starts at $2 million for 2022, $400 million for 2023, $300 million for 2024, and $100 million for 2025.
To be eligible, an entity must:
- Maintain responsibility for monitoring, managing, and tracking its information systems, applications, and those user accounts owned and operated by the government;
- Show it has a process of continuously prioritizing the assessment of its cybersecurity vulnerabilities and threat mitigation practices; and
- Have a tangible plan that outlines:
- How to manage and audit network traffic.
- How the government plans to use the information to improve its systems’ resiliency and strength.
Our perspective
While the bill is still waiting on the Committee on Homeland Security and Governmental Affairs there are some things you can do to make sure you are ready. State and local governments should focus on building teams that can handle the grant application process — and be prepared to implement once awarded. This bill indicates that governments are past the point of merely updating a firewall or running a generic virus program — things like multifactor authentication and zero-trust architecture are viewed as the next steps (which was required for federal agencies in a 2021 executive order).
How we can help
Prior to starting the grant application process, your IT leaders should start thinking about how to handle security gaps with various procedures and consistent tests. MGO can help. Our Technology and Cybersecurity team can provide guidance as you prepare for the future.
About the authors
Francisco Colon is a Partner at MGO with extensive experience in external audit, fraud examinations, litigation support, operational and internal controls reviews, and buyer/seller due diligence. He specifically focuses on assisting organizations with evaluating and updating their internal controls with a focus on strategic alignment and fraud litigation deterrence management in a variety of industries, including tribal government, gaming, technology, cannabis, hospitality, government contracting, distribution, manufacturing, and private equity. Contact Francisco at FColon@mgocpa.com.
]]>Proactive planning is vital
State and local governments are frequently constrained by their budgets. Proactive planning spreads both effort and budget into a longer timeframe, which allows investments to be made incrementally and resources to be consistently allocated.
Because cyberattacks are nothing new, many organizations have already prepared some sort of response plan. However, because the pace of cyberattacks and the sophistication of hackers is constantly increasing, your plan should be updated at least annually. A robust plan is a living document that involves cross functional teams that include IT professionals and leadership.
Risks should be identified and prioritized so that urgent needs can be addressed with immediate investments. Although, the complete (or updated) plan may never be complete, the prioritized pieces of it will form a framework through which cybersecurity becomes an ongoing conversation, and a lens through which daily work is viewed.
Have a contingency plan: know who to contact and how
A contingency plan should be in writing. The process of drafting a detailed plan that addresses many different scenarios is time consuming, and it is also necessary. The thought process and discussions that go into thinking through a robust response to a cybersecurity plan are valuable to the whole organization. When a cyberattack occurs, one of the greatest concerns is to stop the loss of sensitive information. Part of contingency planning will involve creating an information classification policy, so your information systems protect the highest value information with the highest level of security.
Contingency planning also involves a communication plan. In what order do you make phone calls to your incident response team, legal counsel, board of directors, insurance agent, or law enforcement? Who needs to know what, when? How do you document your actions?
If you think having these discussions is overwhelming and stressful in the planning stage, imagine what it would be like to try to make critical decisions when your firewall is open, your information systems are locked, and your daily work has come to a halt.
Update your system to reduce risk
State and local governments often have older IT systems, some of which have been in use for 20 years. These systems require patches to prevent cybercrime, and in most cases, the various information systems do not “talk” to each other.
One of the first steps you can take is to update your information systems. Part of this may involve a discussion of a policy manual and potentially some training so that people are aware of the risks that are constantly evolving. A standing IT governance committee may initially be dedicated to the upgrade, and later take on the ongoing task of mitigating cyber risks throughout your organization.
Mitigating some of these risks might include reviewing your cyber insurance policies to ensure that you have adequate coverage for overall data recovery and the cost of business interruption. This committee should also review your backup policies and services to ensure reliable storage in a separate location that is tested periodically to ensure compliance with your contracts.
Prepare to respond to cyberattacks
State and local governments should expect to be targeted — they have access to large amounts of personal information and data. Thus, it is crucial to have a plan that can be immediately put into action to protect this sensitive information for the people and communities you serve. Your response within the first 24 hours of the breach is critical to minimizing damage. With proper planning, even an aggressive attack can be survived with minimal losses.
If your organization is not yet prepared for a cyberattack, or you are interested in proactive planning against a breach, schedule a consultation with the MGO Technology Group or learn more about the services we provide here.
Because organizations’ vulnerabilities are being actively exploited right now, it is crucial to see if this could affect your organization. Read more about the recommended actions to protect your security and reach out to MGO’s Johnny Mays with any questions.
Immediate defense actions recommended include:
- Ensure you are up to date on the latest patches and system updates
- Update your organization’s blocklist (e.g., if Fortinet is not used, don’t allow key aspects of it to run on your system)
- Ensure your backups are taking place—and they are stored air gapped separate from your live network
- Implement network segmentation to restrict a potential adversary’s ability for lateral movement
- Perform a user access review/permissions clean-up to ensure admin/elevated access privileges are restricted only to those who need them. Employ the principle of least privilege for all users in your organization. If a subject does not need an access right, they should not have that right (no extraneous access)
- Instate multi-factor authentication to stop attackers in their tracks
- Require strong passwords
- Limit remote desktop protocol (RDP) as much as possible. Disable it where it is not needed and monitor RDP access/activity logs.
- Secure remote access by avoiding the use of public Wi-fi and adding VPN for remote access
- Add an email banner to emails received from outside your organization to defend against phishing
- Provide security training
- Monitor/disable the ability to click on hyperlinks in unknown emails
Proactive planning is vital.
Having a defined plan allows your organization to react seamlessly, protecting your company’s assets, data, and activity. This means preparing proactively and practicing periodically to be ready to execute the plan when an attack comes.
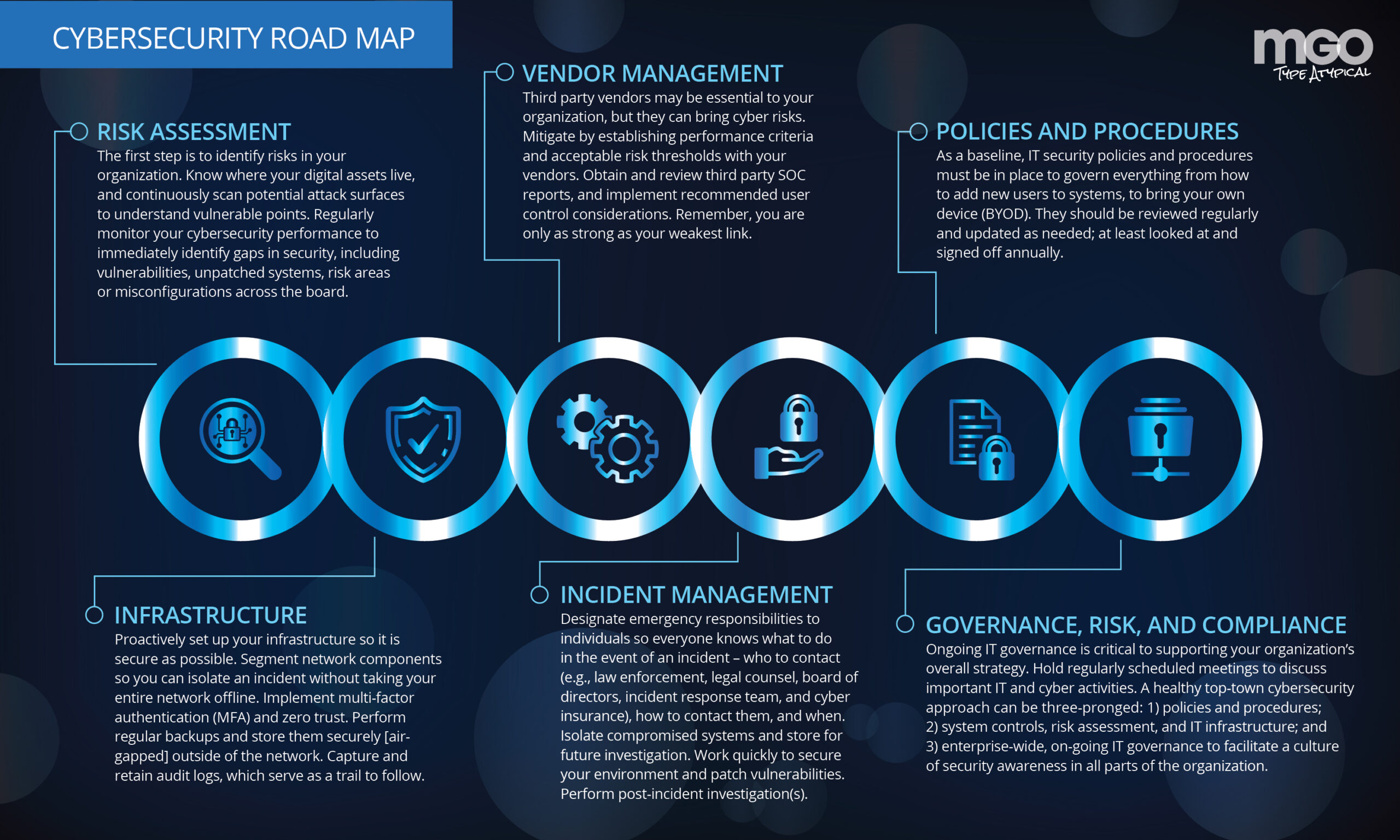
MGO has developed a roadmap to help organizations mitigate attacks within the first 24 hours of a breach. Instead of paying the ransom, ensure your company gets back to business after an attack. Understanding these top nine issues will prepare you to emerge unscathed after those first 24 hours.
1. Know who to contact — and how. When a cyberattack occurs, you will want to notify several groups within the first 24 hours: law enforcement, your legal counsel, the board of directors, incident response team, and cyber insurance. Think of them as your first line of defense in an emergency—you call them for help.
End users—individuals whose information or data is directly impacted—can be notified about the breach later, as there is a substantial amount of confidentiality involved. Businesses must avoid disclosing any weaknesses or exposures immediately following an attack.
2. Isolate and investigate.
Once you know which computers or systems have been affected, you want to isolate those involved and limit the damage. This way, you can utilize them for future investigation. By doing this, you can learn what went wrong, where your potential weak spots are, and how to avoid future mistakes. You want to move quickly to secure the systems and fix vulnerabilities — the only thing worse than one breach is multiple breaches. Remember to take all affected equipment offline and update your credentials so hackers cannot use the old ones to get back inside. Before completely shutting down any equipment, be sure you have surveyed the damage with a snapshot or copy the authorities can later review. An alternative to this is taking the affected equipment off the network to quarantine it—there will be no need to shut it down as it has been effectively partitioned from the rest of the network.
The designated incident response team will perform an immediate internal investigation upon isolation to determine the attack’s impact on critical business functions so the organization can jump into action to remediate. This team will also use their analysis to identify the attacker and discover other vulnerabilities where security can be tightened.
3. Implement manual procedures.
Before a breach, you want to define any manual, non-automatic procedures your team will need to implement during or after an attack. These procedures will allow for business “as usual” even during disruption. It is crucial to have these manual procedures in place already so that when the time arrives to use them, you know exactly what to do.
The implementation of these manual procedures must occur within the first 24 hours of the attack.
4. Contact your security service provider.
Work with your team of forensic experts. They will be able to determine if encryption was enabled at the time of the breach. They will analyze preserved data, review logs to see who had access to it and verify the compromised information. Your incident response team will also hand you forensic reports based on their findings, which you can use to take remedial measures.
5. Know your cyber insurance.
Review your cyber insurance regularly to make sure the policy provides the right level of coverage for your organization.
Generally, you want policies that support data recovery and cover the costs of business interruption.
6. Designate responsibility — ahead of time.
A cyberattack can cause chaos — it is designed to do so. It is crucial to designate responsibilities to different members of your cyber team so that everyone knows what is expected of them to bring the situation under control when a breach occurs. This will allow your organization to respond more seamlessly to the event.
7. Retain audit logs.
Audit logs provide a sort of breadcrumb trail to follow at an information systems level. (I’d discuss who is responsible for making sure these logs are functioning.) Ensure your audit logs are retained in the system so that you can respond within the first 24 hours of the breach. If you get attacked and do not have the audit logs, you probably won’t figure out what happened. This best practice generally suggests that logs should be retained for six months to a year.
8. Segment your network.
Setting up your network ahead of time to be segmented is essential because if a breach occurs on one server or site, it won’t lead to another breach. This allows you to isolate a breach and shut down one segment instead of taking the entire network offline. Your annual security assessment would be able to tell you if your segmentation plan was effective in containing the breach after the initial 24 hours.
9. Store backups — and back up daily at least.
The best way to recover from a ransomware attack is to have your backups ready to use. For this to be effective, your backups must be reliable; stored in a safe, separate place, and tested periodically to ensure that if something happens, you can bring the organization back online within those first 24 hours.
Be prepared for those first 24 hours.
Every organization should expect to be targeted, and all organizations need to have a plan of action to mitigate their risk when a cyberattack occurs. Because the first 24 hours of a breach are so crucial, the roadmap should be dedicated to helping operations protect themselves and prevent the attack from going to other areas of the organization. By preparing a plan, you will respond appropriately and get the company back on track with minimal lost revenue.
]]>As a large percentage of the US workforce transitions to work from home (WFH) situations due to the COVID-19 pandemic, we’ve looked at challenges that many organizations may face in setting up work from home (WFH) environments, as well as one of the most common tools used in making WFH resources available to your staff. Today, we’ll look at some of the best advice you, your IT team, or your managed service provider can provide your staff as they continue to work from home.
1. Turn on your corporate VPN, if provided, as soon as you login.
As stated in our previous article, the Virtual Private Network (VPN) is designed to make the connection between your employees and your corporate resources secure. Employees should get in the habit of activating the VPN as soon as their work or home laptops are turned on.
2. Change your password regularly
It is recommended that firms have a special procedure for incorporating password changes while employees are remote. For example, some setups require employees to be logged into the VPN before they initiate the password change on their own devices. Your employer’s technical staff or MSP should formalized the procedure and make it publicly available to you.
3. Avoid sharing your password
Sharing of passwords goes against almost everything we know about cybersecurity. However, in these times extraneous circumstances may require a transfer of passwords, especially in cases of troubleshooting. Try to avoid sharing your password, but if you must, follow these simple rules:
- ONLY share your password with a trusted source whose identity you can verify. This includes your local IT department or MSP. If you have any doubt about who you are sharing your password with, DO NOT SHARE IT. The inconvenience of not sharing your password is not worth the potential damage that could be caused by a data breach.
- ONLY share your password through a secure method. The safest is a phone call, but if you must use a messaging service, try to stick to simple SMS and do not use apps such as Facebook Messenger.
- As soon as the task requiring the password share is completed, change your password immediately. The longer this action is delayed the longer you and your firm are at risk.
4. Avoid letting other family members use your corporate laptop or devices.
It might be tempting to hand off your device to a family member for a simple task, but remember that in most cases you do not own your corporate devices and are liable for any damage or data leakage caused by your family members.
5. Be mindful of who is around you both virtually and in person.
Picture this scenario: You are on a call with someone in which confidential information is shared. A family member overhears and decides to share this information over their personal social media page for exposure, perhaps not understanding the confidential nature of this information. Suddenly you have a potential data breach of confidential information on your hands.
Though quarters might be tight, it’s important to be cognizant of who is around you at all times. This may include having discussions with family members so they understand that what might see or hear from you is confidential.
6. Remember that, in most cases, your work devices are not yours.
When you are issued a device, it usually comes the legal caveat that the device still belongs to the company along with anything that is introduced to that device. In most employment agreements the employer stipulates that they have the right to access, search, seize, and erase the device at any time. So if you have personal files and photos on any of your work devices, it would be prudent to move or back them up to a personal storage space.
7. Always listen to and follow the advice and notices of your IT staff.
As the COVID-19 situation progresses, new guidelines and rules may have to be developed. These should be communicated to you by your technical staff, HR personnel, or MSP. Assuming the source is verified, you should follow their guidance to the best of your abilities.
8. Never hesitate to ask questions of your IT staff if you are unsure of something.
In the realm of IT Security, there are no stupid questions. Your company has every interest in keeping you productive and safe. You can do your part by engaging with the IT staff or MSP through established channels. This can range from a critical system failure all the way down to reaching out to verify if new guidance you might have received did in fact come from the.
9. Consider how your family activities might affect available bandwidth in your home.
As you work from home, the strain on your home internet connection might become apparent as more devices are using the connection for longer periods of time. This will be especially true if you are home with other family members. You may notice lags on conference calls or the VPN taking longer to connect than usual.
While you can work with your internet service provider to see if you can increase the amount of bandwidth allocated to your house you may also want to consider network usability times with your family. This may be difficult, especially given the bandwidth resources needed for online school learning, but could be a necessary step in ensuring you have enough bandwidth during critical times such as video calls and high volume file transfers.
Ready to learn more? Join us for our up-coming webinar: Cultivating a Culture of Cybersecurity Awareness. Register here.
Or you can schedule a consultation with the MGO Technology Group here.
]]>The coronavirus probably has not hit its peak yet, but every facet of daily life has already been affected. Many companies are actively reaching out to their customers to ensure operations will continue under the best of circumstances and as government regulations allow. For many companies this means supporting a widely spread remote worforce.
As we are already in the midst of this crisis, the chance for your firm to proactively prepare for disrupted operations has passed, but this does not mean there is nothing that can be done. Thanks to the plethora of cloud-based processing options, it is still possible to fully secure resources for the majority of your staff to work remotely. It may be more expensive right now, but that is still a better alternative than shuttering operations entirely. For companies that have already gone remote, you have probably deployed your remote desktop connections, trained your staff on remote conferencing options, and made sure your phone data plans are paid up for any type of mobile device solution you choose to use. Now that these features are fully deployed, this is a great time to review them for potential cybersecurity risk factors.
As is the case with on premise work, cybersecurity has no ‘one size fits all’ solution for remote environments. Each company is going to be different and will require its own strategy to mitigate risk. However, there are some basic steps companies can take to ensure that their cyber risk is limited as much as possible during this time of remote work.
Risks of relying on public internet
The single largest risk factor for remote work is the public internet that is being used by your staff to access your company data, but there are some simple steps you can take to mitigate risk from the largely unsecured public internet.
First and foremost is the securing and monitoring of all connections into your infrastructure. Think of all connections to your data, from any location, as a phone call. A device calls into the physical location of your data to access it, process it, and possibly transfer it to another location, much as you would see with a phone call or fax machine. The key is to identify the various points from which these devices can ‘call into’ your physical infrastructure and then limit the number of devices that can actually make this call. Identifying and securing the remote access points of your company data or network infrastructure is most likely the easier of the these two tasks as in most circumstances you should have near full control over the physical space in which your data storage device resides.
Establishing a secure infrastructure
From here, the simplest and most effective means of protection is to erect a firewall to keep out unauthorized calls. Step two is to do as much as you can to secure the connections that you want to allow through the firewall. The simplest means to accomplish this is through a Virtual Private Network (VPN) that will not only provide verification of the authorized connections past your firewall, but will also create a secure tunnel by which the call into your data can travel.
The VPN will compensate for most security provisions your staff’s at home internet might or might not have. From there, you will need to look carefully at which devices you actually will allow in through your firewall. It would be prudent to direct your technical team or IT Vendor to create a list of approved devices that is as small as possible. You should limit approved devices to company issued laptops and mobile handsets. You can expand this list to employee owned devices, but this should only be done with the advent of a Mobile Device Manager (MDM) solution. While a VPN will compensate for an insecure connection, an MDM will compensate for the lack of cybersecurity protection an employee owned device may or may not have. At this point, you might be asking, where can I find VPNs, MDMs, etc. Thankfully there are plenty of businesses on the open market that have these tools, and even technical staff, setup and ready to deploy and are just waiting for a company like yours to engage them for assistance. By employing these two relatively simple steps, your company can create remote work infrastructure that will significantly cut down on the risks of employees working from home over the open internet.
Vigilant infrastructure maintenance
Now that we have looked at what infrastructure should be put in place, we next need to look at how to properly maintain the infrastructure. As with the technical tools listed above, the market has plenty of Managed Service Providers (MSPs), such as MGO Technology Group, that are ready to engage and provide you with the technical staff and tools your company will need to effectively continue operations during this crisis. Make no mistake about it, your remote work environment is going to require some form of troubleshooting, either in the form of equipment malfunction or staff training on how to properly use the tools mentioned above. This is where having a good level one (L1) IT support staff comes into play in your cybersecurity strategy. In order to properly mitigate the risks of data breach or leakage, your staff will need to correctly use the tools you have put into place. Never underestimate how far a well-trained and well-equipped IT support staff can go in correcting the human errors not caught by your VPNs, Firewalls, and MDMs.
Access professional guidance
In order to weather this crisis or any over further disruption your company might experience, you are going to need good equipment and knowledgeable people to install and maintain this equipment. Finding, maintaining, and retaining the equipment and staff can be a difficult and time consuming endeavor. As mentioned above, you may want to consider engaging with technical MSPs who have the training and resources in order to install and maintain the infrastructure your company will need to not only allow your employees to work from home, but to also switch back to working on premise as soon as the situation improves.
For more guidance or to schedule a consultation, contact us here.
]]>Emerging industries are prime candidates for cyberattacks and criminal hacking. That’s because as an industry matures companies quickly scale operations to meet the rising demand. With the focus on generating revenue, the implementation of appropriate security protocols is too often overlooked. A hallmark of a sophisticated and successful organization is robust cyber and information systems and processes that protect intellectual property, customer information, and other valuable data, or risk losing the market share you’ve fought so hard to win.
Cannabis faces nearly all of the same cyber security challenges of other industries of equivalent size and maturity. This includes, but is far from limited to, service disruptions through natural disasters, regulatory compliance, online based attacks, and especially offline based attacked such as phishing.
Understanding phishing attacks
Phishing holds a unique place in the cyber security sphere as unlike active attacks against a company’s information technology infrastructure, phishing seeks to gain access via user vulnerability. No matter how good your electronic defenses may be, a single well placed phishing scheme can compromise your data. This is why user education must be a part of any cybersecurity program and cannabis is no different. It does not matter if your cannabis operation is involved in cultivation, distribution, or retail. If your employees handle information that is important to your business they must be educated on best practices regarding phishing. The data your business holds is a valuable commodity and must be treated accordingly.
The emerging threat of ransomware
While phishing is the most common culprit of data breaches, ransomware has emerged as a less common, but just as threatening cyber risk. Ransomware is a type of attack that, rather than attempt to steal your data, will deny you access to it typically by encrypting your files. This will render your businesses inoperable until, in theory, you pay the ransom to your attacker to regain access to your data. Ransomware was prominent in the news in 2019 for various high profile attacks on mid-tier cites that simply did not have the financial resources to combat and undo the consequences of ransomware. Such a patterns is crucial for the cannabis industry to recognize. A result of these trends in 2019 shows us that ransomware attackers will often chose their victims carefully in the hope that the victim not have the willpower or resources to combat the attacker.
Since cannabis is a relatively new industry, with most resources dedicated to production development and company growth, most companies will not have the resources available to dedicate to combating ransomware attacks. Industry players should be aware of a simple fact of life when it comes to cyber security: prevention is always more cost-effective than recovery. Resources may be tight, but even a basic offsite data backup strategy could go a long way towards mitigating an attack that compromises data access.
IT asset inventory is a strong first step
This period of early growth is the perfect time for industry leaders and business owners to cultivate cyber security strategies. The relatively early-stage of the cannabis industry provides an opportunity in that companies are not unencumbered by legacy software and processes. Cyber security software and processes may not need to be stacked on or integrated into existing operations. Rather, it can be ‘backed into’ the company at an early stage. This will make the inevitable need to scale up cyber security operations within your company that much easier. It is also a good time to start your IT asset inventory processes, which will allow for a more robust IT security posture down the road. There are companies that have been around for decades that still do not have a handle on what equipment they actually have. In this regard, the cannabis industry has an advantage.
Smalls steps produce big results
The examples of phishing, ransomware, and asset management are just three core topics within the broader world of cyber security. While cyber security may seem to be a large, complex, and costly endeavor, even small and recently founded companies can effectively tackle the problems at hand. For example, as phishing constitutes the vast majority of data breach starting points, instituting a phishing awareness campaign at your company could go a long way towards reducing vulnerability to potential threats. Secondly, a small firm need not pay for real time data replication. Even a simple and cost-effective off-site backup can go a long way towards mitigating the effects of a ransomware attack. Sure, it might take longer to restore your data in the event of an emergency, but a slow restoration is better than none at all.
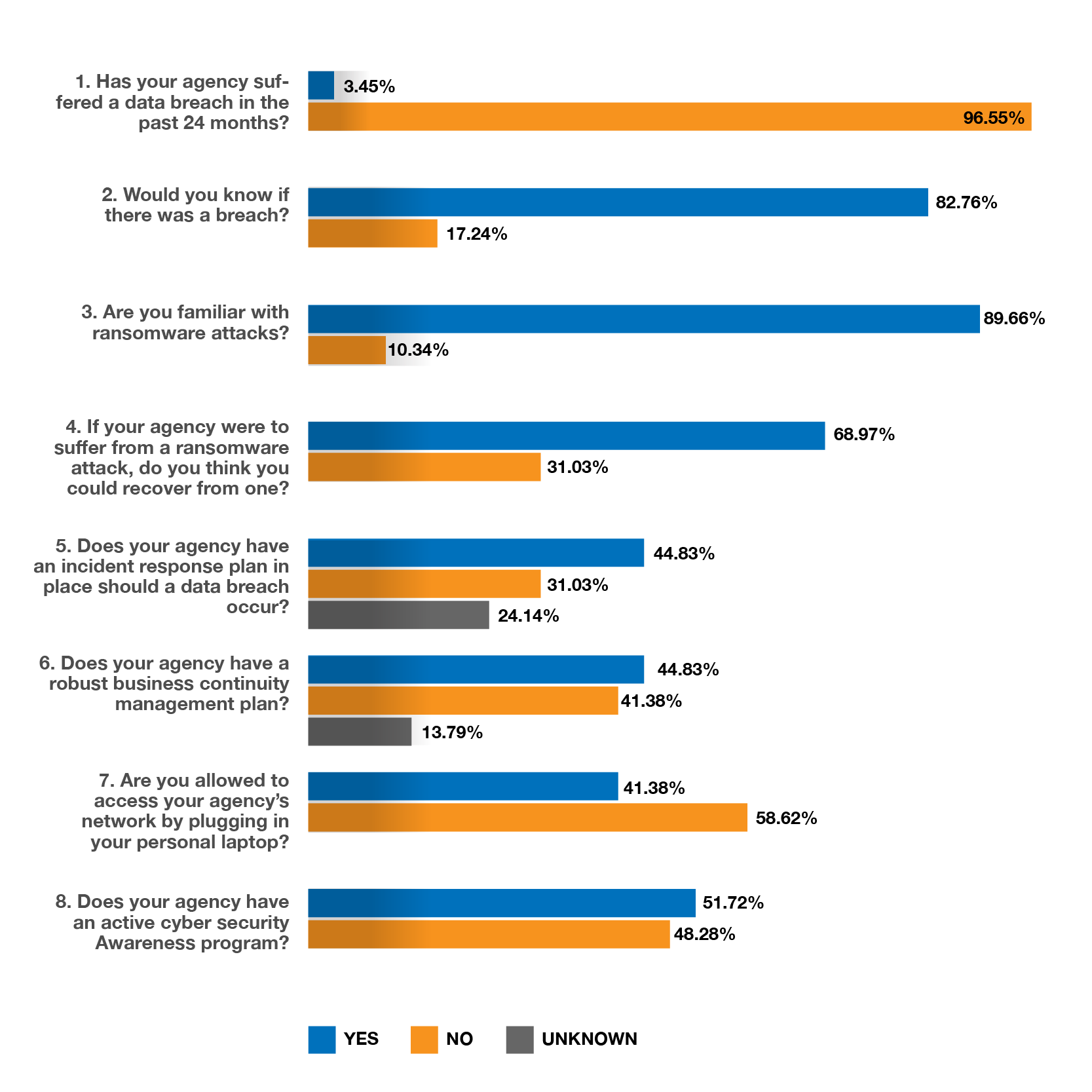
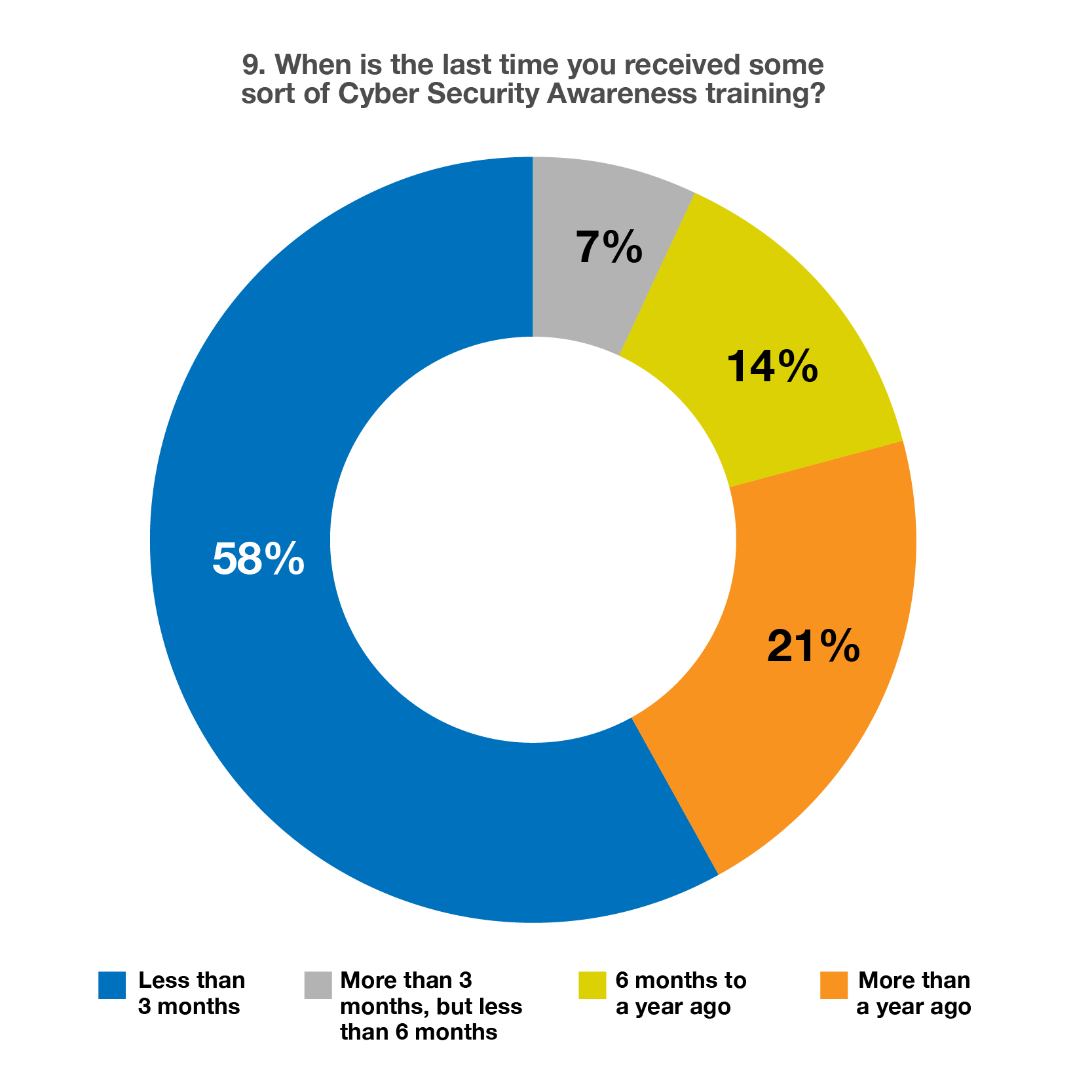
]]>The most interesting results from this survey indicate the majority of government agencies have NOT received Cyber Security Awareness training in the last year. This highlights an overwhelming need for the implementation of strong cyber security awareness programs in the government sector.
The results went on to show that barely half of the organizations have a cybersecurity awareness program in place at all, and of those that do, 58% haven’t received awareness training in over a year.
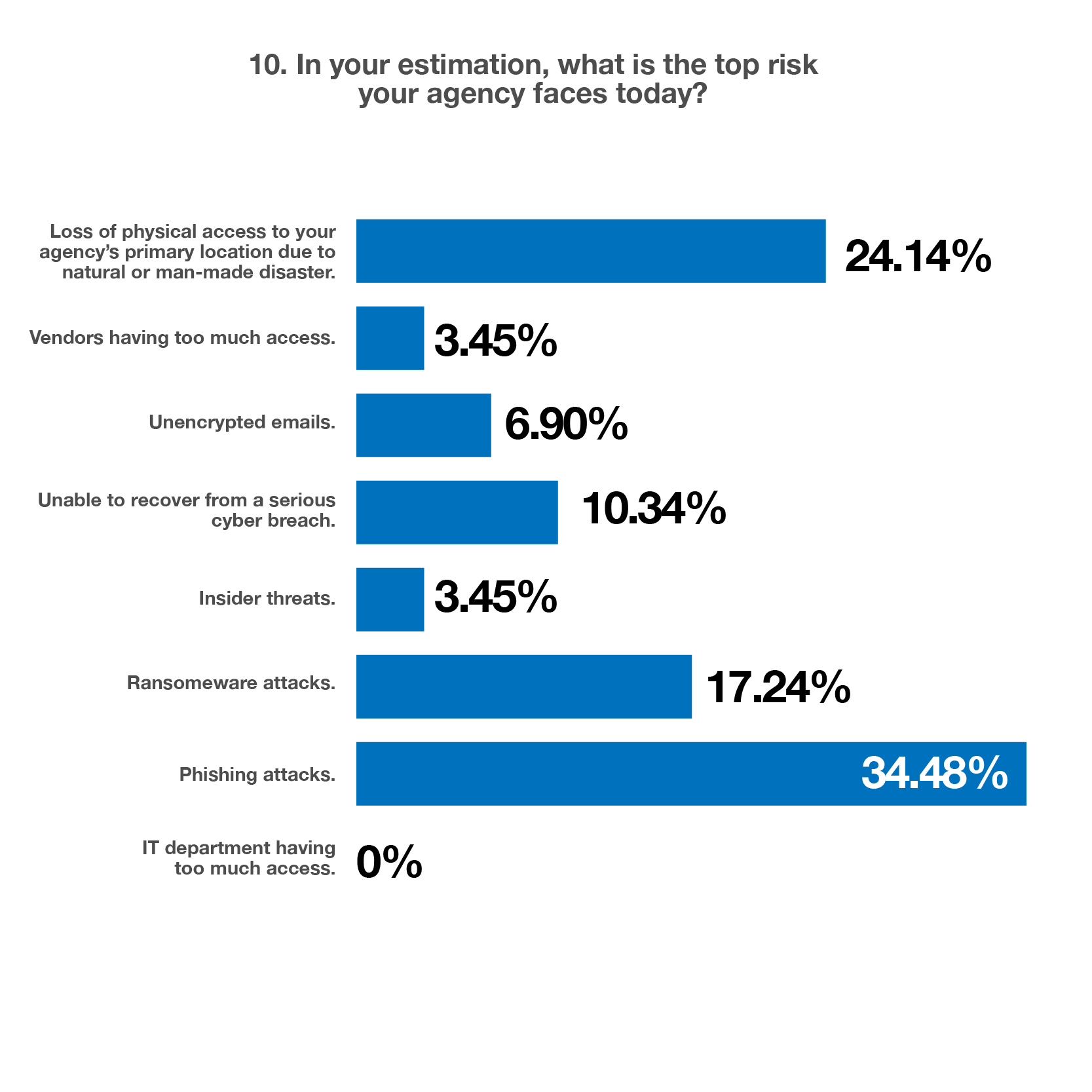
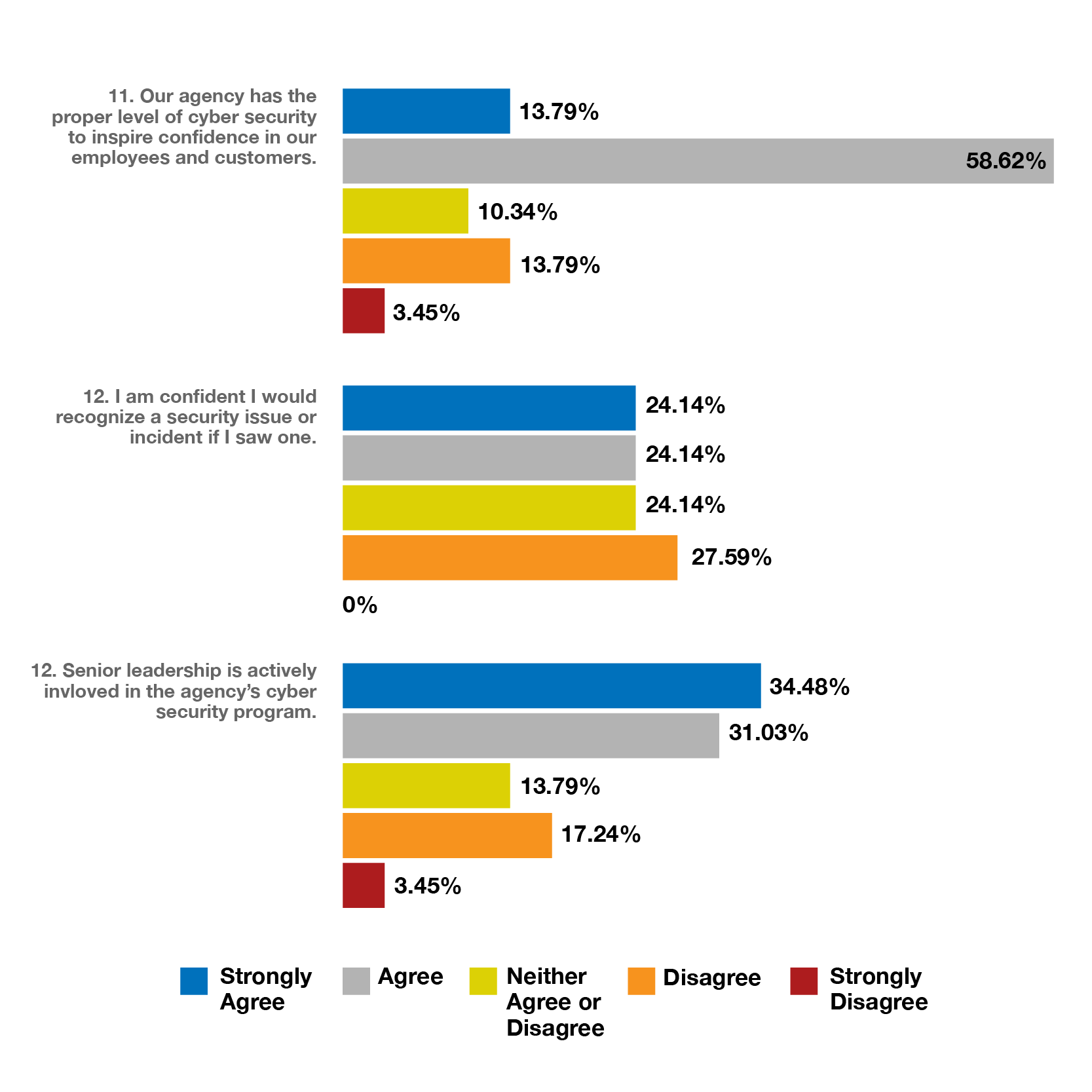
When asked to rate their top three risks agencies face today, your peers are mostly concerned about phishing and ransomware attacks at a combined percentage of 51.72%. It’s worth noting these risks can be significantly reduced when an awareness program is implemented. A lack of awareness is also evident with only half of those surveyed stating they would be able to recognize a security incident.
We’ve saved the most intriguing results for last. There’s actually enormous uncertainty about whether there is an Incident Response Plan, let alone any plan, in place to recover, should a breach occur. Communication across departments isn’t occurring.
Moreover, the majority of those polled tell us that senior leadership isn’t actively involved in agency cyber security programs.
As we welcome in the New Year why not commit some time on your calendar for more conversations and increased awareness about the business risks that face your city? Engage with the city leadership in identifying additional ways to increase the level of awareness for everyone.
We have a dedicated team of cyber and information security experts that can help you by creating a custom program – whatever the size of your organization – that will greatly improve your security posture. We can assist with security awareness programs, conduct threat assessments, review 3rd party vendor risks, or even create detailed Business Continuity and Incident Response Plans to transform your city into a cyber secure one. Let us partner with you in minimizing your vulnerabilities. What we can’t do is stop a cyber attack once it’s already been launched.